52% of Serious Vulnerabilities We Find are Related to Windows 10
We analyzed 2,5 million vulnerabilities we discovered in our customer’s assets. This is what we found.
Digging into the data
The dataset we analyze here is representative of a subset of clients that subscribe to our vulnerability scanning services. Assets scanned include those reachable across the Internet, as well as those present on internal networks. The data includes findings for network equipment, desktops, web servers, database servers, and even the odd document printer or scanning device.
The number of organizations in this dataset is smaller (3 less) than the previous dataset used in last year’s Security Navigator 2023 and some organizations were replaced by new additions. With the change of organizations comes a different mix of assets, which leaves comparing the previous results akin to comparing apples to oranges (we might be biased), but it’s still worth noting similar patterns where possible.
This year, we revisit the menacing vulnerability theme with an eye on the ever-present and lingering tail of unresolved system weaknesses. The waves of newly discovered serious issues are just for our attention with existing unresolved issues, seeming like a hydra that keeps on growing new snaking heads as soon as you dispatch others.
Assessing whether a system is adequately protected is a challenge that requires skill and expertise and can take a lot of time. But we want to learn of any weaknesses beforehand rather than having to deal with the fallout of an unplanned “free pentest” by a random Cy-X group.
Security Navigator 2024 is Here – Download Now#
The newly released Security Navigator 2024 offers critical insights into current digital threats, documenting 129,395 incidents and 25,076 confirmed breaches. More than just a report, it serves as a guide to navigating a safer digital landscape.
What’s Inside?#
- 📈 In-Depth Analysis: Explore trends, attack patterns, and predictions. Learn from case studies in CyberSOC and Pentesting.
- 🔮 Future-Ready: Equip yourself with our security predictions and research summary.
- 👁️ Real-Time Data: From Dark Net surveillance to industry-specific statistics.
Stay one step ahead in cybersecurity. Your essential guide awaits!
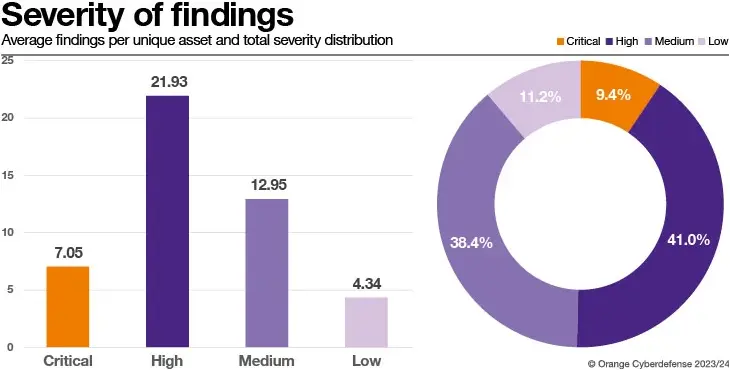
Vulnerability Scanning Findings by Severity
Examining the severity rating share per unique Finding we see that the bulk of unique Findings, 79%, are classified as ‘High’ or ‘Medium’. However, it is also worth noting that half, 50.4%, of unique Findings are considered ‘Critical’ or ‘High.’
The average number of ‘Critical’ or ‘High’ Findings has decreased by 52.17% and 43.83%, respectively, compared to our previously published results. An improvement can also be observed for Findings with severity ratings ‘Medium’ and ‘Low’ being down 29.92% and 28.76%. As this report uses a slightly different sample of clients to last year, a YoY comparison has limited value, but we see evidence that clients are responding well to the findings we report, resulting in an overall improvement.
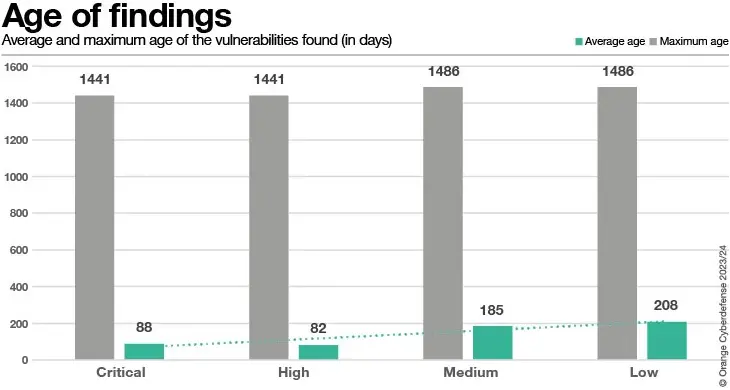
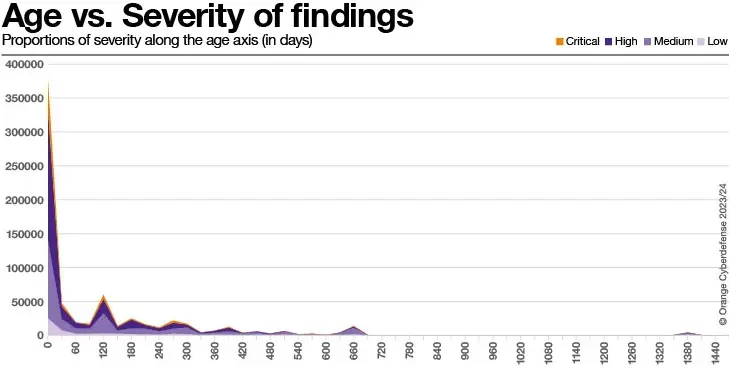
The majority of Findings (78%) rated ‘Critical’ or ‘High’ are 30 days or younger (when looking at a 120-day window). Conversely, 18% of all findings rated ‘Critical’ or ‘High’ are 150-days or older. From a prioritization perspective, ‘Critical’ or ‘High’ real findings seem to be dealt with swiftly, but some residual still accumulates over time. We see, therefore, that unresolved Findings continue to grow older. Indeed, ~35% of all unique CVEs are from findings 120 days or older.
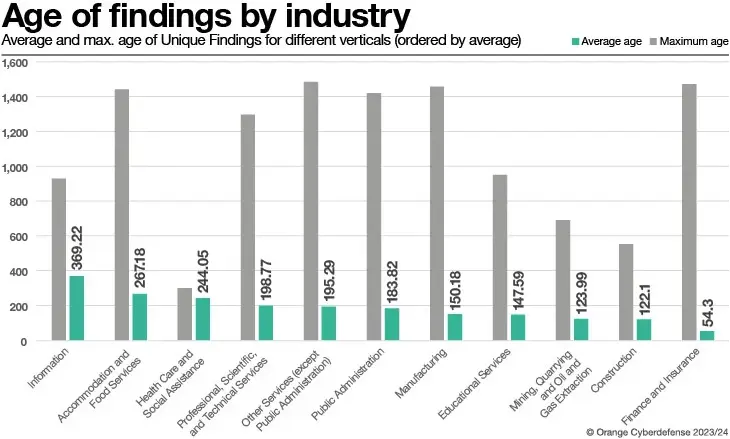
The chart above shows the long tail of unresolved real findings. Note the first remarkable long tail peak around 660 days and the second one at 1380 days (3 years and 10 months).
A window of opportunity
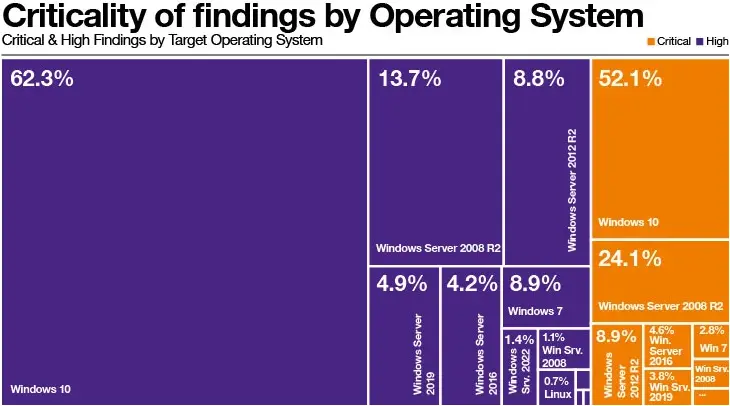
The high average numbers of ‘Critical’ and ‘High’ findings are largely influenced by assets running Microsoft Windows or Microsoft Windows Server operating systems. Assets running operating systems other than Microsoft, such as Linux-based OS, are present, but these are reported proportionally far less.
We should note, however, that the ‘Critical’ or ‘High’ findings associated with assets running Windows are not necessarily vulnerabilities in the operating system but can also be related to applications running on the asset.
It is perhaps understandable that unsupported Microsoft Windows and Windows Server versions are prominent here, but it is surprising to find more recent versions of these operating systems with severities rated as ‘Critical’ or ‘High’.
Industry perspective
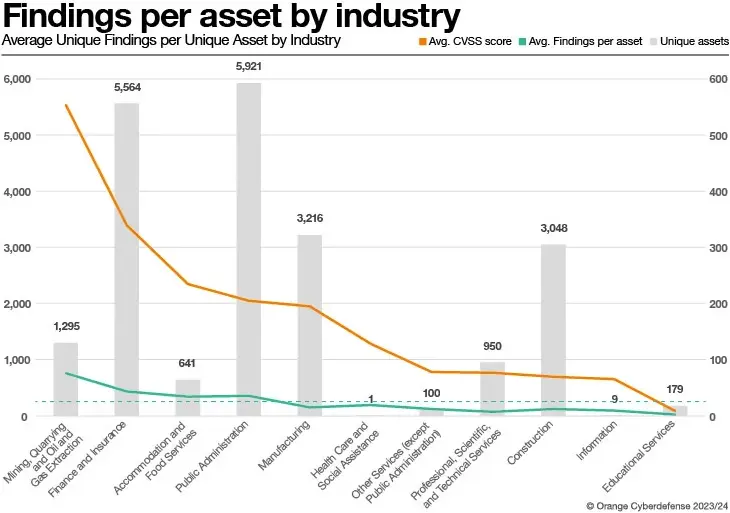
We are using NAICS for our industry classification. The results here only consider Findings based on scans of hosts rather than services such as web applications. The average unique real Finding per unique asset is 31.74 across all organizations, denoted by the dashed horizontal line in the chart below.
Our clients in the Construction industry appear to be performing exceptionally well compared to clients in other industries, with an average of 12.12 Findings per Asset. At the opposite end of the spectrum, we have the Mining, Quarrying, and Oil and Gas industries, where we report an average of 76.25 unique findings per asset. Clients in Public Administration surprised us by outperforming Finance and Insurance with an average of 35.3 Findings per Asset, compared with 43.27, despite the larger number of Assets. Of course, these values are derived from the set of clients present in our sample and may not represent the universal reality.
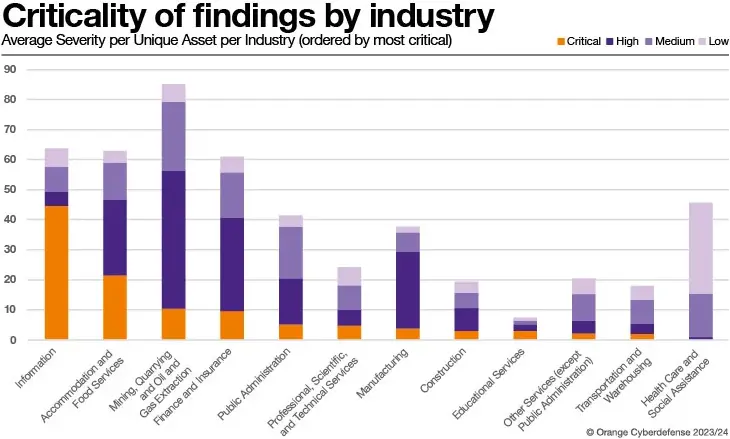
When comparing the average severity per unique asset per Industry, we see a mixed picture. We can ignore Health Care and Social Assistance and Information, with a relatively small unique asset count, that results in averages that are disproportionate in relation to other Industries.
Our overall Industry average for Severity rating High is 21.93 and Mining, Quarrying and Oil and Gas Extraction have more than double that average.
Similarly, Finance and Insurance with Accommodation and Food Services also overshot the overall average by 10.2 and 3.4 findings per unique asset, respectively. The same three Industries exceeded the overall average for findings rated Critical, with Accommodation and Food Servers doing so by almost a factor of 3.
Vulnerability is getting old
As we revisit the menacing vulnerability theme this year, we once again look suspiciously at the ever-present and lingering tale of unresolved system weaknesses that are just getting older. We assessed over 2.5m vulnerability findings that we reported to our clients and over 1,500 reports from our professional ethical hackers to understand the current state of security vulnerabilities and consider their role and effectiveness as a tool for prioritization.
The bulk of unique Findings reported by our scanning teams – 79% – are classified as ‘High’ or ‘Medium,’ and 18% of all serious findings are 150 days or older. Though these are generally dealt with more swiftly than others, some residuals still accumulate over time. While most findings we identify are resolved after 90 days, 35% of all findings we report persist for 120 days or longer. And way too many are never addressed at all.
Our scanning results illuminate the persistent problem of unpatched vulnerabilities. Meanwhile, our Ethical Hacking teams more frequently encounter newer applications and systems built on contemporary platforms, frameworks, and languages.
The role of the Ethical Hacker is to conduct Penetration Tests – to emulate a malicious attacker and assess a system, application, device, or even people for vulnerabilities that could be used to gain access or deny access to IT resources.
Penetration Testing is generally considered a component of Vulnerability Management but could also be seen as a form of Threat Intelligence that businesses should leverage as part of their proactive defense strategy.
17.67% of findings our Ethical Hackers reported were rated as ‘Serious’, but, on a brighter note, hackers must work harder today to discover them than they had to in the past.
This is just an excerpt of the analysis. More details on our analysis of vulnerabilities and Pentesting (as well as a ton of other interesting research topics like VERIS categorization of the incidents handled in our CyberSOCs, Cyber Extortion statistics and an analysis of Hacktivism) can be found in the Security Navigator. Just fill in the form and get your download. It’s worth it!
Note: This informative piece has been expertly crafted and generously shared by Charl van der Walt, Head of the Security Research Center, Orange Cyberdefense.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.