Over 100 Us And Eu Orgs Targeted In Strelastealer Malware Attacks

A new large-scale StrelaStealer malware campaign has impacted over a hundred organizations across the United States and Europe, attempting to steal email account credentials.
StrelaStealer was first documented in November 2022 as a new information-stealing malware that steals email account credentials from Outlook and Thunderbird.
One notable characteristic of the malware was using a polyglot file infection method to evade detection from security software.
At the time, StrelaStealer was seen targeting predominately Spanish-speaking users. However, according to a recent report by Palo Alto Networks’ Unit42, this has changed as the malware now targets people from the U.S. and Europe.
StrelaStealer is distributed through phishing campaigns that showed a significant uptick in November 2023, some days targeting over 250 organizations in the U.S.
The elevated phishing email distribution volumes continued into 2024, with a significant wave of activity being recorded by Unit42 analysts between late January and early February 2024.
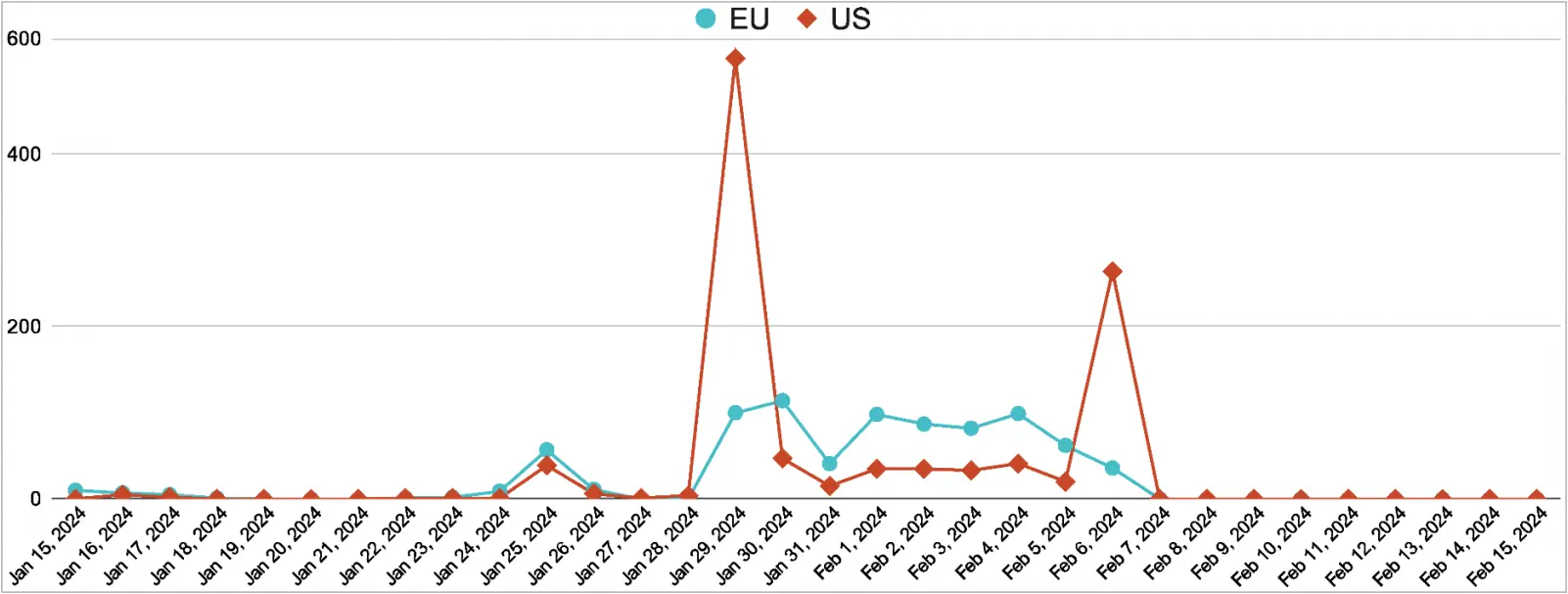
In some days during that period, the attacks in the U.S. surpassed 500, while Unit42 says it has confirmed at least 100 compromises in the country as well as Europe.
The malware operators used English and other European languages to adjust their attacks as needed.
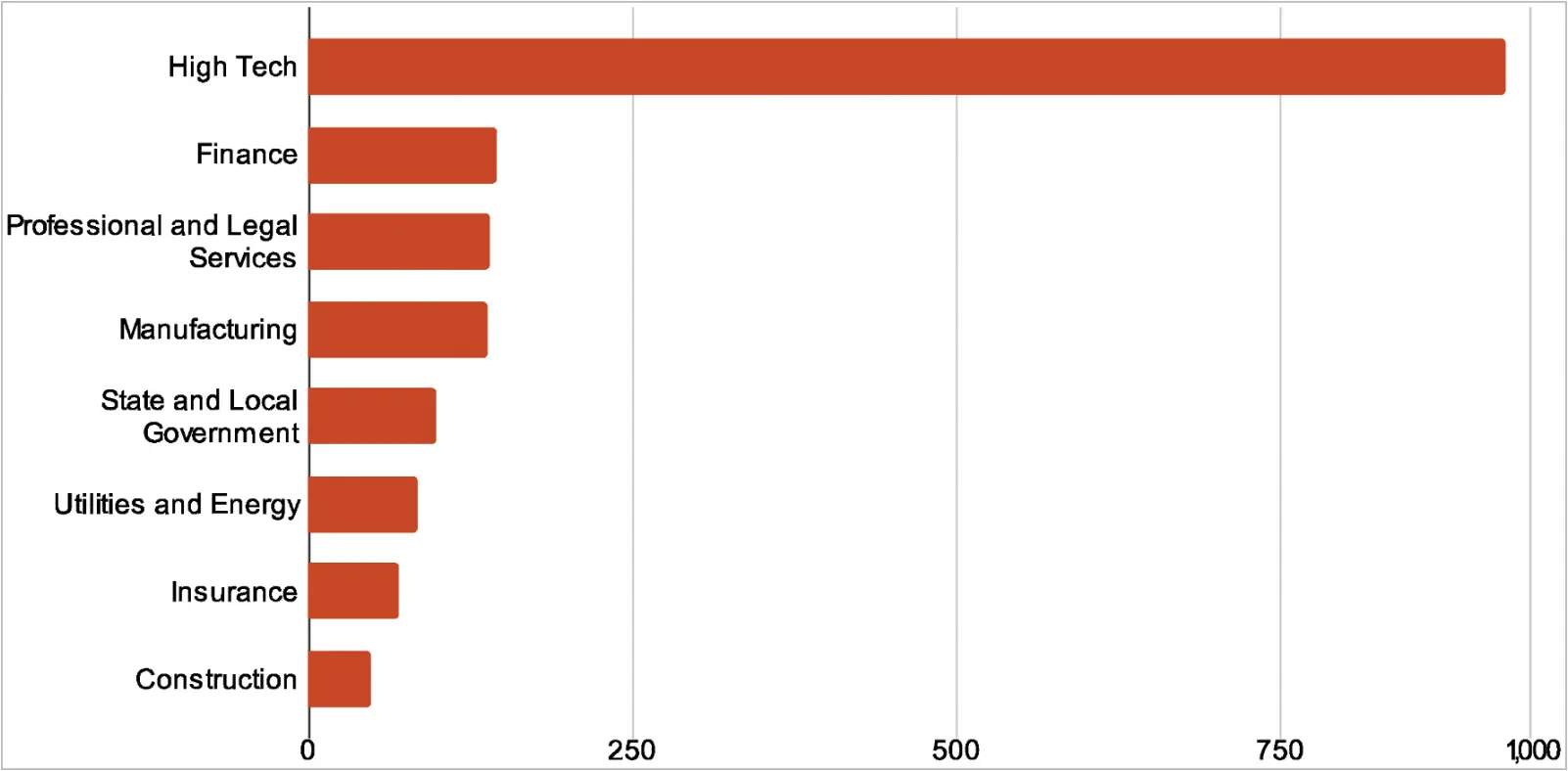
Most targeted entities operate in the ‘high tech’ space, followed by sectors like finance, legal services, manufacturing, government, utilities and energy, insurance, and construction.
New infection method
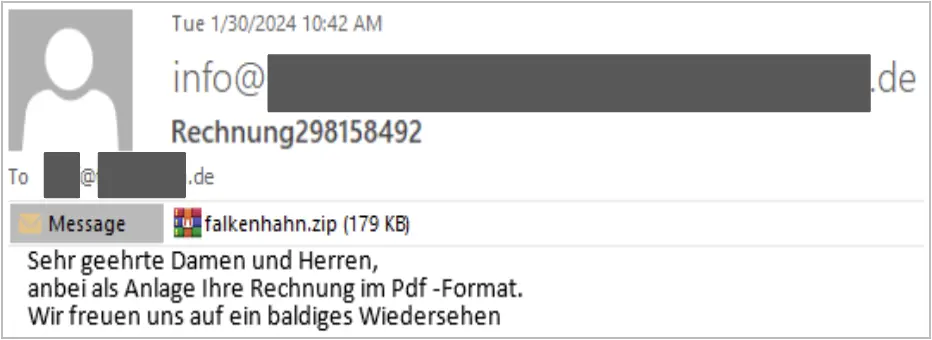
StrelaStealer’s original infection mechanisms from late 2022 have evolved, though the malware still uses malicious emails as the primary infection vector.
Previously, the emails attached .ISO files containing a .lnk shortcut and an HTML file, which utilized polyglotism to invoke ‘rundll32.exe’ and execute the malware payload.
The latest infection chain uses ZIP attachments to drop JScript files on the victim’s system. When executed, the scripts drop a batch file and a base64-encoded file that decodes into a DLL. That DLL is executed via rundll32.exe again to deploy the StrelaStealer payload.
Additionally, the newest version of the malware employs control flow obfuscation in its packing to complicate analysis and removes PDB strings to evade detection by tools relying on static signatures.
StrelaStealer’s primary function remains the same: to steal email login information from popular email clients and send it to the attackers’ command and control (C2) server.
Users should exercise vigilance when receiving unsolicited emails that purport to involve payments or invoices and refrain from downloading attachments from unknown senders.
