Hackers target vulnerable WordPress Elementor plugin after PoC released

Hackers are now actively probing for vulnerable Essential Addons for Elementor plugin versions on thousands of WordPress websites in massive Internet scans, attempting to exploit a critical account password reset flaw disclosed earlier in the month.
The critical-severity flaw is tracked as CVE-2023-32243 and impacts Essential Addons for Elementor versions 5.4.0 to 5.7.1, allowing unauthenticated attackers to arbitrarily reset the passwords of administrator accounts and assume control of the websites.
The flaw that impacted over a million websites was discovered by PatchStack on May 8th, 2023, and fixed by the vendor on May 11th, with the release of the plugin’s version 5.7.2.
Scale of exploitation
On May 14th, 2023, researchers published a proof-of-concept (PoC) exploit on GitHub, making the tool widely available to attackers.
At the time, a BleepingComputer reader and website owner reported that their site was hit by hackers who reset the admin password by leveraging the flaw. Still, the scale of the exploitation was unknown.
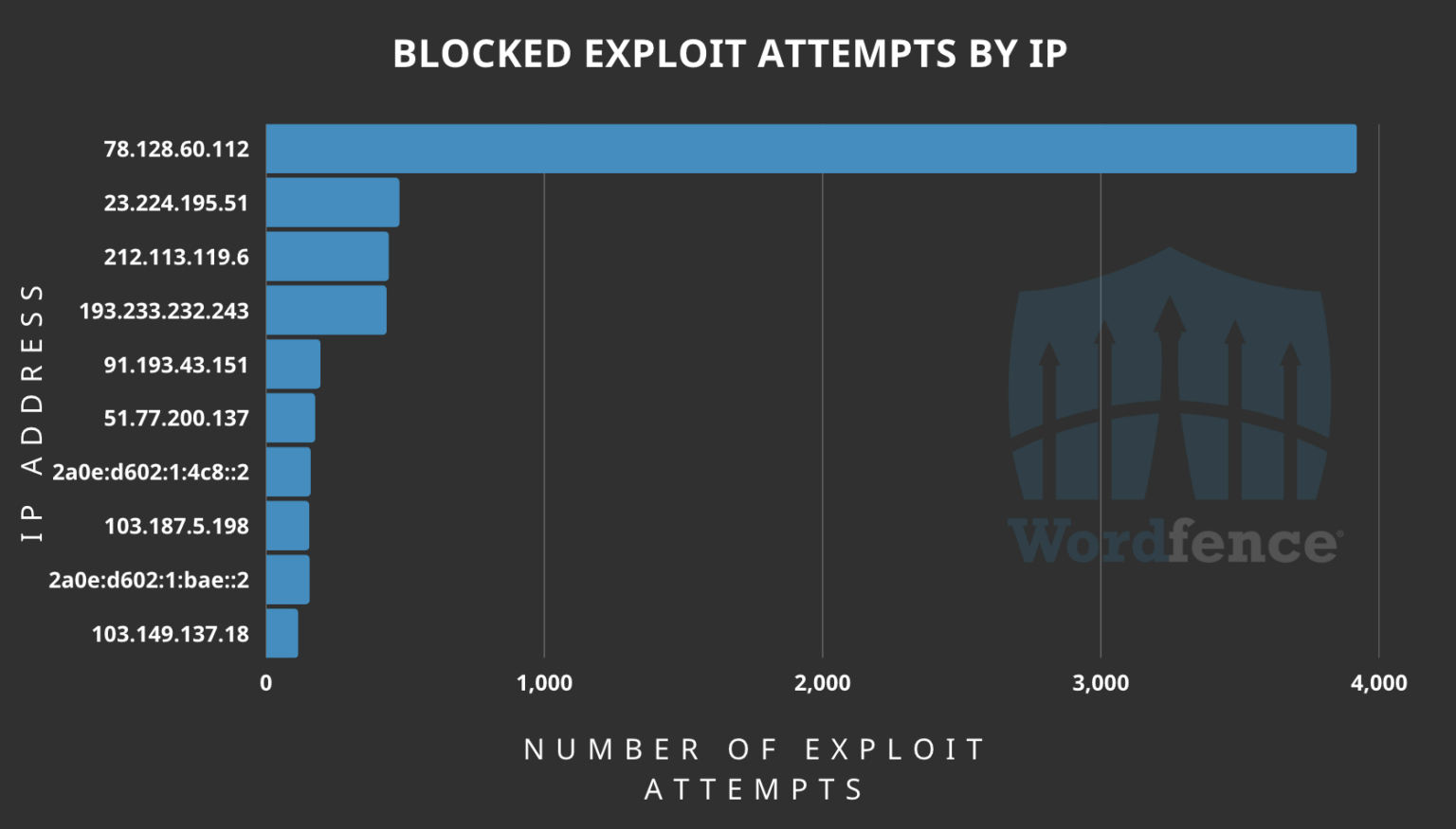
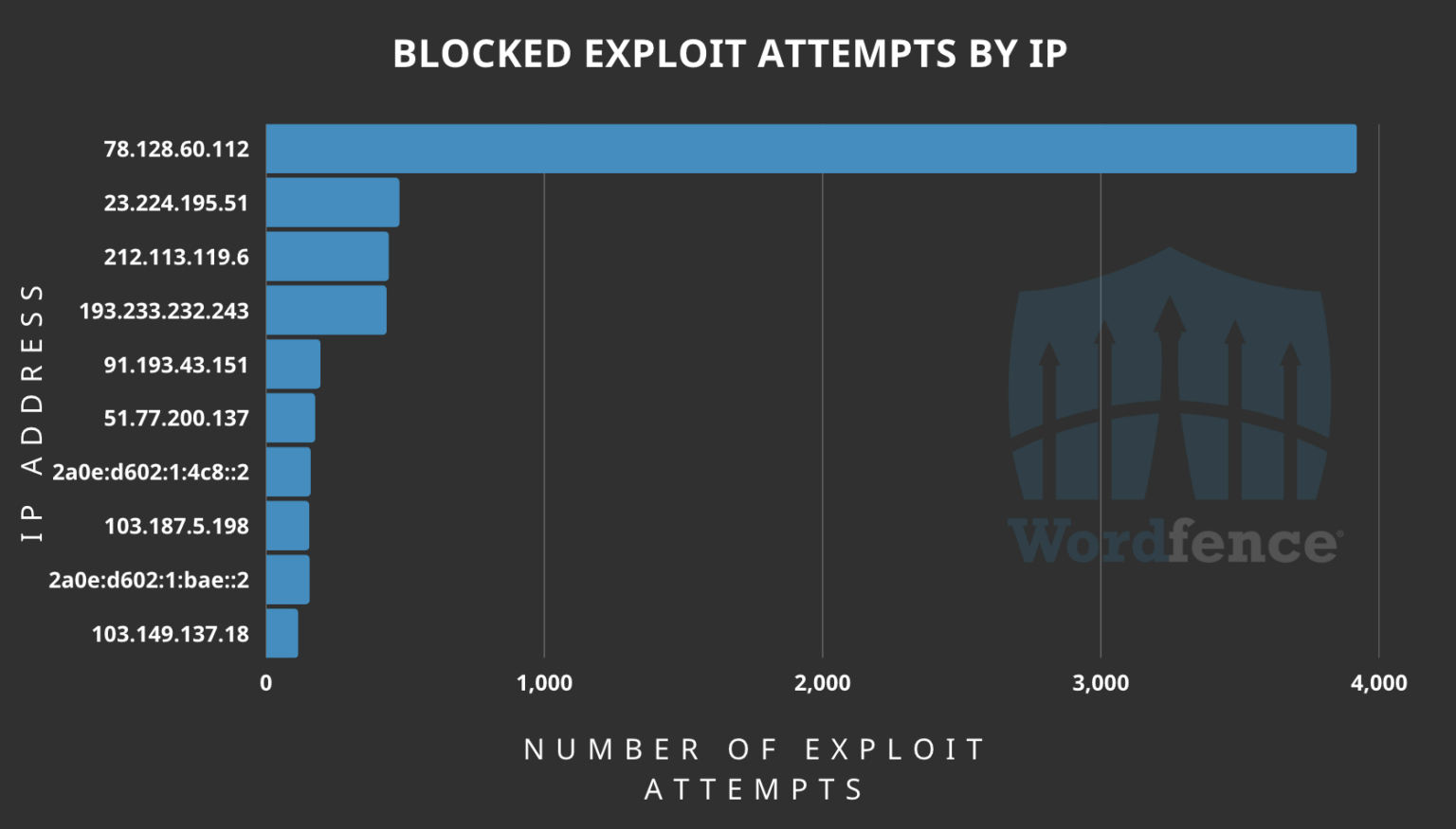
A Wordfence report published yesterday sheds more light, with the company claiming to observe millions of probing attempts for the presence of the plugin on websites and has blocked at least 6,900 exploitation attempts.
On the day after the disclosure of the flaw, WordFence recorded 5,000,000 probing scans looking for the plugin’s ‘readme.txt’ file, which contains the plugin’s version information, and hence determines if a site is vulnerable.


“While there are services that probe installation data for legitimate purposes, we believe this data indicates that attackers began looking for vulnerable sites as soon as the vulnerability was disclosed,” comments Wordfence in the report.
Most of these requests came from just two IP addresses, ‘185.496.220.26’ and ‘185.244.175.65.’
As for the exploitation attempts, the IP address ‘78.128.60.112’ had a considerable volume, utilizing the PoC exploit released on GitHub. Other high-ranking attacking IPs count between 100 and 500 attempts.
Website owners using the ‘Essential Addons for Elementor’ plugin are advised to apply the available security update by installing version 5.7.2 or later immediately.
“Considering how easily this vulnerability can be successfully exploited, we highly recommend all users of the plugin update ASAP to ensure their site is not compromised by this vulnerability,” advises Wordfence.
Additionally, website administrators should use the indicators of compromise listed on Wordfence’s report and add the offending IP addresses to a blocklist to stop these and future attacks.
Users of Wordfence’s free security package will be covered by protection against CVE-2023-32243 on June 20, 2023, so they’re currently exposed too.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below




To keep up to date follow us on the below channels.





