Python-Based PyLoose Fileless Attack Targets Cloud Workloads for Cryptocurrency Mining
A new fileless attack dubbed PyLoose has been observed striking cloud workloads with the goal of delivering a cryptocurrency miner, new findings from Wiz reveal.
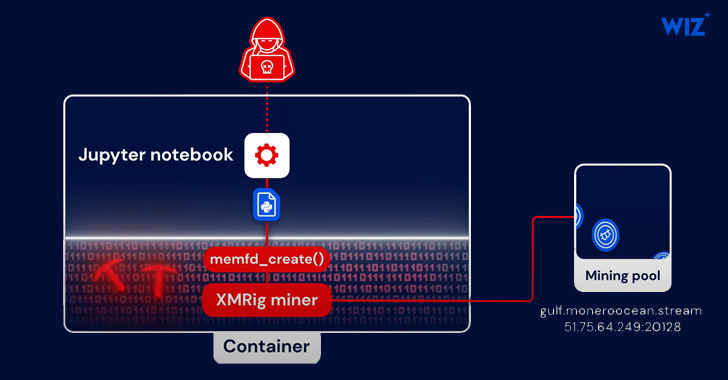
“The attack consists of Python code that loads an XMRig Miner directly into memory using memfd, a known Linux fileless technique,” security researchers Avigayil Mechtinger, Oren Ofer, and Itamar Gilad said. “This is the first publicly documented Python-based fileless attack targeting cloud workloads in the wild.”
The cloud security firm said it found nearly 200 instances where the attack method was employed for cryptocurrency mining. No other details about the threat actor are currently known other than the fact that they possess sophisticated capabilities.
In the infection chain documented by Wiz, initial access is achieved through the exploitation of a publicly accessible Jupyter Notebook service that allowed for the execution of system commands using Python modules.
PyLoose, first detected on June 22, 2023, is a Python script with just nine lines of code that embeds a compressed and encoded precompiled XMRig miner. The payload is retrieved from paste.c-net[.]org into the Python runtime’s memory by means of an HTTPS GET request without having to write the file to disk.
The Python code is designed to decode and decompress the XMRig miner and then load it directly into memory via the memfd memory file descriptor, which is used to access memory-resident files.
Worried about insider threats? We’ve got you covered! Join this webinar to explore practical strategies and the secrets of proactive security with SaaS Security Posture Management.
Claim Your Spot“The attacker went to great lengths to be untraceable by using an open data-sharing service to host the Python payload, adapting the fileless execution technique to Python, and compiling an XMRig miner to embed its config to avoid touching the disk or using a revealing command line,” the researchers said.
The development comes as Sysdig detailed a new attack campaign mounted by a threat actor known as SCARLETEEL that entails the abuse of AWS infrastructure to steal proprietary data and conduct illicit crypto mining.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.

![[QILIN] - Ransomware Victim: www[.]unitedcaps[.]com 1 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)

