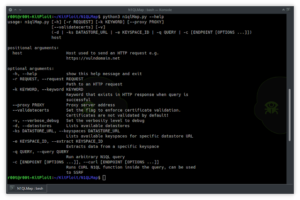
DNSx – A Fast And Multi-Purpose DNS Toolkit Allow To Run Multiple DNS Queries Of Your Choice With A List Of User-Supplied Resolvers
dnsx is a fast and multi-purpose DNS toolkit allow to run multiple probers using retryabledns library, that allows you to...







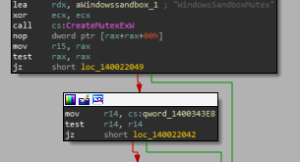







![[BABUK2] - Ransomware Victim: forvismazars[.]com[.]fr ( mazars[.]fr ) By Babuk Locker 2[.]0 25 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)
