China-Linked BadBazaar Android Spyware Targeting Signal and Telegram Users
Cybersecurity researchers have discovered malicious Android apps for Signal and Telegram distributed via the Google Play Store and Samsung Galaxy Store that are engineered to deliver the BadBazaar spyware on infected devices.
Slovakian company ESET attributed the campaign to a China-linked actor called GREF.
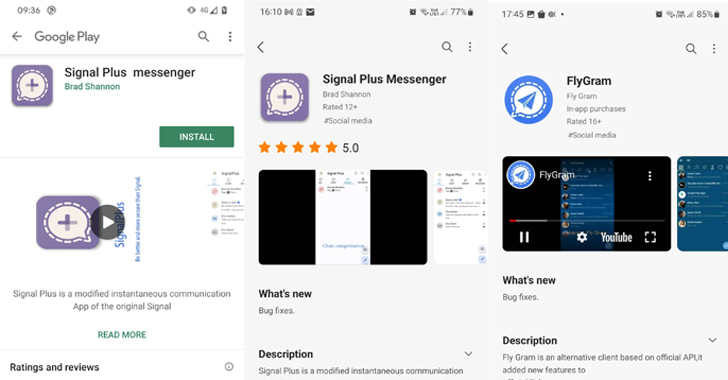
“Most likely active since July 2020 and since July 2022, respectively, the campaigns have distributed the Android BadBazaar espionage code through the Google Play store, Samsung Galaxy Store, and dedicated websites representing the malicious apps Signal Plus Messenger and FlyGram,” security researcher Lukáš Štefanko said in a new report shared with The Hacker News.
Victims have been primarily detected in Germany, Poland, and the U.S., followed by Ukraine, Australia, Brazil, Denmark, Congo-Kinshasa, Hong Kong, Hungary, Lithuania, the Netherlands, Portugal, Singapore, Spain, and Yemen.
BadBazaar was first documented by Lookout in November 2022 as targeting the Uyghur community in China with seemingly benign Android and iOS apps that, once installed, harvests a wide range of data, including call logs, SMS messages, locations, and others.
The earlier campaign, active since at least 2018, is also notable for the fact that the rogue Android apps were never published to the Play Store. Both the apps have since been taken down from google’s app storefront, but they continue to be available on the Samsung Galaxy Store.
The details of the apps are as follows –
- Signal Plus Messenger (org.thoughtcrime.securesmsplus) – 100+ downloads since July 2022, also available via signalplus[.]org
- FlyGram (org.telegram.FlyGram) – 5,000+ downloads since June 2020, also available via flygram[.]org
Beyond these distribution mechanisms, it’s said that potential victims have also been likely tricked into installing the apps from a Uyghur Telegram group focused on sharing Android apps. The group has over 1,300 members.
Both Signal Plus Messenger and FlyGram are designed to collect and exfiltrate sensitive user data, with each app dedicated to also amassing information from the respective apps they mimic: Signal and Telegram.
This includes the ability to access Signal PIN and Telegram chat backups should the victim enable a Cloud Sync feature from the trojanized app.
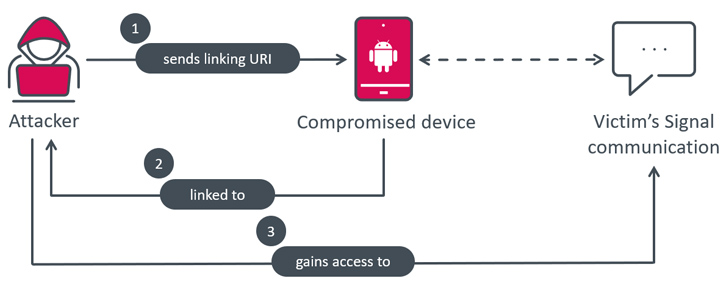
In what’s a novel twist, Signal Plus Messenger represents the first documented case of surveillance of a victim’s Signal communications by covertly linking the compromised device to the attacker’s Signal account without requiring any user interaction.
“BadBazaar, the malware responsible for the spying, bypasses the usual QR code scan and user click process by receiving the necessary URI from its [command-and-control] server, and directly triggering the necessary action when the Link device button is clicked,” Štefanko explained.
“This enables the malware to secretly link the victim’s smartphone to the attacker’s device, allowing them to spy on Signal communications without the victim’s knowledge.”
FlyGram, for its part, also implements a feature called SSL pinning to evade analysis by embedding the certificate within the APK file such that only encrypted communication with the predefined certificate is allowed, thereby making it challenging to intercept and analyze the network traffic between the app and its server.
An examination of the app Cloud Sync feature has further revealed that every user who registers for the service is assigned a distinct ID that’s sequentially incremented. It’s estimated that 13,953 users (including ESET) installed FlyGram and activated the Cloud Sync feature.
ESET said it’s continuing to track GREF as a separate cluster despite prior open-source reporting connecting the group to APT15, citing lack of definitive evidence.
“BadBazaar’s main purpose is to exfiltrate device information, the contact list, call logs, and the list of installed apps, and to conduct espionage on Signal messages by secretly linking the victim’s Signal Plus Messenger app to the attacker’s device,” Štefanko said.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.