CISOs Tout SaaS Cybersecurity Confidence, But 79% Admit to SaaS Incidents, New Report Finds
A new State of SaaS Security Posture Management Report from SaaS cybersecurity provider AppOmni indicates that Cybersecurity, IT, and business leaders alike recognize SaaS cybersecurity as an increasingly important part of the cyber threat landscape. And at first glance, respondents appear generally optimistic about their SaaS cybersecurity.
Over 600 IT, cybersecurity, and business leaders at companies between 500-2,500+ employees were surveyed and responded with confidence in their SaaS cybersecurity preparedness and capabilities. For example:
- When asked to rate the SaaS cybersecurity maturity level of their organizations, 71% noted that their organizations’ SaaS cybersecurity maturity has achieved either a mid-high level (43%) or the highest level (28%).
- For the security levels of the SaaS applications authorized for use in their organization, sentiment was similarly high. Seventy-three percent rated SaaS application security as mid-high (41%) or the highest maturity level (32%).
- Remarkably, 85% answered that they are confident or very confident in their company’s or customer’s data security in sanctioned SaaS apps.
But how well are organizations defending themselves against these threats? The pace and severity of SaaS security incidents and breaches tell an entirely different story than respondents’ perception of a secure SaaS environment.
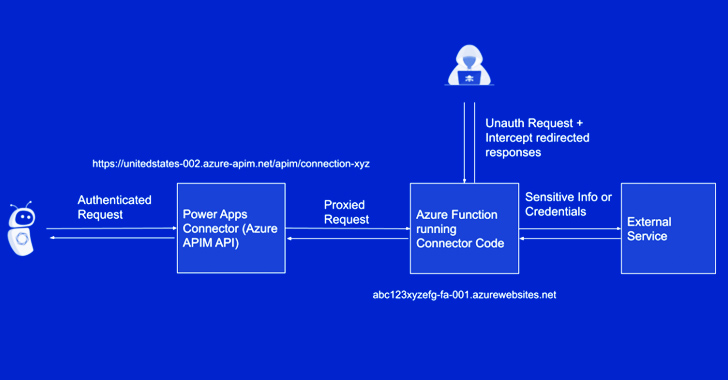
Cybersecurity Teams Should Be Concerned: Only 21% Claimed Zero SaaS Incidents in the Last 12 Months#
Despite trumpeting their perceived SaaS cybersecurity resilience, 79% of respondents confirmed that their organization had identified SaaS cybersecurity incidents over the past 12 months. And many of those incidents occurred in environments with cybersecurity policies in place and enforced, as 66% of respondents claimed in their responses.
SaaS data breaches can devastate organizations in operational disruptions, reputational damage, and the bottom line. A recent IBM report showed that the cost of a data breach now averages $4.45 million in 2023. SecOps teams may quickly be overwhelmed by the challenge of monitoring and securing a diverse SaaS environment that requires real depth of expertise in each application. Responses bear out this reality as the majority of incidents fell into preventable categories such as over permissioned users, app misconfigurations, human and error-related data exposures.
Download AppOmni’s State of SaaS Security Posture Management 2023 Report##
Think your SaaS security is top-notch? We surveyed over 600 global security practitioners, and 79% of professionals felt the same – yet they faced cybersecurity incidents! Dive into the insights of the AppOmni 2023 Report.”
SaaS Cybersecurity Incidents in the Last 12 Months (June 2023)
 |
| Image courtesy of AppOmni |
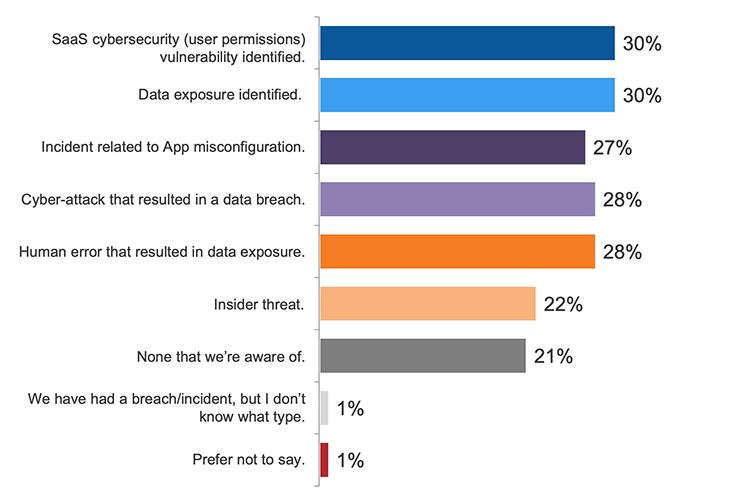
The SaaS Footprint, and its Corresponding Risk, is Grossly Underestimated #
Critical operations in both SMBs and the enterprise increasingly rely on cloud and SaaS infrastructure. Gartner has noted that enterprise spend on SaaS exceeded industry projections in recent years, and enterprises are investing an average of 50% more on SaaS services than Infrastructure-as-a-Service (IaaS) services. Between 2017 to 2022, SaaS-related services grew at a 29% CAGR (compounded annual growth rate).
The flexibility and customizability of SaaS, coupled with economies of scale, make it a game-changer for knowledge-worker productivity. The State of SaaS Security Posture Management Report responses reflect these advantages. Nearly 45% of both North America- and Europe-based respondents reported using more than 100 SaaS apps. Unsurprisingly, larger companies (2,500+ employees) tend to have the highest number of sanctioned SaaS apps in use.
Number of Applications in Use (June 2023)
 |
| Image courtesy of AppOmni |
But SaaS applications carry hidden risks. As SaaS has become the de facto operating system of the enterprise, legacy cybersecurity tools and procedures no longer provide adequate protection. An identity provider (IdP) can be compromised and lead to SaaS data breaches, such as occurred in last year’s 0ktapus phishing scam that targeted Okta credentials. Similarly, mobile device management (MdM) does not secure SaaS apps accessed via mobile devices. And endpoint detection and response (EDR) fail to recognize SaaS as an endpoint.
CASBs (cloud access security brokers) may act as vital cloud security tools, but they don’t offer SaaS protection. While a CASB can inspect network traffic flowing through the proxy, it cannot monitor SaaS-to-SaaS connectivity or third-party SaaS integrations accessed over non-corporate networks.
 |
| Image courtesy of AppOmni |
Three Key SaaS Security Misunderstandings Put Applications at Higher Risk#
SaaS may be as widely used as it is misunderstood. In its report, AppOmni shared three of the most common problem areas in SaaS cybersecurity that lead to avoidable cyber risk.
SaaS Data Security Misconceptions #
AppOmni’s proprietary assessments have identified more than 300 million exposed SaaS data records — a significant portion of which includes PII (personally identifiable information) and other forms of customer data. Recent SaaS security incidents such as the Salesforce Community Site data leaks had significant reach but relatively scant mainstream press coverage and limited awareness among affected organizations.
These examples and AppOmni’s data stand in stark contrast to the 85% of respondents who affirmed a high level of confidence in their organizational or customer SaaS data security. Yet large data breaches can often be traced to a SaaS application (often described as a “third party” in breach reports and publications) with critical misconfigurations, over-permissioning, and exposed data. As continuous SaaS monitoring and attack surface risk mitigation continue to be blind spots for cybersecurity and IT teams, the security misconceptions accordingly persist.
Overconfidence in the Extent of SaaS Cyber Risk Visibility#
While 89% of respondents claimed to perform some type of audit or checklist before procuring a new SaaS application, this stage of SaaS adoption reflects the least amount of risk. Live SaaS environments are in a constant state of change that can, and frequently do, introduce security gaps and unintended configuration. On top of this, vendors continuously launch updates that can inadvertently affect security settings.
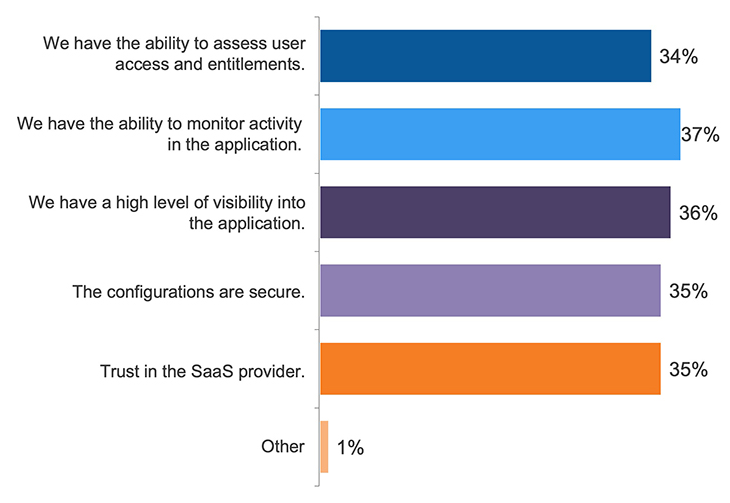
AppOmni’s proprietary research indicates that few organizations have continuous visibility into SaaS applications after pre-procurement due diligence has concluded. Business or application owners with limited security knowledge are then charged with ensuring that the SaaS applications are configured and functioning correctly. These settings do not abide by a universal framework, rendering cybersecurity teams unable to master security settings across all SaaS apps in use. Yet half of respondents believed they had achieved full visibility and monitoring capability of their organizations’ SaaS apps. And 34% claimed they have the ability to assess end-user access and entitlements.
Reasons for SaaS Cybersecurity Confidence (June 2023)
 |
| Image courtesy of AppOmni |
While a subset of SaaS applications can be monitored and assessed individually, the reality of monitoring and assessing end-user access and entitlements — along with ensuring secure configurations on an ongoing basis — is more complicated than respondents’ perception. Maintaining secure SaaS configuration for just one application, let alone dozens or hundreds of apps across an organization, is exceedingly difficult for overwhelmed security organizations with inadequate SaaS security tooling.
Misreading the SaaS Cyber Threat Model#
While SaaS-to-SaaS (sometimes called third-party integrations or third-party apps) connections are a boon to productivity, they’re a bane to security. These ubiquitous apps, which include connecting generative AI tools to SaaS platforms, increase the attack surface risk through the improper exposure of insecure applications or exposed data to threat actors. And 60% of respondents confessed to limited or no ability to monitor and detect these connections.
According to AppOmni, the average enterprise organization has 256 distinct SaaS-to-SaaS connections connecting into a single SaaS instance within an enterprise. These connections represent a pervasive form of shadow IT, with end-users agreeing to link unsanctioned third-party apps to SaaS platforms that store sensitive or confidential data.
What end-users are doing with the data accessed by apps, since there’s no overarching security monitoring platform, is often unknown. More concerningly, dormant SaaS-to-SaaS apps retain read and write privileges, making them attractive targets to threat actors to gain entry to an organization’s information system. Inventorying and continuously monitoring sanctioned and sanctioned SaaS-to-SaaS connections requires advanced security tooling that many cybersecurity and IT teams lack.
Lack of SaaS Compliance Monitoring Presents Further Risk to Organizations Operating in Advanced Economies#
Global Compliance Requirements
 |
| Image courtesy of AppOmni |
Maintaining compliance with regional and international regulations such as GDPR, HIPAA, CCPA, APPI, and industry-specific standards also proved challenging for the research study participants. With a cohort based in North America (U.S.), Europe (UK, France, and Germany), and APAC (Japan and Australia), abiding by legislation that carries stiff fines and consequences for noncompliance should be a top cybersecurity priority.
Yet half of respondents rely on recurring or ad hoc manual SaaS audits. As compliance requirements evolve, manual and piecemeal efforts likely won’t be capable of achieving these evolving mandates, with the shift to on-demand compliance reporting underway.
For example, Australia’s APRA CPS 234 standards now require organizations under its purview to “maintain an information security capability commensurate with the size and extent of the threats to its information assets.” They must also “implement controls to protect said information assets commensurate with the criticality and sensitivity of those information assets” that SaaS native security settings and an overwhelmed cybersecurity/IT organization can’t meet alone.
Similarly, the UK National Cyber Security Centre (NCSC) Cyber Essentials updates now include SaaS security in its scope. Specifically, organizations governed by Cyber Essentials are responsible for implementing necessary controls and ensuring SaaS applications are securely configured in perpetuity. This responsibility does not fall on the SaaS vendor.
Once more, survey respondents’ confidence appears based on sentiment, not the maturity of their SaaS cybersecurity organization or consistent enforcement of policies.
How Can Security Leaders Strengthen SaaS Cybersecurity? Invest in the Right Tools and a Robust SaaS Cybersecurity Program#
SaaS adoption will likely continue to outpace the ability of cybersecurity teams to secure their organization’s critical data. Manual checks and compliance measures will not suffice, despite the confidence survey respondents appear to have in such measures.
To detect any abnormal or inappropriate activity such as suspicious logins, brute force attempts, and data access or deletion consider adopting a SaaS Security Posture Management (SSPM) tool. SSPM provides continuous monitoring of each SaaS app across the entire SaaS estate. This provides security and risk leaders with the advanced SaaS cybersecurity tooling needed to proactively address SaaS misconfigurations or data exposure risks as they arise. Security teams can also monitor and manage all SaaS-to-SaaS connections, including unsanctioned SaaS-to-SaaS connections.
Not all SSPM solutions are created equal. Carefully and methodically evaluate SSPM vendors to ensure they fully address prevention and detection measures your organization needs.
Of course, the best SSPM solution requires the right people, processes, technology, and commitment to be effective. Such a transformation doesn’t happen overnight. Organizations of all sizes should consider building a SaaS cybersecurity program.
A properly resourced SaaS cybersecurity program will reduce the risk of SaaS-related data breaches, scale SaaS cybersecurity as organizational usage grows, automate compliance and risk reporting, and realize cost savings and operational efficiencies across the SaaS estate. This requires a long-term investment of internal resources, with most enterprise SaaS cybersecurity programs realizing immediate value after implementation, but typically reaching full maturity between 12 – 18 months from kick-off.
Tackling SaaS app security on a manual and piecemeal basis leaves organizations vulnerable to significant cyber risk being exploited by threat actors. SSPM coupled with a robust SaaS cybersecurity program is the best method for elevating the importance of dedicated and proactive SaaS security posture management to reduce the SaaS attack surface. Only with an SSPM solution and SaaS cybersecurity program can you shift perceptions of confidence to actual SaaS cybersecurity confidence.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.