ADReaper – A Fast Enumeration Tool For Windows Active Directory Pentesting Written In Go
ADReaper is a tool written in Golang which enumerate a Active Directory environment with LDAP queries within few seconds.
Installation
You can download precompiled executable binaries for Windows/Linux from latest releases
Install from source
To build from source, clone the repo and build it with GO
$ git clone https://github.com/AidenPearce369/ADReaper
$ cd ADReaper/
$ go buildUsage
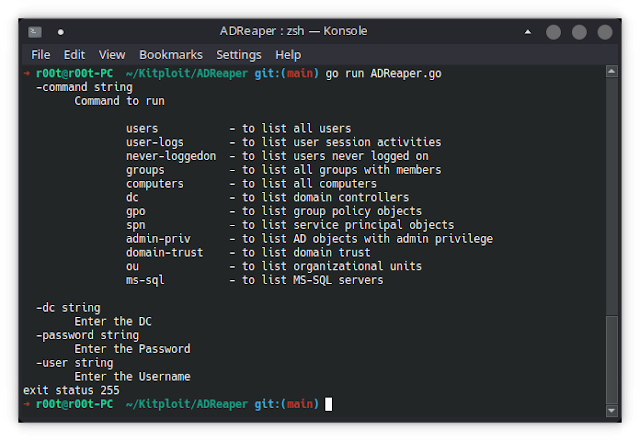
ADReaper performs enumeration with various commands that performs LDAP queries with respective to it
group policy objects spn – to list service principal objects admin-priv – to list AD objects with admin privilege domain-trust – to list domain trust ou – to list organizational units ms-sql – to list MS-SQL servers -dc string Enter the DC -password string Enter the Password -user string Enter the Username “>
monish@chimera:/ADReaper$ ./ADReaper
-command string
Command to run
users - to list all users
user-logs - to list user session activities
never-loggedon - to list users never logged on
groups - to list all groups with members
computers - to list all computers
dc - to list domain controllers
gpo - to list group policy objects
spn - to list service principal objects
admin-priv - to list AD objects with admin privilege
domain-trust - to list domain trust
ou - to list organizational units
ms-sql - to list MS-SQL servers
-dc string
Enter the DC
-password string
Enter th e Password
-user string
Enter the Username
To-Do
Looking forward for contributors to build the next version
Planned features,
- Custom LDAP querying
- Filters with existing commands
- PrivEsc checker
- LAPS enumeration
- Kerberoasting
- Local admin access hunting
- Registry analysis
If interested, ping me 🙂
Download ADReaper
If you like the site, please consider joining the telegram channel or supporting us on Patreon using the button below.


![Cobalt Strike Beacon Detected - 154[.]204[.]35[.]215:80 3 Cobalt-Strike](https://www.redpacketsecurity.com/wp-content/uploads/2021/11/Cobalt-Strike-300x201.jpg)