Hackers target European government entities in SmugX campaign

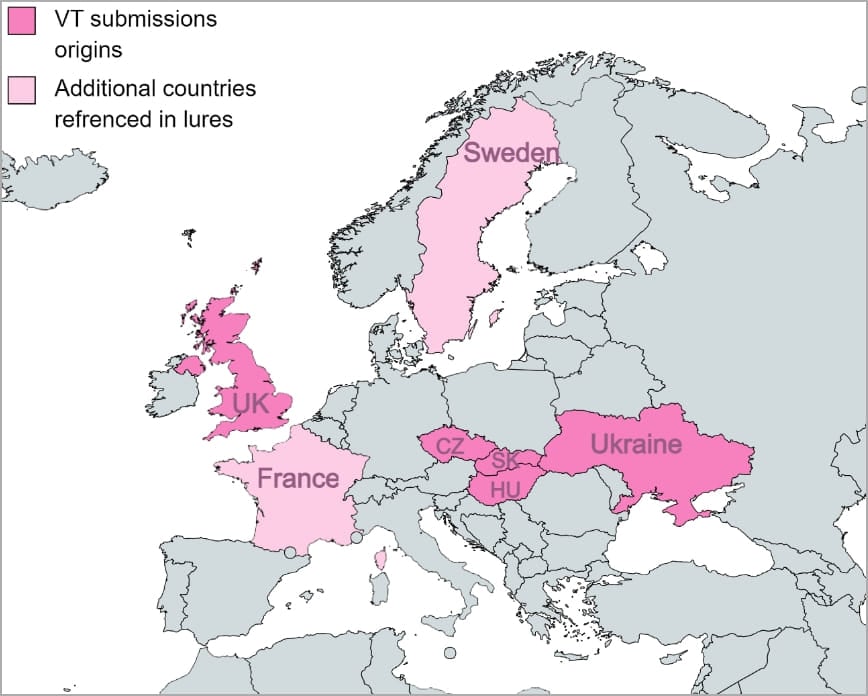
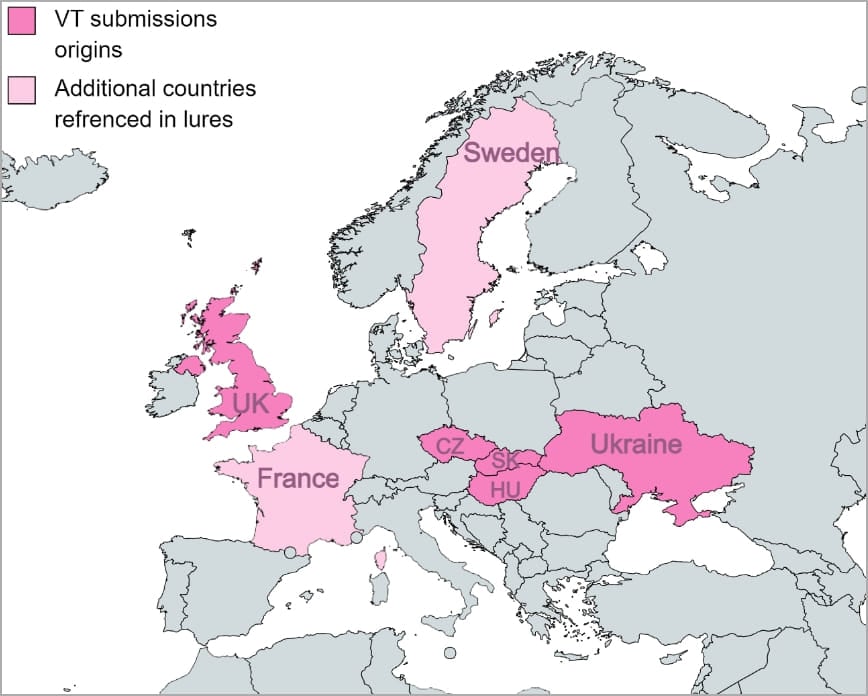
A phishing campaign that security researchers named SmugX and attributed to a Chinese threat actor has been targeting embassies and foreign affairs ministries in the UK, France, Sweden, Ukraine, Czech, Hungary, and Slovakia, since December 2022.
Researchers at cybersecurity company Check Point analyzed the attacks and observed overlaps with activity previously attributed to advanced persistent threat (APT) groups tracked as Mustang Panda and RedDelta.
Looking at the lure documents, the researchers noticed that they are typically themed around European domestic and foreign policies.
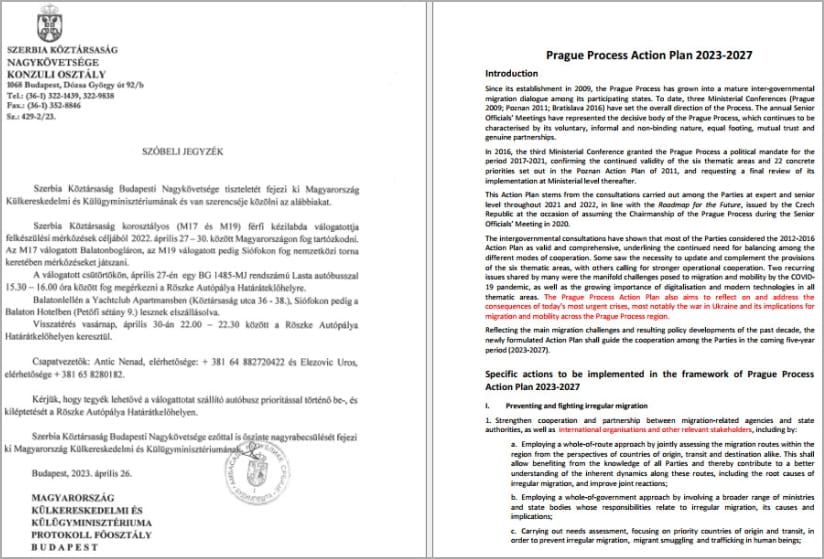
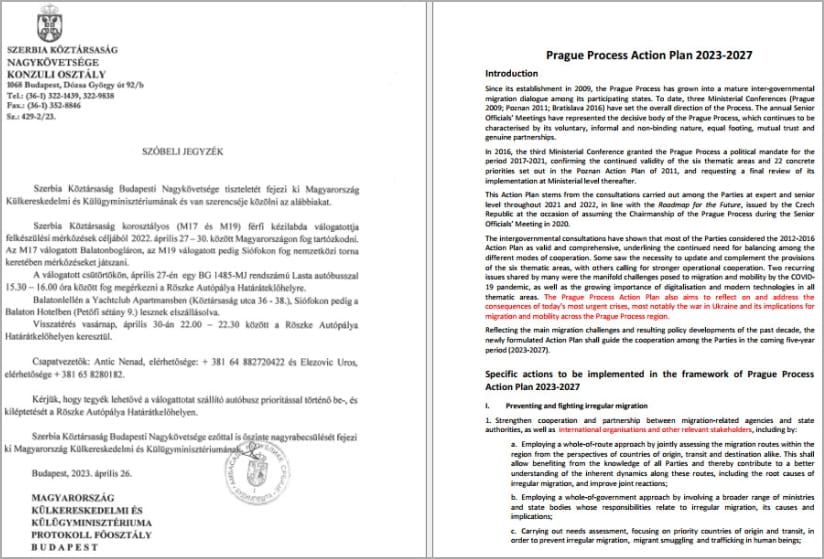
Among the samples that Check Point collected during the investigation are:
- A letter from the Serbian embassy in Budapest
- a document stating the priorities of the Swedish Presidency of the Council of the European Union
- an invitation to a diplomatic conference issued by Hungary’s Ministry of Foreign Affairs
- an article about two Chinese human rights lawyers
The lures used in the SmugX campaign betray the threat actor’s target profile and indicates espionage as the likely objective of the campaign.
SmugX attack chains
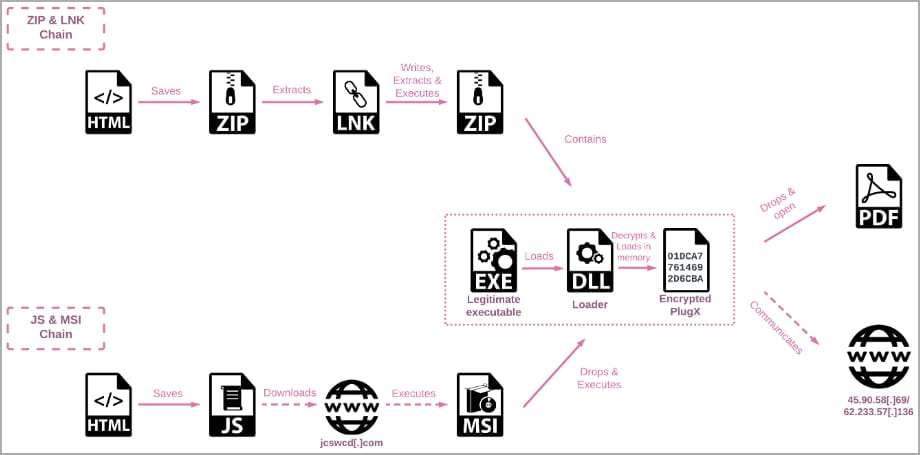
Check Point observed that SmugX attacks rely on two infection chains, both employing the HTML smuggling technique to hide malicious payloads in encoded strings of HTML documents attached to the lure message.
One variant of the campaign delivers a ZIP archive with a malicious LNK file that runs PowerShell when launched, to extract an archive and save it into the Windows temporary directory.
The extracted archive contains three files, one being a legitimate executable (either “robotaskbaricon.exe” or “passwordgenerator.exe”) from an older version of the RoboForm password manager that allowed loading DLL files unrelated to the application, a technique called DLL sideloading.
The other two files are a malicious DLL (Roboform.dll) that is sideloaded using one of the two legitimate executables, and “data.dat” – which contains the PlugX remote access trojan (RAT) that is executed through PowerShell.
The second variant of the attack chain uses HTML smuggling to download a JavaScript file that executes an MSI file after downloading it from the attacker’s command and control (C2) server.
The MSI then creates a new folder within the “%appdata%\Local” directory and stores three files: a hijacked legitimate executable, the loader DLL, and the encrypted PlugX payload (‘data.dat’).
Again, the legitimate program is executed, and PlugX malware is loaded into memory via DLL sideloading in an effort to avoid detection.
To ensure persistence, the malware creates a hidden directory where it stores the legitimate executable and malicious DLL files and adds the program to the ‘Run’ registry key.
Once PlugX is installed and running on the victim’s machine, it may load a deceptive PDF file to distract the victim and reduce their suspicion.
PlugX is a modular RAT that has been used by multiple Chinese APTs since 2008. It comes with a wide range of functions that include file exfiltration, taking screenshots, keylogging, and command execution.
While the malware is typically associated with APT groups, it has also been used by cybercriminal threat actors.
However, the version that Check Point saw deployed in the SmugX campaign is largely the same as those seen in other recent attacks attributed to a Chinese adversary, with the difference that it used the RC4 cipher instead of XOR.
Based on the details uncovered, Check Point researchers believe that the SmugX campaign shows that Chinese threat groups are becoming interested in European targets, likely for espionage.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.

