Exploit released for PaperCut flaw abused to hijack servers, patch now
Attackers are exploiting severe vulnerabilities in the widely-used PaperCut MF/NG print management software to install Atera remote management software to take over servers.
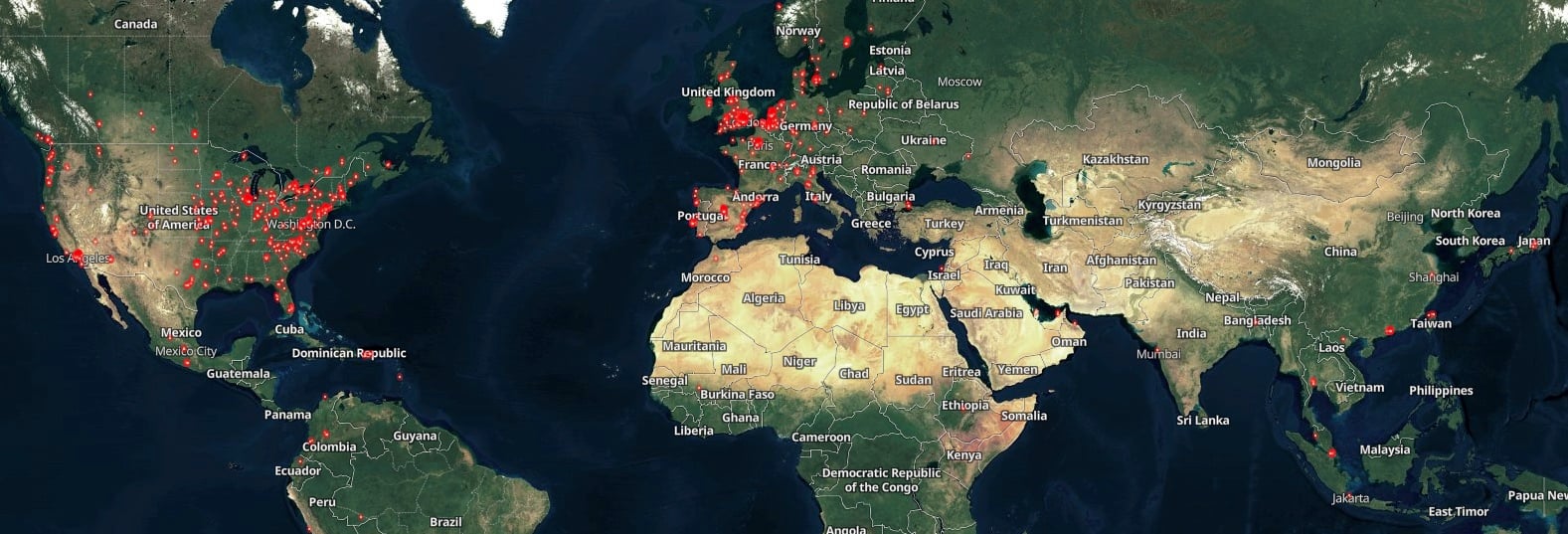
The software’s developer claims it’s used by more than 100 million users from over 70,000 companies worldwide.
The two security flaws (tracked as CVE-2023-27350 and CVE-2023-27351) allow remote attackers to bypass authentication and execute arbitrary code on compromised PaperCut servers with SYSTEM privileges in low-complexity attacks that don’t require user interaction.
“Both of these vulnerabilities have been fixed in PaperCut MF and PaperCut NG versions 20.1.7, 21.2.11 and 22.0.9 and later. We highly recommend upgrading to one of these versions containing the fix,” the company warned.
Proof-of-concept exploit available
Earlier today, attack surface assessment firm Horizon3 published a blog post containing detailed technical information and a CVE-2023-27350 proof-of-concept (PoC) exploit that attackers could use to bypass authentication and execute code on unpatched PaperCut servers.
Horizon3 says the RCE exploit helps gain “remote code execution by abusing the built-in ‘Scripting’ functionality for printers.”
Huntress also created a PoC exploit to showcase the threat posed by these ongoing attacks but is yet to release it online (a video demo is available below).
While unpatched PaperCut servers are already being targeted in the wild, additional threat actors will also likely use Horizon3’s exploit code in further attacks.
Fortunately, a Shodan search shows that attackers could target only around 1,700 Internet-exposed PaperCut servers.
CISA added the CVE-2023-27350 flaw to its list of actively exploited vulnerabilities on Friday, ordering federal agencies to secure their systems against ongoing exploitation within three weeks by May 12, 2023.
Huntress advises administrators unable to promptly patch their PaperCut servers should take measures to prevent remote exploitation.
This includes blocking all traffic to the web management port (default port 9191) from external IP addresses on an edge device, as well as blocking all traffic to the same port on the server’s firewall to restrict management access solely to the server and prevent potential network breaches.
Links to Clop ransomware
According to Huntress security researchers who have been analyzing post-exploitation activity linked to these ongoing attacks since April 16, when the first attacks were observed, threat actors have been using the flaw to execute PowerShell commands that install Atera and Syncro remote management software.
These attacks were preceded by the registration of the windowservicecenter.com domain on April 12th, which was also used to host and deliver TrueBot downloader, a malware linked to the Silence cybercrime group and used to deploy Clop ransomware payloads since December 2022.
“While the ultimate goal of the current activity leveraging PaperCut’s software is unknown, these links (albeit somewhat circumstantial) to a known ransomware entity are concerning,” Huntress Labs said.
“Potentially, the access gained through PaperCut exploitation could be used as a foothold leading to follow-on movement within the victim network, and ultimately ransomware deployment.”
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below


To keep up to date follow us on the below channels.






![Cobalt Strike Beacon Detected - 140[.]143[.]132[.]170:80 12 Cobalt-Strike](https://www.redpacketsecurity.com/wp-content/uploads/2021/11/Cobalt-Strike-300x201.jpg)
