Chinese Hackers Use HTML Smuggling to Infiltrate European Ministries with PlugX
A Chinese nation-state group has been observed targeting Foreign Affairs ministries and embassies in Europe using HTML smuggling techniques to deliver the PlugX remote access trojan on compromised systems.
Cybersecurity firm Check Point said the activity, dubbed SmugX, has been ongoing since at least December 2022.
“The campaign uses new delivery methods to deploy (most notably – HTML Smuggling) a new variant of PlugX, an implant commonly associated with a wide variety of Chinese threat actors,” Check Point said.
“Although the payload itself remains similar to the one found in older PlugX variants, its delivery methods result in low detection rates, which until recently helped the campaign fly under the radar.”
The exact identity of the threat actor behind the operation is a little hazy, although existing clues point in the direction of Mustang Panda, which also shares overlaps with clusters tracked as Earth Preta, RedDelta, and Check Point’s own designation Camaro Dragon.
However, the company said there is “insufficient evidence” at this stage to conclusively attribute it to the adversarial collective.
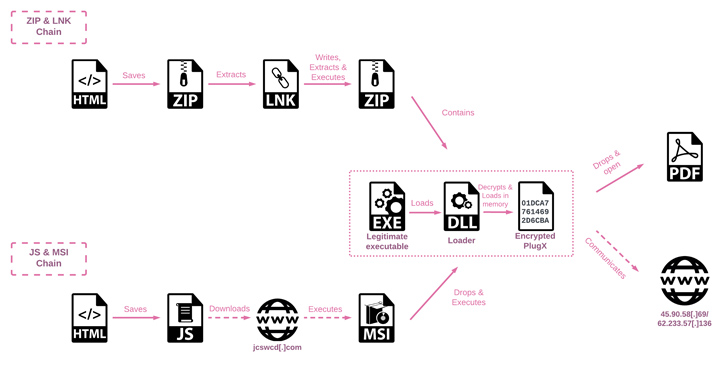
The latest attack sequence is significant for the use of HTML Smuggling – a stealthy technique in which legitimate HTML5 and JavaScript features are abused to assemble and launch the malware – in the decoy documents attached to spear-phishing emails.
“HTML smuggling employs HTML5 attributes that can work offline by storing a binary in an immutable blob of data within JavaScript code,” Trustwave noted earlier this February. “The data blob, or the embedded payload, gets decoded into a file object when opened via a web browser.”
An analysis of the documents, which were uploaded to the VirusTotal malware database, reveals that they are designed to target diplomats and government entities in Czechia, Hungary, Slovakia, the U.K., Ukraine, and also likely France and Sweden.
In one instance, the threat actor is said to have employed an Uyghur-themed lure (“China Tries to Block Prominent Uyghur Speaker at UN.docx”) that, when opened, beacons to an external server by means of an embedded, invisible tracking pixel to exfiltrate reconnaissance data.
The multi-stage infection process utilizes DLL side-loading methods to decrypt and launch the final payload, PlugX.
Also called Korplug, the malware dates all the way back to 2008 and is a modular trojan capable of accommodating “diverse plugins with distinct functionalities” that enables the operators to carry out file theft, screen captures, keystroke logging, and command execution.
“During the course of our investigating the samples, the threat actor dispatched a batch script, sent from the C&C server, intended to erase any trace of their activities,” Check Point said.
“This script, named del_RoboTask Update.bat, eradicates the legitimate executable, the PlugX loader DLL, and the registry key implemented for persistence, and ultimately deletes itself. It is likely this is the result of the threat actors becoming aware they were under scrutiny.”
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.



![[INCRANSOM] - Ransomware Victim: Pastor Real Estate 3 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)
