Malicious NPM Packages Target Roblox Users with Data-Stealing Malware
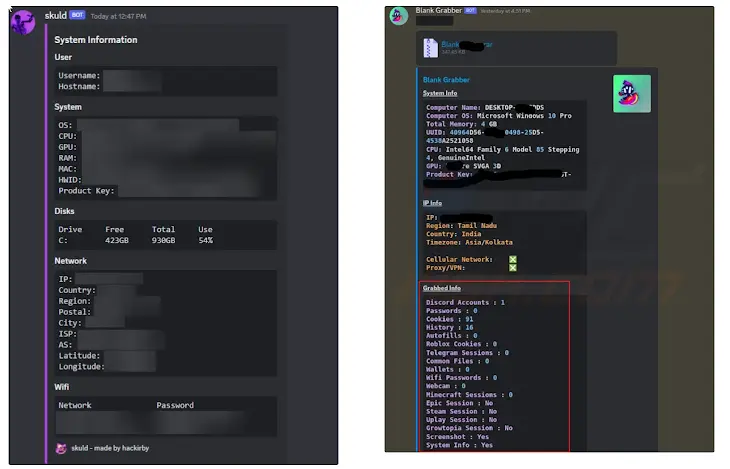
A new campaign has targeted the npm package repository with malicious JavaScript libraries that are designed to infect Roblox users with open-source stealer malware such as Skuld and Blank-Grabber.
“This incident highlights the alarming ease with which threat actors can launch supply chain attacks by exploiting trust and human error within the open source ecosystem, and using readily available commodity malware, public platforms like GitHub for hosting malicious executables, and communication channels like Discord and Telegram for C2 operations to bypass traditional security measures,” Socket security researcher Kirill Boychenko said in a report shared with The Hacker News.
The list of malicious packages is as follows –
- node-dlls (77 downloads)
- ro.dll (74 downloads)
- autoadv (66 downloads)
- rolimons-api (107 downloads)
It’s worth pointing out that “node-dlls” is an attempt on part of the threat actor to masquerade as the legitimate node-dll package, which offers a doubly linked list implementation for JavaScript. Similarly, rolimons-api is a deceptive variant of Rolimon’s API.
“While there are unofficial wrappers and modules — such as the rolimons Python package (downloaded over 17,000 times) and the Rolimons Lua module on GitHub — the malicious rolimons-api packages sought to exploit developers’ trust in familiar names,” Boychenko noted.
The rogue packages incorporate obfuscated code that downloads and executes Skuld and Blank Grabber, stealer malware families written in Golang and Python, respectively, that are capable of harvesting a wide range of information from infected systems. The captured data is then exfiltrated to the attacker via Discord webhook or Telegram.
In a further attempt to bypass security protections, the malware binaries are retrieved from a GitHub repository (“github[.]com/zvydev/code/”) controlled by the threat actor.
Roblox’s popularity in recent years has led to threat actors actively pushing bogus packages to target both developers and users. Earlier this year, several malicious packages like noblox.js-proxy-server, noblox-ts, and noblox.js-async were discovered impersonating the popular noblox.js library.
With bad actors exploiting the trust with widely-used packages to push typosquatted packages, developers are advised to verify package names and scrutinize source code prior to downloading them.
“As open-source ecosystems grow and more developers rely on shared code, the attack surface expands, with threat actors looking for more opportunities to infiltrate malicious code,” Boychenko said. “This incident emphasizes the need for heightened awareness and robust security practices among developers.”
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.



![[HUNTERS] - Ransomware Victim: Amourgis & Associates 4 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)
![Cobalt Strike Beacon Detected - 156[.]238[.]227[.]43:80 8 Cobalt Strike](https://www.redpacketsecurity.com/wp-content/uploads/2021/11/Cobalt-Strike-300x201.jpg)