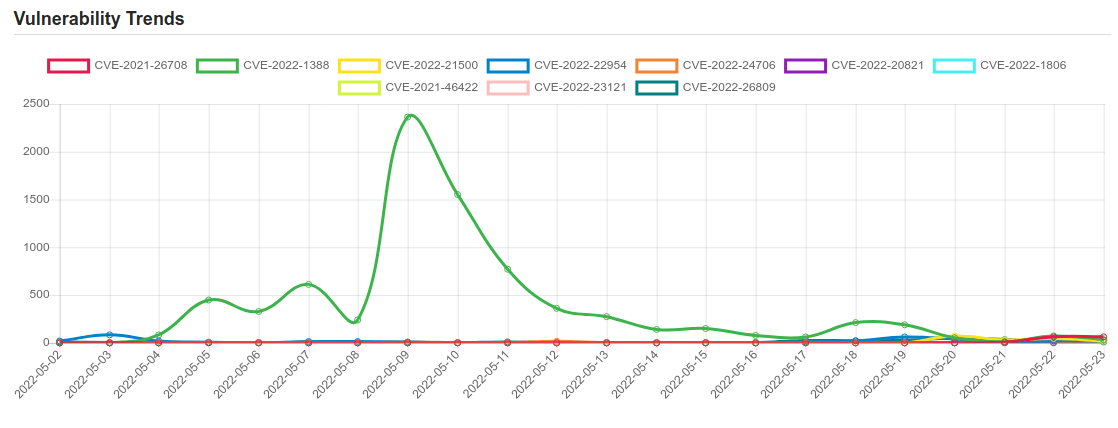
Daily Vulnerability Trends: Tue May 24 2022
| CVE NAME | CVE Description |
| CVE-2022-22972 | VMware Workspace ONE Access, Identity Manager and vRealize Automation contain an authentication bypass vulnerability affecting local domain users. A malicious actor with network access to the UI may be able to obtain administrative access without the need to authenticate. |
| CVE-2022-29383 | NETGEAR ProSafe SSL VPN firmware FVS336Gv2 and FVS336Gv3 was discovered to contain a SQL injection vulnerability via USERDBDomains.Domainname at cgi-bin/platform.cgi. |
| CVE-2021-3929 | No description provided |
| CVE-2022-1183 | On vulnerable configurations, the named daemon may, in some circumstances, terminate with an assertion failure. Vulnerable configurations are those that include a reference to http within the listen-on statements in their named.conf. TLS is used by both DNS over TLS (DoT) and DNS over HTTPS (DoH), but configurations using DoT alone are unaffected. Affects BIND 9.18.0 -> 9.18.2 and version 9.19.0 of the BIND 9.19 development branch. |
| CVE-2022-1813 | OS Command Injection in GitHub repository yogeshojha/rengine prior to 1.2.0. |
| CVE-2022-26923 | Active Directory Domain Services Elevation of Privilege Vulnerability. |
| CVE-2022-1388 | On F5 BIG-IP 16.1.x versions prior to 16.1.2.2, 15.1.x versions prior to 15.1.5.1, 14.1.x versions prior to 14.1.4.6, 13.1.x versions prior to 13.1.5, and all 12.1.x and 11.6.x versions, undisclosed requests may bypass iControl REST authentication. Note: Software versions which have reached End of Technical Support (EoTS) are not evaluated |
| CVE-2022-21500 | Vulnerability in Oracle E-Business Suite (component: Manage Proxies). Supported versions that are affected are 12.1 and 12.2. Easily exploitable vulnerability allows unauthenticated attacker with network access via HTTP to compromise Oracle E-Business Suite. Successful attacks of this vulnerability can result in unauthorized access to critical data or complete access to all Oracle E-Business Suite accessible data. Note: Authentication is required for successful attack, however the user may be self-registered. CVSS 3.1 Base Score 7.5 (Confidentiality impacts). CVSS Vector: (CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N). |
| CVE-2022-22954 | VMware Workspace ONE Access and Identity Manager contain a remote code execution vulnerability due to server-side template injection. A malicious actor with network access can trigger a server-side template injection that may result in remote code execution. |
| CVE-2022-24706 | In Apache CouchDB prior to 3.2.2, an attacker can access an improperly secured default installation without authenticating and gain admin privileges. The CouchDB documentation has always made recommendations for properly securing an installation, including recommending using a firewall in front of all CouchDB installations. |
| CVE-2022-20821 | No description provided |
| CVE-2022-1806 | Cross-site Scripting (XSS) – Reflected in GitHub repository rtxteam/rtx prior to checkpoint_2022-05-18. |
| CVE-2021-46422 | Telesquare SDT-CW3B1 1.1.0 is affected by an OS command injection vulnerability that allows a remote attacker to execute OS commands without any authentication. |
| CVE-2022-23121 | No description provided |
| CVE-2022-26809 | Remote Procedure Call Runtime Remote Code Execution Vulnerability. This CVE ID is unique from CVE-2022-24492, CVE-2022-24528. |
| CVE-2022-1809 | Access of Uninitialized Pointer in GitHub repository radareorg/radare2 prior to 5.7.0. |
| CVE-2022-31245 | mailcow before 2022-05d allows a remote authenticated user to inject OS commands and escalate privileges to domain admin via the –debug option in conjunction with the —PIPEMESS option in Sync Jobs. |
| CVE-2022-27254 | The remote keyless system on Honda Civic 2018 vehicles sends the same RF signal for each door-open request, which allows for a replay attack, a related issue to CVE-2019-20626. |
| CVE-2022-26717 | No description provided |
| CVE-2021-26708 | CVE-2021-26708 – Linux Kernel Organization / Linux kernel – Improper privilege management |
If you like the site, please consider joining the telegram channel and supporting us on Patreon using the button below.


