3,000 Apache ActiveMQ servers vulnerable to RCE attacks exposed online

Over three thousand internet-exposed Apache ActiveMQ servers are vulnerable to a recently disclosed critical remote code execution (RCE) vulnerability.
Apache ActiveMQ is a scalable open-source message broker that fosters communication between clients and servers, supporting Java and various cross-language clients and many protocols, including AMQP, MQTT, OpenWire, and STOMP.
Thanks to the project’s support for a diverse set of secure authentication and authorization mechanisms, it is widely used in enterprise environments where systems communicate without direct connectivity.
The flaw in question is CVE-2023-46604, a critical severity (CVSS v3 score: 10.0) RCE allowing attackers to execute arbitrary shell commands by exploiting the serialized class types in the OpenWire protocol.
According to Apache’s disclosure from October 27, 2023, the issue affects the following Apache Active MQ and Legacy OpenWire Module versions:
- 5.18.x versions before 5.18.3
- 5.17.x versions before 5.17.6
- 5.16.x versions before 5.16.7
- All versions before 5.15.16
Fixes were made available on the same day with the release of versions 5.15.16, 5.16.7, 5.17.6, and 5.18.3, which are the recommended upgrade targets.
Thousands of servers unpatched
Researchers from threat monitoring service ShadowServer found 7,249 servers accessible with ActiveMQ services.
Of those, 3,329 were found to run an ActiveMQ version vulnerable to CVE-2023-4660, with all of these servers vulnerable to remote code execution.
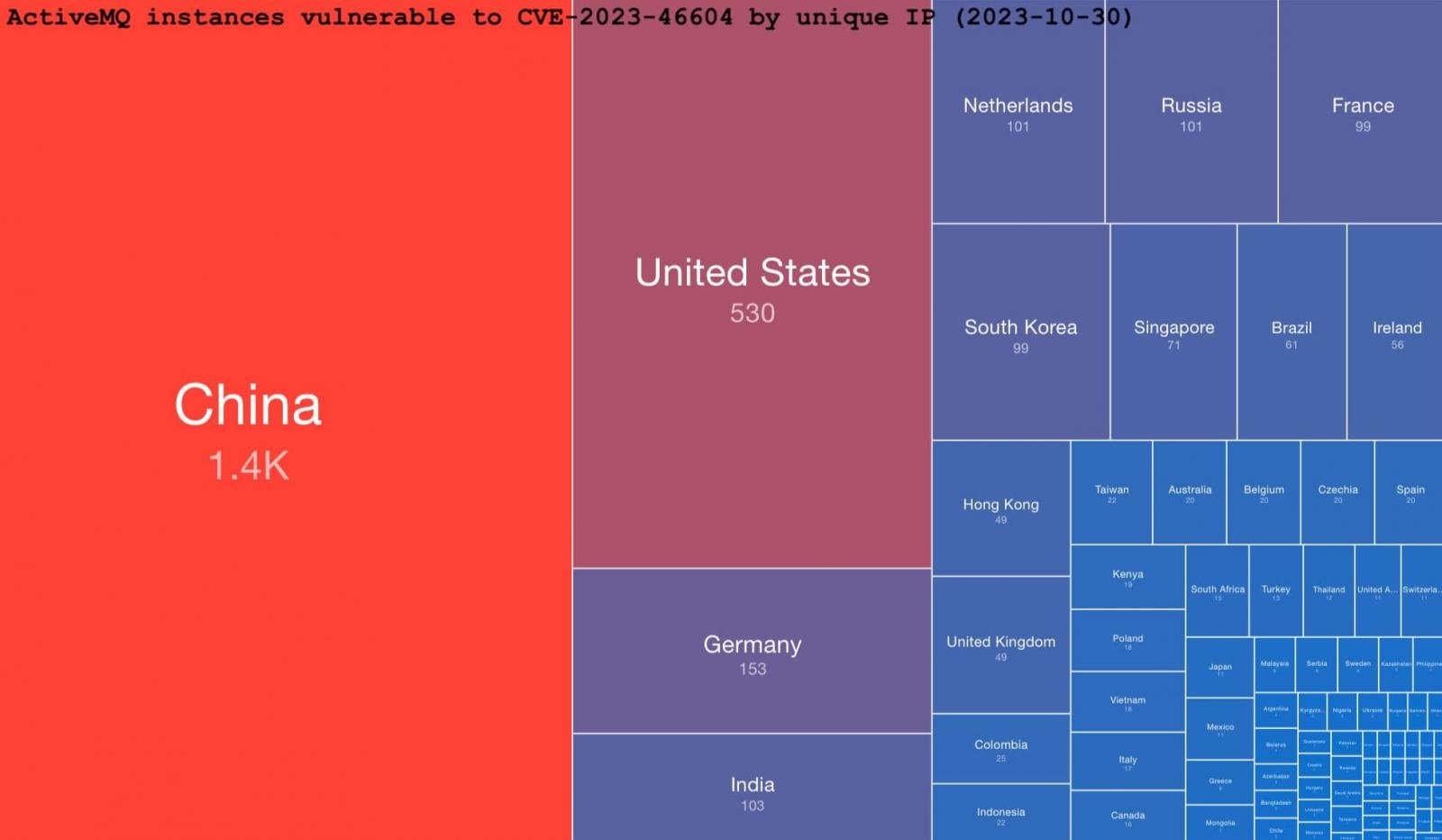
Most of the vulnerable instances (1,400) are located in China. The United States comes second with 530, Germany is third with 153, while India, the Netherlands, Russia, France, and South Korea have 100 exposed servers each.
Given the role Apache ActiveMQ fulfills as a message broker in enterprise environments, exploitation of CVE-2023-46604 could result in message interception, workflow disruption, data theft, and even lateral movement in the network.
As technical details on exploiting CVE-2023-46604 are publicly available, applying the security updates should be considered time-sensitive.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.