Over 15K Citrix servers likely vulnerable to CVE-2023-3519 attacks

Thousands of Citrix Netscaler ADC and Gateway servers exposed online are likely vulnerable against a critical remote code execution (RCE) bug exploited by unauthenticated attackers in the wild as a zero-day.
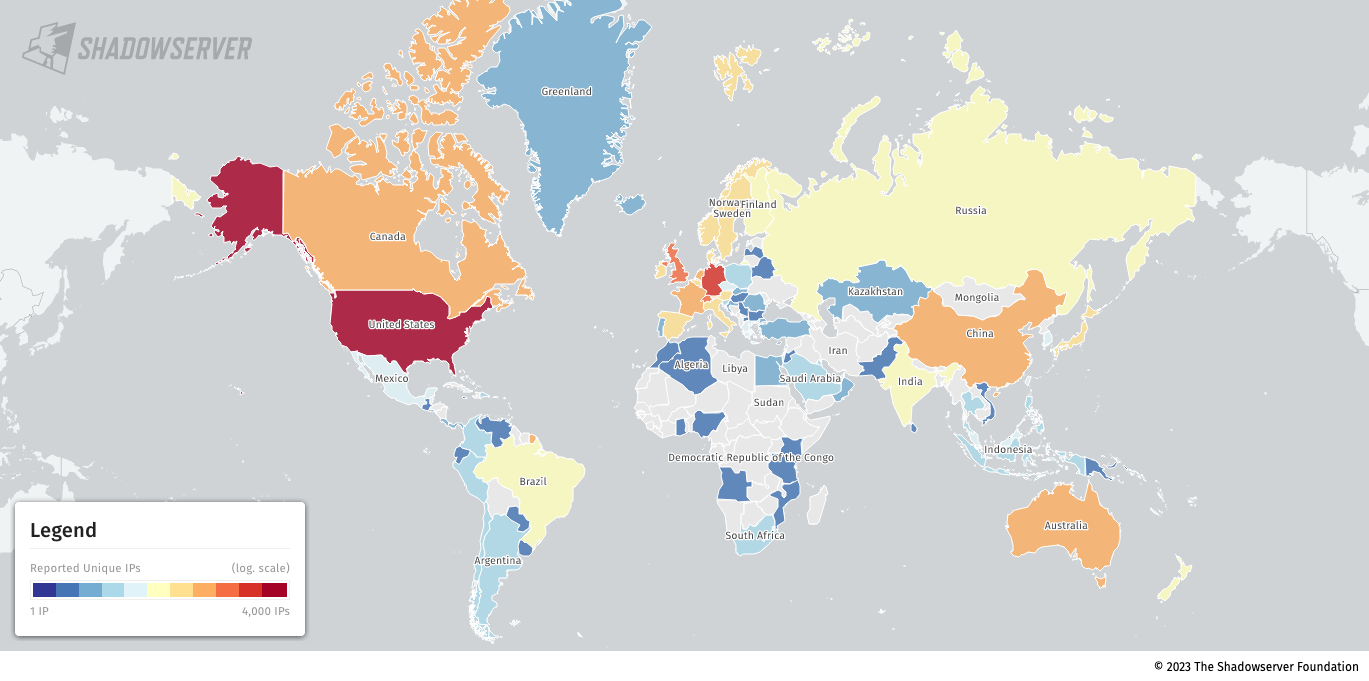
Security researchers from the Shadowserver Foundation, a non-profit organization dedicated to enhancing internet security, revealed this week that at least 15,000 appliances were identified as exposed to attacks leveraging the flaw (CVE-2023-3519) based on their version information.
“We tag all IPs where we see a version hash in a Citrix instance. This is due fact that Citrix has removed version hash information in recent revisions,” Shadowserver said.
“Thus safe to assume in our view all instances that still provide version hashes have not been updated and may be vulnerable.”
They also noted that they’re also undercounting since some revisions known to be vulnerable but with no version hashes have not been tagged and added to the total number of exposed Citrix servers.
Citrix released security updates to address this RCE vulnerability on July 18th, saying that “exploits of CVE-2023-3519 on unmitigated appliances have been observed” and urging customers to install the patches as soon as possible.
The company added that unpatched Netscaler appliances must be configured as a gateway (VPN virtual server, ICA Proxy, CVPN, RDP Proxy) or an authentication virtual server (the so-called AAA server) to be vulnerable to attacks.
The CVE-2023-3519 RCE zero-day was likely available online since the first week of July when a threat actor began advertising Citrix ADC zero-day flaw on a hacker forum.
BleepingComputer has also been aware that Citrix had learned of the zero-day advertisement and was working on a patch before making an official disclosure.
The same day, Citrix patched two other high-severity vulnerabilities tracked as CVE-2023-3466 and CVE-2023-3467.
The former allows attackers to launch reflected cross-site scripting (XSS) attacks by tricking targets on the same networks into loading a malicious link in the web browser, while the latter makes it possible to elevate privileges to get root permissions.
While the second is much more impactful, it also requires authenticated access to the vulnerable appliances’ management interface via their IP (NSIP) or a SubNet IP (SNIP) address.
CISA also ordered U.S. federal agencies on Wednesday to secure Citrix servers on their networks against ongoing attacks by August 9th, warning that the bug was already used to breach the systems of a U.S. critical infrastructure organization.
“In June 2023, threat actors exploited this vulnerability as a zero-day to drop a webshell on a critical infrastructure organization’s NetScaler ADC appliance,” CISA said in a separate advisory published on Thursday.
“The webshell enabled the actors to perform discovery on the victim’s active directory (AD) and collect and exfiltrate AD data. The actors attempted to move laterally to a domain controller but network-segmentation controls for the appliance blocked movement.”
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.

