Silentbob Campaign: Cloud-Native Environments Under Attack
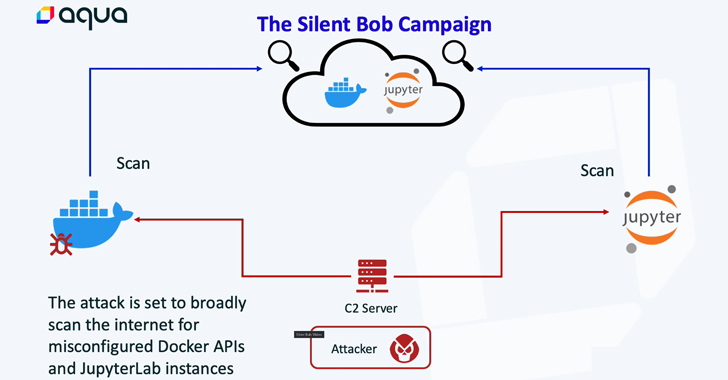
Cybersecurity researchers have unearthed an attack infrastructure that’s being used as part of a “potentially massive campaign” against cloud-native environments.
“This infrastructure is in early stages of testing and deployment, and is mainly consistent of an aggressive cloud worm, designed to deploy on exposed JupyterLab and Docker APIs in order to deploy Tsunami malware, cloud credentials hijack, resource hijack, and further infestation of the worm,” cloud security firm Aqua said.
The activity, dubbed Silentbob in reference to an AnonDNS domain set up by the attacker, is said to be linked to the infamous cryptojacking group tracked as TeamTNT, citing overlaps in tactics, techniques, and procedures (TTPs). Alternatively, it could be the work of an “advanced copycat.”
Aqua’s investigation was prompted in the aftermath of an attack targeting its honeypot in early June 2023, leading to the discovery of four malicious container images that are designed to detect exposed Docker and Jupyter Lab instances and deploy a cryptocurrency miner as well as the Tsunami backdoor.
This feat is achieved by means of a shell script that’s programmed to launch when the container starts and is used to deploy the Go-based ZGrab scanner to locate misconfigured servers. Docker has since taken down the images from the public registry. The list of images are below –
- shanidmk/jltest2 (44 pulls)
- shanidmk/jltest (8 pulls)
- shanidmk/sysapp (11 pulls)
- shanidmk/blob (29 pulls)
shanidmk/sysapp, besides executing a cryptocurrency miner on the infected host, is configured to download and run additional binaries, which Aqua said could either be backup cryptominers or the Tsunami malware.
Discover different approaches to conquer Privileged Account Management (PAM) challenges and level up your privileged access security strategy.
Join the WebinarAlso downloaded by the container is a file named “aws.sh.txt,” a script that’s likely designed to systematically scan the environment for AWS keys for subsequent exfiltration.
Aqua said it found 51 servers with exposed JupyterLab instances in the wild, all of which have been actively exploited or exhibited signs of exploitation by threat actors. This includes a “live manual attack on one of the servers that employed masscan to scan for exposed Docker APIs.”
“Initially, the attacker identifies a misconfigured server (either Docker API or JupyterLab) and deploys a container or engages with the Command Line Interface (CLI) to scan for and identify additional victims,” security researchers Ofek Itach and Assaf Morag said.
“This process is designed to spread the malware to an increasing number of servers. The secondary payload of this attack includes a crypto miner and a backdoor, the latter employing the Tsunami malware as its weapon of choice.”
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.

![[RAWORLD] - Ransomware Victim: Co****nt 2 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)