Bing search results hijacked via misconfigured Microsoft app
A misconfigured Microsoft application allowed anyone to log in and modify Bing.com search results in real-time, as well as inject XSS attacks to potentially breach the accounts of Office 365 users.
The security issue was discovered by Wiz Research, who named the attack “BingBang.”
Wiz’s analysts reported the issue to Microsoft on January 31, 2023, and the tech giant confirmed that it was fixed on March 28, 2023.
A misconfiguration
Wiz researchers found that when creating an application in Azure App Services and Azure Functions, the app can be mistakenly configured to allow users from any Microsoft tenant, including public users, to log in to the application.
This configuration setting is called ‘Support account types’ and lets developers specify if a specific tenant multi-tenant, personal accounts, or a mix of multi and personal accounts should be allowed to access the application.
This configuration option is offered for legitimate cases where developers must make their apps available across organizational boundaries.
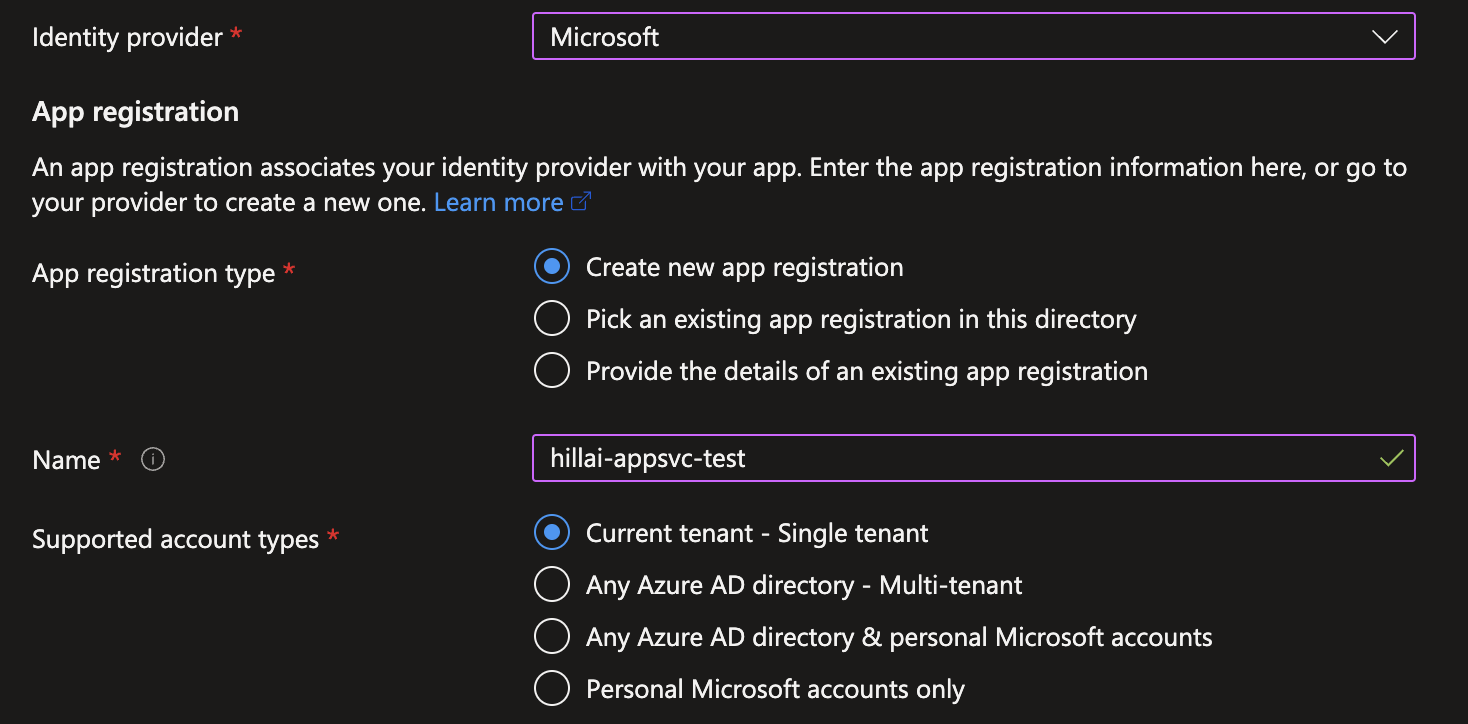
However, if a developer mistakenly assigns looser permissions, it could cause unwanted access to the application and its features.
“This Shared Responsibility architecture is not always clear to developers, and as a result, validation and configuration mistakes are quite prevalent,” comments Wiz in its report.
Such is the extent of the misconfiguration problem that approximately 25% of the multi-tenant apps scanned by Wiz are misconfigured, allowing unconditional access without proper user validation.
In some cases, the misconfigured apps belonged to Microsoft, highlighting how easy it is for admins to make mistakes in Azure AD configuration.
BingBang and XSS attacks
Wiz’s analysts found a misconfigured “Bing Trivia” app that allowed anyone to log in to the application and access its CMS (Content Management System).
However, they soon discovered that the application was directly linked to Bing.com, allowing them to modify the live content shown in Bing search results.
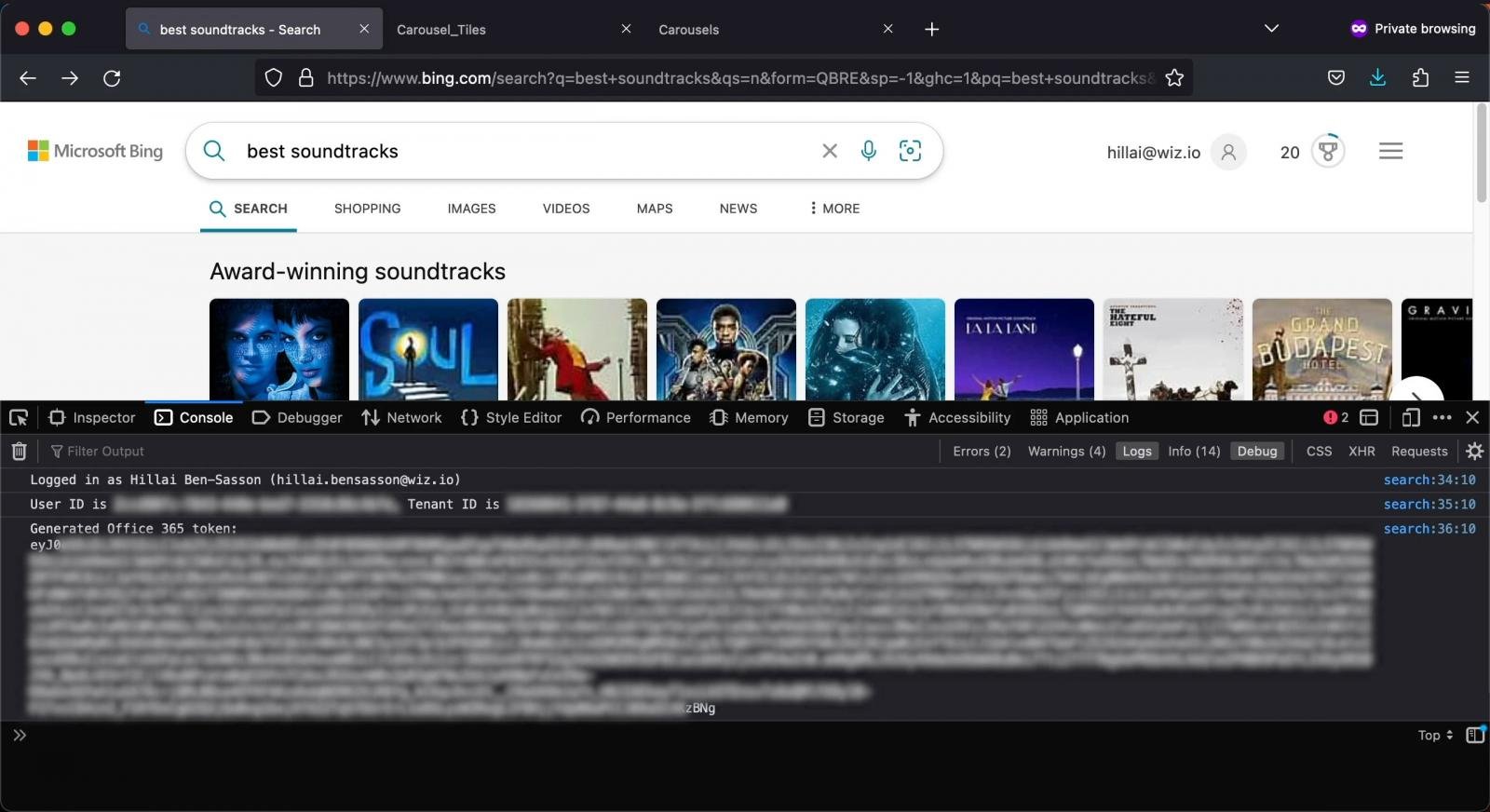
To verify they had complete control, the researchers attempted and succeeded in modifying search results for the “best soundtracks” search term, adding arbitrary results to the top carousel.
Next, the analysts checked if they could inject a payload into the Bing search results using this same CMS and found they could execute a cross-site scripting (XSS) attack on Bing.com.
After confirming that the XSS was possible, Wiz reported its findings to Microsoft and worked with the software company to determine the exact impact of this second attack.
A test XSS showed that it was possible to compromise the Office 365 token of any Bing user that saw the carousel in the search results, giving them full access to the searchers’ accounts.
This includes access to Outlook emails, calendar data, messages on Teams, SharePoint documents, and OneDrive files.
Microsoft’s fix
Microsoft downplayed the issue, saying that the misconfiguration that allowed external parties read and write access impacted only a small number of internal applications and was corrected immediately.
Additionally, Microsoft says it has introduced security enhancements that will prevent Azure AD misconfiguration issues from becoming a problem again.
Most notably, Microsoft has stopped issuing access tokens to clients not registered in the resource tenants, limiting access only to properly registered clients.
“This functionality has been disabled for more than 99% of customer applications,” reads Microsoft’s advisory.
“For the remainder of multi-tenant resource applications that rely on access from clients without a service principal, we have provided instructions in an Azure Service Health Security Advisory to Global Admins (Azure Portal and email) and in the Microsoft 365 Message Center.”
Also, additional security checks have been added for multi-tenant applications, checking for tenant ID matching on a set allow-list and the presence of a client registration (Service Principal).
Developers and admins that control multi-tenant applications are recommended to consult Microsoft’s updated guidance on securing them properly.
For additional details, Wiz has published a separate, more detailed report that also includes remediation advice.
Wiz Research received a bug bounty of $40,000 for responsibly disclosing their findings to Microsoft.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below


To keep up to date follow us on the below channels.






![[HANDALA] - Ransomware Victim: Commemoration of Commander Martyr Reza Awada 11 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)