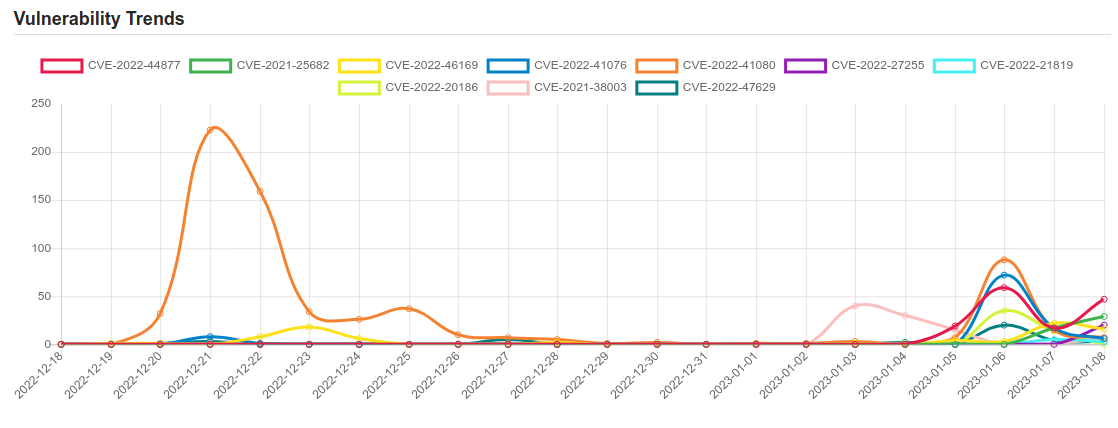
Daily Vulnerability Trends: Mon Jan 09 2023
| CVE NAME | CVE Description |
| CVE-2022-37958 | SPNEGO Extended Negotiation (NEGOEX) Security Mechanism Information Disclosure Vulnerability. |
| CVE-2022-46689 | A race condition was addressed with additional validation. This issue is fixed in tvOS 16.2, macOS Monterey 12.6.2, macOS Ventura 13.1, macOS Big Sur 11.7.2, iOS 15.7.2 and iPadOS 15.7.2, iOS 16.2 and iPadOS 16.2, watchOS 9.2. An app may be able to execute arbitrary code with kernel privileges. |
| CVE-2022-45913 | An issue was discovered in Zimbra Collaboration (ZCS) 9.0. XSS can occur via one of attributes in webmail URLs to execute arbitrary JavaScript code, leading to information disclosure. |
| CVE-2022-41082 | Microsoft Exchange Server Remote Code Execution Vulnerability. |
| CVE-2022-33942 | Protection mechanism failure in the Intel(R) DCM software before version 5.0 may allow an unauthenticated user to potentially enable escalation of privilege via adjacent access. |
| CVE-2021-4308 | A vulnerability was found in WebPA up to 3.1.1. It has been rated as critical. This issue affects some unknown processing. The manipulation leads to sql injection. Upgrading to version 3.1.2 is able to address this issue. The name of the patch is 8836c4f549181e885a68e0e7ca561fdbcbd04bf0. It is recommended to upgrade the affected component. The identifier VDB-217637 was assigned to this vulnerability. |
| CVE-2022-40127 | A vulnerability in Example Dags of Apache Airflow allows an attacker with UI access who can trigger DAGs, to execute arbitrary commands via manually provided run_id parameter. This issue affects Apache Airflow Apache Airflow versions prior to 2.4.0. |
| CVE-2023-0111 | Cross-site Scripting (XSS) – Stored in GitHub repository usememos/memos prior to 0.10.0. |
| CVE-2022-41040 | Microsoft Exchange Server Elevation of Privilege Vulnerability. |
| CVE-2021-25682 | It was discovered that the get_pid_info() function in data/apport did not properly parse the /proc/pid/status file from the kernel. |
| CVE-2022-46169 | Cacti is an open source platform which provides a robust and extensible operational monitoring and fault management framework for users. In affected versions a command injection vulnerability allows an unauthenticated user to execute arbitrary code on a server running Cacti, if a specific data source was selected for any monitored device. The vulnerability resides in the `remote_agent.php` file. This file can be accessed without authentication. This function retrieves the IP address of the client via `get_client_addr` and resolves this IP address to the corresponding hostname via `gethostbyaddr`. After this, it is verified that an entry within the `poller` table exists, where the hostname corresponds to the resolved hostname. If such an entry was found, the function returns `true` and the client is authorized. This authorization can be bypassed due to the implementation of the `get_client_addr` function. The function is defined in the file `lib/functions.php` and checks serval `$_SERVER` variables to determine the IP address of the client. The variables beginning with `HTTP_` can be arbitrarily set by an attacker. Since there is a default entry in the `poller` table with the hostname of the server running Cacti, an attacker can bypass the authentication e.g. by providing the header `Forwarded-For: |
| CVE-2022-41076 | PowerShell Remote Code Execution Vulnerability. |
| CVE-2022-41080 | Microsoft Exchange Server Elevation of Privilege Vulnerability. This CVE ID is unique from CVE-2022-41123. |
| CVE-2022-27255 | In Realtek eCos RSDK 1.5.7p1 and MSDK 4.9.4p1, the SIP ALG function that rewrites SDP data has a stack-based buffer overflow. This allows an attacker to remotely execute code without authentication via a crafted SIP packet that contains malicious SDP data. |
| CVE-2022-21819 | NVIDIA distributions of Jetson Linux contain a vulnerability where an error in the IOMMU configuration may allow an unprivileged attacker with physical access to the board direct read/write access to the entire system address space through the PCI bus. Such an attack could result in denial of service, code execution, escalation of privileges, and impact to data integrity and confidentiality. The scope impact may extend to other components. |
|
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.  To keep up to date follow us on the below channels.     |

