Experts Warn of ‘Ice Breaker’ Cyberattacks Targeting Gaming and Gambling Industry
A new attack campaign has been targeting the gaming and gambling sectors since at least September 2022, just as the ICE London 2023 gaming industry trade fair event is scheduled to kick off next week.
Israeli cybersecurity company Security Joes is tracking the activity cluster under the name Ice Breaker, stating the intrusions employ clever social engineering tactics to deploy a JavaScript backdoor.
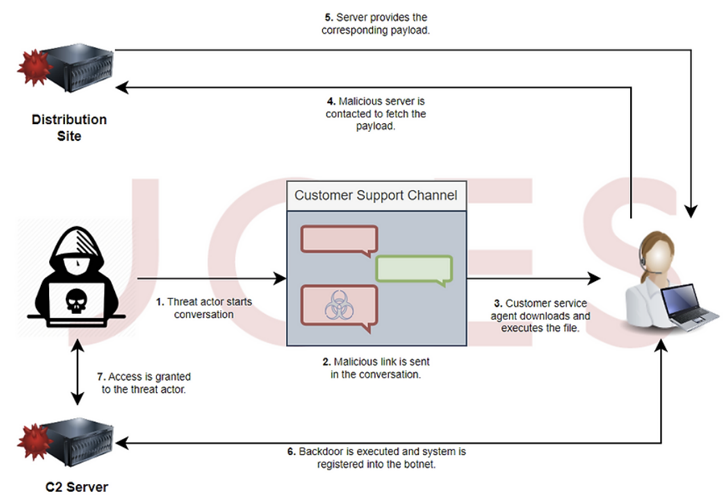
The attack sequence proceeds as follows: The threat actor poses as a customer while initiating a conversation with a support agent of a gaming company under the pretext of having account registration issues. The adversary then urges the individual on the other end to open a screenshot image hosted on Dropbox.
Security Joes said that the threat actor is “well-aware of the fact that the customer service is human-operated.”
Clicking the purported screenshot link sent in the chat leads to the retrieval of an LNK payload or, alternatively, a VBScript file as a backup option, the former of which is configured to download and run an MSI package containing a Node.js implant.
The JavaScript file has all the features of a typical backdoor, enabling the threat actor to enumerate running processes, steal passwords and cookies, exfiltrate arbitrary files, take screenshots, run VBScript imported from a remote server, and even open a reverse proxy on the compromised host.
Should the VBS downloader be executed by the victim, the infection culminates in the deployment of Houdini, a VBS-based remote access trojan that dates back to 2013.
The threat actors’ origins are currently unknown, although they have been observed using broken English during their conversations with customer service agents. Some indicators of compromise (IoCs) associated with the campaign were previously shared by the MalwareHunterTeam in October 2022.
“This is a highly effective attack vector for the gaming and gambling industry,” Felipe Duarte, senior threat researcher at Security Joes, said.
“The never-seen-before compiled JavaScript second stage malware is highly complex to dissect, showing that we are dealing with a skilled threat actor with the potential of being sponsored by an interest owner.”
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on Patreon using the button below

To keep up to date follow us on the below channels.










![[QILIN] - Ransomware Victim: Zimmerman & Frachtman PA Law Firm 7 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)

