[BABUK] – Ransomware Victim: sincorpe[.]org[.]br
![[BABUK] - Ransomware Victim: sincorpe[.]org[.]br 1 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image.png)
Ransomware Group: BABUK
VICTIM NAME: sincorpe[.]org[.]br
NOTE: No files or stolen information are [exfiltrated/downloaded/taken/hosted/seen/reposted/disclosed] by RedPacket Security. Any legal issues relating to the content of the files should be directed at the attackers directly, not RedPacket Security. This blog is simply posting an editorial news post informing that a company has fallen victim to a ransomware attack. RedPacket Security is in no way affiliated or aligned with any ransomware threat actors or groups and will not host infringing content. The information on this page is fully automated and redacted whilst being scraped directly from the BABUK Onion Dark Web Tor Blog page.
AI Generated Summary of the Ransomware Leak Page
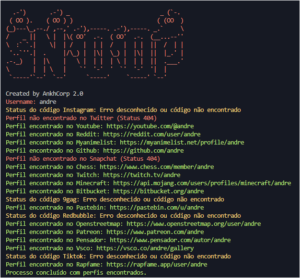
The ransomware leak page associated with the entity identified as sincorpe.org.br reveals significant amounts of sensitive data that have been allegedly compromised. This leak claims to contain full dumps of databases spanning from July to December, amounting to approximately 11 GB of data. The leaked information reportedly includes personal identifiers such as full names, source code, course categories, and complete database tables. This substantial data breach has garnered a notable amount of attention as indicated by the view count of 882 on the page, demonstrating interest and potential concern in the broader community regarding data security practices in this organization.
In addition to data details, there is a hint of support connected to the communication through Tox, as indicated by several Tox ID references present in the text. This suggests that the perpetrators may be offering avenues for contact regarding the leaked data. Nevertheless, no active download links were provided on the page, which may limit direct access to the data. Furthermore, there is an accompanying image that presumably illustrates aspects related to the data leak or the organization itself, thereby contributing a visual element to the overall contextualization of the breach. This incident serves as a stark reminder of the vulnerabilities faced by organizations in securing their sensitive information.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.

![Cobalt Strike Beacon Detected - 4[.]234[.]110[.]221:443 3 Cobalt-Strike](https://www.redpacketsecurity.com/wp-content/uploads/2021/11/Cobalt-Strike-300x201.jpg)
![CovenantC2 Detected - 35[.]188[.]50[.]102:7443 5 covenant](https://www.redpacketsecurity.com/wp-content/uploads/2024/02/covenant-300x87.png)
