Thousands of Android Malware Apps Using Stealthy APK Compression to Evade Detection
Threat actors are using Android Package (APK) files with unknown or unsupported compression methods to elude malware analysis.
That’s according to findings from Zimperium, which found 3,300 artifacts leveraging such compression algorithms in the wild. 71 of the identified samples can be loaded on the operating system without any problems.
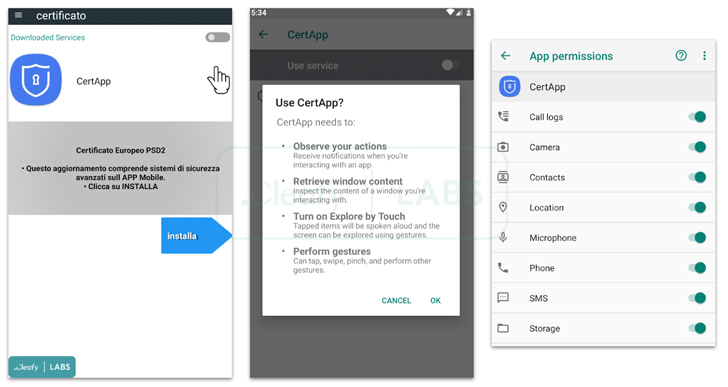
There is no evidence that the apps were available on the Google Play Store at any point in time, indicating that the apps were distributed through other means, typically via untrusted app stores or social engineering to trick the victims into sideloading them.
The APK files use “a technique that limits the possibility of decompiling the application for a large number of tools, reducing the possibilities of being analyzed,” security researcher Fernando Ortega said. “In order to do that, the APK (which is in essence a ZIP file), is using an unsupported decompression method.”
The advantage of such an approach is its ability to resist decompilation tools, while still being able to be installed on Android devices whose operating system version is above Android 9 Pie.
The Texas-based cybersecurity firm said it started its own analysis after a post from Joe Security on X (previously Twitter) in June 2023 about an APK file that exhibited this behavior.
Android packages use the ZIP format in two modes, one without compression and one using the DEFLATE algorithm. The crucial finding here is that APKs packed using unsupported compression methods are not installable on handsets running Android versions below 9, but they work properly on subsequent versions.
In addition, Zimperium discovered that malware authors are also deliberately corrupting the APK files by having filenames with more than 256 bytes and malformed AndroidManifest.xml files to trigger crashes on analysis tools.
The disclosure comes weeks after Google revealed that threat actors are leveraging a technique called versioning to evade its Play Store’s malware detections and target Android users.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.

![Cobalt Strike Beacon Detected - 52[.]231[.]10[.]139:8080 2 Cobalt Strike](https://www.redpacketsecurity.com/wp-content/uploads/2021/11/Cobalt-Strike-300x201.jpg)