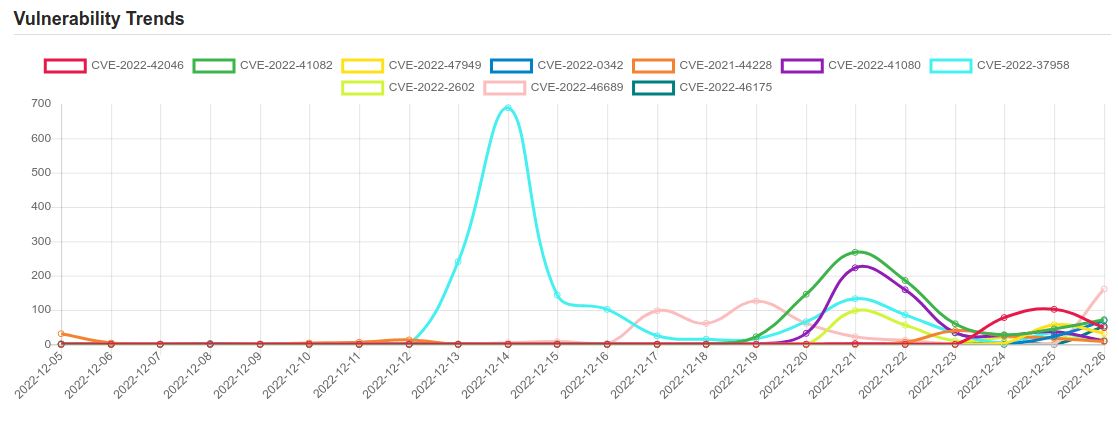
Daily Vulnerability Trends: Tue Dec 27 2022
| CVE NAME | CVE Description |
| CVE-2022-2602 | No description provided |
| CVE-2022-46689 | A race condition was addressed with additional validation. This issue is fixed in tvOS 16.2, macOS Monterey 12.6.2, macOS Ventura 13.1, macOS Big Sur 11.7.2, iOS 15.7.2 and iPadOS 15.7.2, iOS 16.2 and iPadOS 16.2, watchOS 9.2. An app may be able to execute arbitrary code with kernel privileges. |
| CVE-2022-46175 | JSON5 is an extension to the popular JSON file format that aims to be easier to write and maintain by hand (e.g. for config files). The `parse` method of the JSON5 library before and including version `2.2.1` does not restrict parsing of keys named `__proto__`, allowing specially crafted strings to pollute the prototype of the resulting object. This vulnerability pollutes the prototype of the object returned by `JSON5.parse` and not the global Object prototype, which is the commonly understood definition of Prototype Pollution. However, polluting the prototype of a single object can have significant security impact for an application if the object is later used in trusted operations. This vulnerability could allow an attacker to set arbitrary and unexpected keys on the object returned from `JSON5.parse`. The actual impact will depend on how applications utilize the returned object and how they filter unwanted keys, but could include denial of service, cross-site scripting, elevation of privilege, and in extreme cases, remote code execution. `JSON5.parse` should restrict parsing of `__proto__` keys when parsing JSON strings to objects. As a point of reference, the `JSON.parse` method included in JavaScript ignores `__proto__` keys. Simply changing `JSON5.parse` to `JSON.parse` in the examples above mitigates this vulnerability. This vulnerability is patched in json5 version 2.2.2 and later. |
| CVE-2022-42821 | A logic issue was addressed with improved checks. This issue is fixed in macOS Monterey 12.6.2, macOS Big Sur 11.7.2, macOS Ventura 13. An app may bypass Gatekeeper checks. |
| CVE-2022-33679 | Windows Kerberos Elevation of Privilege Vulnerability. This CVE ID is unique from CVE-2022-33647. |
| CVE-2022-29455 | DOM-based Reflected Cross-Site Scripting (XSS) vulnerability in Elementor’s Elementor Website Builder plugin <= 3.5.5 versions. |
| CVE-2018-17463 | Incorrect side effect annotation in V8 in Google Chrome prior to 70.0.3538.64 allowed a remote attacker to execute arbitrary code inside a sandbox via a crafted HTML page. |
| CVE-2022-40602 | A flaw in the Zyxel LTE3301-M209 firmware verisons prior to V1.00(ABLG.6)C0 could allow a remote attacker to access the device using an improper pre-configured password if the remote administration feature has been enabled by an authenticated administrator. |
| CVE-2021-1732 | Windows Win32k Elevation of Privilege Vulnerability This CVE ID is unique from CVE-2021-1698. |
| CVE-2022-44015 | An issue was discovered in Simmeth Lieferantenmanager before 5.6. An attacker can inject raw SQL queries. By activating MSSQL features, the attacker is able to execute arbitrary commands on the MSSQL server via the xp_cmdshell extended procedure. |
| CVE-2021-24891 | The Elementor Website Builder WordPress plugin before 3.4.8 does not sanitise or escape user input appended to the DOM via a malicious hash, resulting in a DOM Cross-Site Scripting issue. |
| CVE-2019-16891 | Liferay Portal CE 6.2.5 allows remote command execution because of deserialization of a JSON payload. |
| CVE-2022-41040 | Microsoft Exchange Server Elevation of Privilege Vulnerability. |
| CVE-2022-42046 | WFS, Inc HeavenBurnsRed 2020.3.15.7141260 is vulnerable to Local Privilege Escalation. |
| CVE-2022-41082 | Microsoft Exchange Server Remote Code Execution Vulnerability. |
|
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.  To keep up to date follow us on the below channels.     |

