Chinese hackers use new custom backdoor to evade detection

The Chinese cyber espionage hacking group Mustang Panda was seen deploying a new custom backdoor named ‘MQsTTang’ in attacks starting this year.
Mustang Panda is an advanced persistent threat (APT) group known to target organizations worldwide in data theft attacks using customized versions of the PlugX malware. The threat actors are also known as TA416 and Bronze President.
Mustang Panda’s new MQsTTang backdoor malware does not appear to be based on previous malware, indicating the hackers likely developed it to evade detection and make attribution harder.
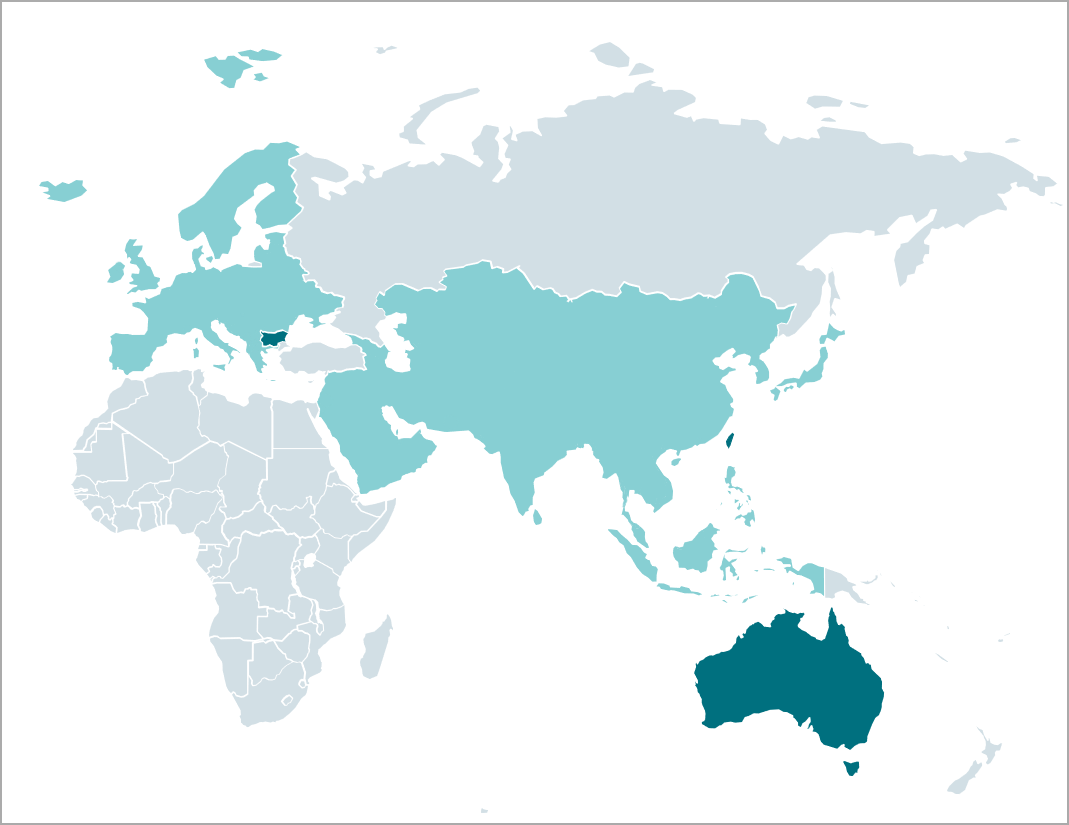
ESET’s researchers discovered MQsTTang in a campaign that started in January 2023 and is still ongoing. The campaign targets government and political organizations in Europe and Asia, focusing on Taiwan and Ukraine.
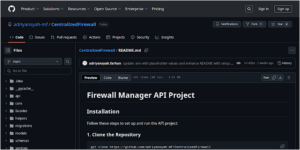
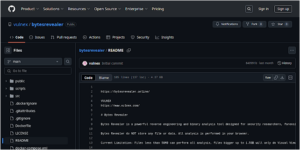
The malware distribution happens through spear-phishing emails, while the payloads are downloaded from GitHub repositories created by a user associated with previous Mustang Panda campaigns.
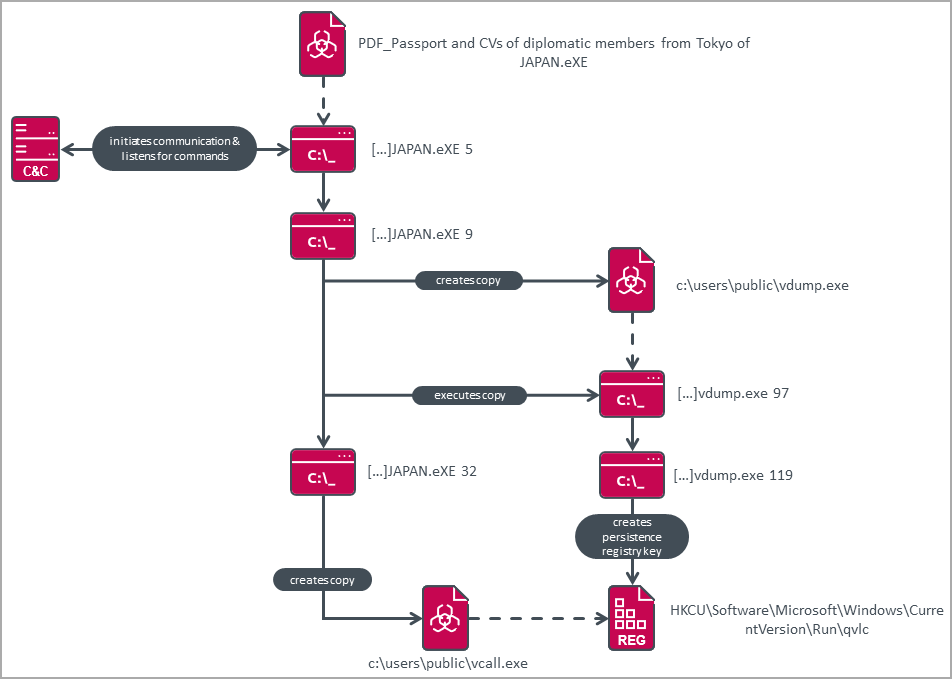
The malware is an executable compressed inside RAR archives, given names with a diplomacy theme, such as scans of passports of members of diplomatic missions, embassy notes, etc.
The new MQsTTang backdoor
ESET characterizes MQsTTang as a “barebones” backdoor that enables the threat actor to execute commands remotely on the victim’s machine and receive their output.
“This new MQsTTang backdoor provides a kind of remote shell without any of the bells and whistles associated with the group’s other malware families,” reads the ESET report.
Upon launch, the malware creates a copy of itself with a command line argument that performs various tasks, such as starting C2 communications, establishing persistence, etc.
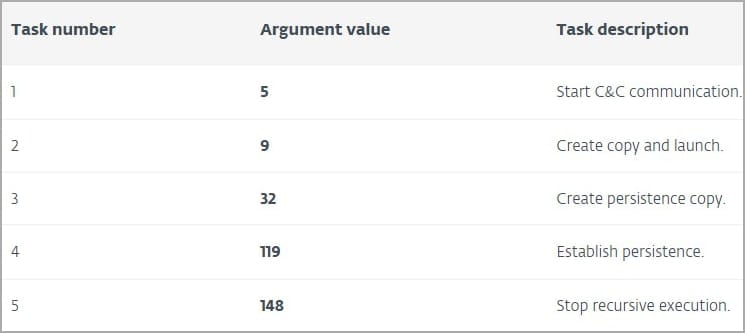
Persistence is established by adding a new registry key under “HKCU\Software\Microsoft\Windows\CurrentVersion\Run,” which launches the malware at system startup. After reboot, only the C2 communication task is executed.
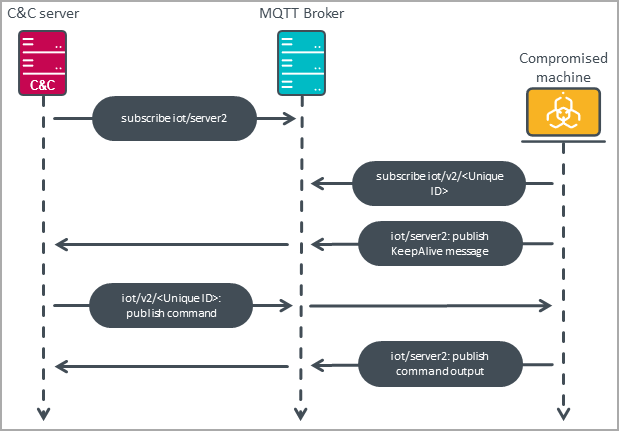
An unusual characteristic of the novel backdoor is using the MQTT protocol for command and control server communications.
MQTT gives the malware good resilience to C2 takedowns, hides the attacker’s infrastructure by passing all communications through a broker, and makes it less likely to be detected by defenders looking for more commonly used C2 protocols.
To evade detection, MQsTTang checks for the presence of debuggers or monitoring tools on the host, and if any are found, it changes its behavior accordingly.
Another recent Mustang Panda operation was observed between March and October 2022 by analysts at Trend Micro, who reported seeing heavy targeting against Australian, Japanese, Taiwanese, and Philippine organizations.
In that campaign, the threat group used three malware strains, namely PubLoad, ToneIns, and ToneShell, which aren’t present in the 2023 campaign spotted by ESET.
Whether or not MQsTTang becomes part of the group’s long-term arsenal or if it was specifically developed for a specific operation remains to be seen.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on Patreon using the button below

To keep up to date follow us on the below channels.





![Cobalt Strike Beacon Detected - 185[.]9[.]146[.]38:80 13 Cobalt-Strike](https://www.redpacketsecurity.com/wp-content/uploads/2021/11/Cobalt-Strike-300x201.jpg)