23andme Data Breach Hackers Stole Raw Genotype Data Health Reports

Genetic testing provider 23andMe confirmed that hackers stole health reports and raw genotype data of customers affected by a credential stuffing attack that went unnoticed for five months, from April 29 to September 27.
The credentials used by the attackers to breach the customers’ accounts were stolen in other data breaches or used on previously compromised online platforms.
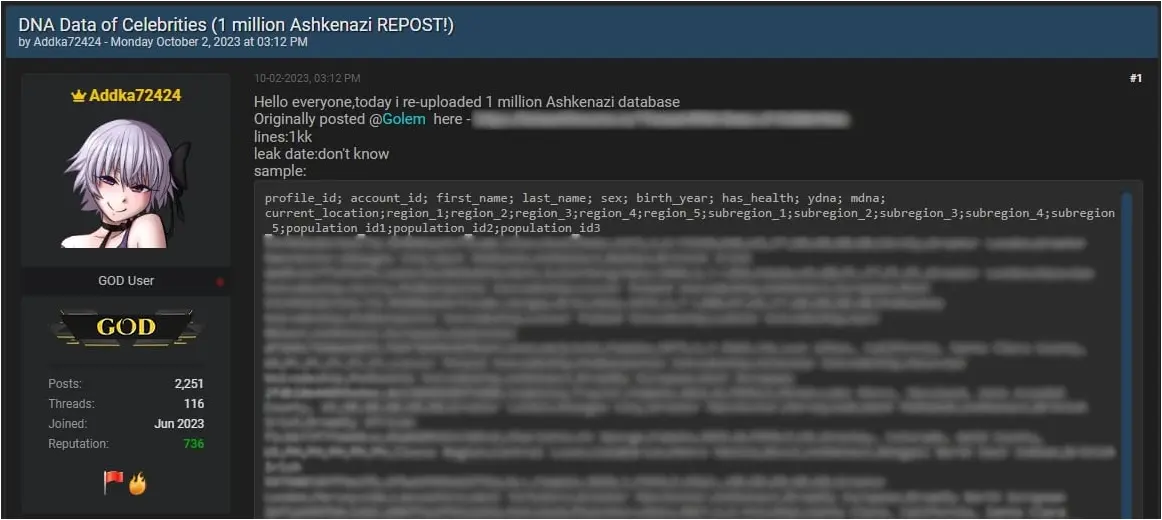
As the genomics and biotechnology company disclosed in data breach notification letters sent to those impacted in the incident, some of the stolen data was posted on the BreachForums hacking forum and the unofficial 23andMe subreddit site.
The leaked information includes the data for 1 million Ashkenazi Jews and 4.1 million people living in the United Kingdom.
“Our investigation determined the threat actor downloaded or accessed your uninterrupted raw genotype data, and may have accessed other sensitive information in your account, such as certain health reports derived from the processing of your genetic information, including health-predisposition reports, wellness reports, and carrier status reports,” 23andMe revealed.
“To the extent your account contained such information, the threat actor may have also accessed self-reported health condition information, and information in your settings.”
For customers who also used 23andMe’s DNA Relatives feature, it is possible that the attackers also scraped their DNA Relatives and Family Tree profile information.
They may have also gained visibility to affected customers’ following information if shared via the DNA Relatives feature:
- Ancestry reports and matching DNA segments (specifically where on your chromosomes you and your relative had matching DNA),
- Self-reported location (city/zip code),
- Ancestor birth locations and family names,
- Profile picture, birth year, and anything else included in their profile’s “Introduce yourself” section
23andMe told BleepingComputer in December that the hackers downloaded the data of 6.9 million people of the existing 14 million customers after breaching around 14,000 user accounts.
5.5 million individuals had their data scraped through the DNA Relatives feature and 1.4 million via the Family Tree feature.
On October 10, roughly one week after detecting the attack, 23andMe started requiring all customers to reset their passwords.
Since November 6, all new and existing customers must use two-factor authentication when logging into their accounts to block future credential-stuffing attempts.
Last year’s incident also resulted in multiple lawsuits being filed against 23andMe, causing the company to update its Terms of Use on November 30 with provisions that make it harder for customers to join class action lawsuits against 23andMe.
“To the fullest extent allowed by applicable law, you and we agree that each party may bring disputes against the other party only in an individual capacity, and not as a class action or collective action or class arbitration,” reads one of the updates.
However, 23andMe said these changes were added to make the arbitration process more efficient and easier for customers to understand.
