BlackByte Ransomware Exploits VMware ESXi Flaw in Latest Attack Wave
The threat actors behind the BlackByte ransomware group have been observed likely exploiting a recently patched security flaw impacting VMware ESXi hypervisors, while also leveraging various vulnerable drivers to disarm security protections.
“The BlackByte ransomware group continues to leverage tactics, techniques, and procedures (TTPs) that have formed the foundation of its tradecraft since its inception, continuously iterating its use of vulnerable drivers to bypass security protections and deploying a self-propagating, wormable ransomware encryptor,” Cisco Talos said in a technical report shared with The Hacker News.
The exploitation of CVE-2024-37085, an authentication bypass vulnerability in VMware ESXi that has also been weaponized by other ransomware groups, is a sign that the e-crime group is pivoting from established approaches.
BlackByte made its debut in the second half of 2021 and is purported to be one of the ransomware variants to have emerged in the months leading up to shutdown of the infamous Conti ransomware crew.
The ransomware-as-a-service (RaaS) group has a history of exploiting ProxyShell vulnerabilities in Microsoft Exchange Server to obtain initial access, while avoiding systems that use Russian and a number of Eastern European languages.
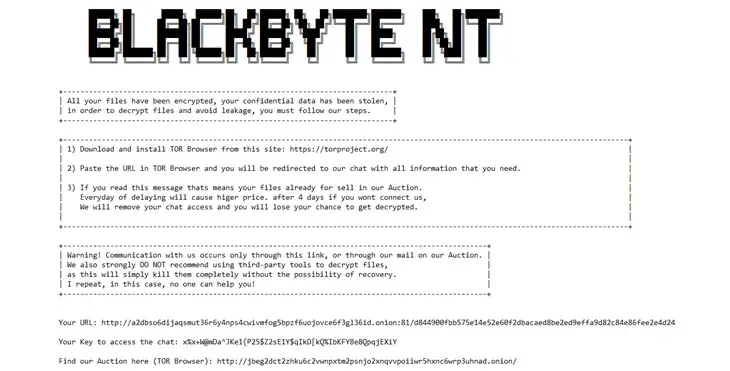
Like RaaS groups, it also leverages double extortion as part of attacks, adopting a name-and-shame approach via a data leak site operated on the dark web to pressurize victims into paying up. Multiple variants of the ransomware, written in C, .NET, and Go, have been observed in the wild to date.
While a decryptor for BlackByte was released by Trustwave in October 2021, the group has continued to refine its modus operandi, even going to the extent of employing a custom tool named ExByte for data exfiltration prior to commencing encryption.
An advisory released by the U.S. government in early 2022 attributed the RaaS group to financially motivated attacks targeting critical infrastructure sectors, including financial, food and agriculture, and government facilities.
One of the important aspects of their attacks is the use of vulnerable drivers to terminate security processes and bypass controls, a technique known as bring your own vulnerable driver (BYOVD).
Cisco Talos, which investigated a recent BlackByte ransomware attack, said the intrusion was likely facilitated using valid credentials to access the victim organization’s VPN. It’s believed that the initial access was obtained through a brute-force attack.
“Given BlackByte’s history of exploiting public-facing vulnerabilities for initial access, the use of VPN for remote access may represent a slight shift in technique or could represent opportunism,” security researchers James Nutland, Craig Jackson, Terryn Valikodath, and Brennan Evans said. “The use of the victim’s VPN for remote access also affords the adversary other advantages, including reduced visibility from the organization’s EDR.”
The threat actor subsequently managed to escalate their privileges, using the permissions to access the organization’s VMware vCenter server to create and add new accounts to an Active Directory group named ESX Admins. This, Talos said, was done by exploiting CVE-2024-37085, which enables an attacker to gain administrator privileges on the hypervisor by creating a group with that name and adding any user to it.
This privilege could then be abused to control virtual machines (VMs), modify host server’s configuration, and gain unauthorized access to system logs, diagnostics, and performance monitoring tools.
Talos pointed out that the exploitation of the flaw took place within days of public disclosure, highlighting the speed at which threat actors refine their tactics to incorporate newly disclosed vulnerabilities into their arsenal and advance their attacks.
Furthermore, the recent BlackByte attacks culminate with the encrypted files being rewritten with the file extension “blackbytent_h,” with the encryptor also dropping four vulnerable drivers as part of the BYOVD attack. All the four drivers follow a similar naming convention: Eight random alphanumeric characters followed by an underscore and an incremental numerical value –
- AM35W2PH (RtCore64.sys)
- AM35W2PH_1 (DBUtil_2_3.sys)
- AM35W2PH_2 (zamguard64.sys aka Terminator)
- AM35W2PH_3 (gdrv.sys)
The professional, scientific, and technical services sectors have the greatest exposure to the observed vulnerable drivers, accounting for 15% of the total, followed by manufacturing (13%) and educational services (13%). Talos has also assessed that the threat actor is likely more active than what it appears to be, and that only an estimated 20-30% of victims are publicly posted, although the exact reason for this disparity remains unclear.

“BlackByte’s progression in programming languages from C# to Go and subsequently to C/C++ in the latest version of its encryptor – BlackByteNT – represents a deliberate effort to increase the malware’s resilience against detection and analysis,” the researchers said.
“Complex languages like C/C++ allow for the incorporation of advanced anti-analysis and anti-debugging techniques, which have been observed across the BlackByte tooling during detailed analysis by other security researchers.”
The disclosure comes as Group-IB unpacked the tactics associated with two other ransomware strains tracked as Brain Cipher and RansomHub, underscoring the potential connections of the former with ransomware groups such as EstateRansomware, SenSayQ, and RebornRansomware.
“There are similarities in terms of style and content of the Brain Cipher’s ransom note to those by SenSayQ ransomware,” the Singaporean cybersecurity company said. “The TOR websites of Brain Cipher ransomware group and SenSayQ ransomware group use similar technologies and scripts.”
RansomHub, on the other hand, has been observed recruiting former affiliates of Scattered Spider, a detail that first came to light last month. A majority of the attacks have targeted healthcare, finance, and government sectors in the U.S., Brazil, Italy, Spain, and the U.K.
“For initial access the affiliates usually purchase compromised valid domain accounts from Initial Access Brokers (IABs) and external remote services,” Group-IB said, adding the “accounts have been acquired via LummaC2 stealer.”
“RansomHub’s tactics include leveraging compromised domain accounts and public VPNs for initial access, followed by data exfiltration and extensive encryption processes. Their recent introduction of a RaaS affiliate program and use of high-demand ransom payments illustrate their evolving and aggressive approach.”
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.




![Cobalt Strike Beacon Detected - 179[.]43[.]186[.]234:80 4 Cobalt-Strike](https://www.redpacketsecurity.com/wp-content/uploads/2021/11/Cobalt-Strike-300x201.jpg)
![[PLAY] - Ransomware Victim: All Book Covers 5 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)