Ethereum feature abused to steal $60 million from 99K victims

Malicious actors have been abusing Ethereum’s ‘Create2’ function to bypass wallet security alerts and poison cryptocurrency addresses, which led to stealing $60,000,000 worth of cryptocurrency from 99,000 people in six months.
This is reported by Web3 anti-scam specialists at ‘Scam Sniffer,’ who observed several cases of in-the-wild exploitation of the function, in some cases losses incurred by one individual reaching up to $1.6 million.
Legitimate function
Create2 is an opcode in Ethereum, introduced in the ‘Constantinople’ upgrade, that allows creating smart contracts on the blockchain.
Unlike the original Create opcode, which generated new addresses based on the creator’s address and nonce, Create2 allows calculating addresses before the deployment of the contract.
It’s a powerful tool for Ethereum developers, enabling advanced and flexible contract interactions, parameter-based contract address pre-calculation, deployment flexibility, suitability for off-chain transactions and certain dApps.
Create2 introduced significant benefits, but several security implications and new attack vectors also came along with them.
Create2 opcode abuse
Scam Sniffer’s report explains that Create2 can be abused to generate fresh contract addresses with no history of malicious/reported transactions, hence bypassing wallet security alerts.
When a victim signs a malicious transaction, the attacker deploys a contract at the pre-calculated address and transfers the victim’s assets to it, a non-reversible process.
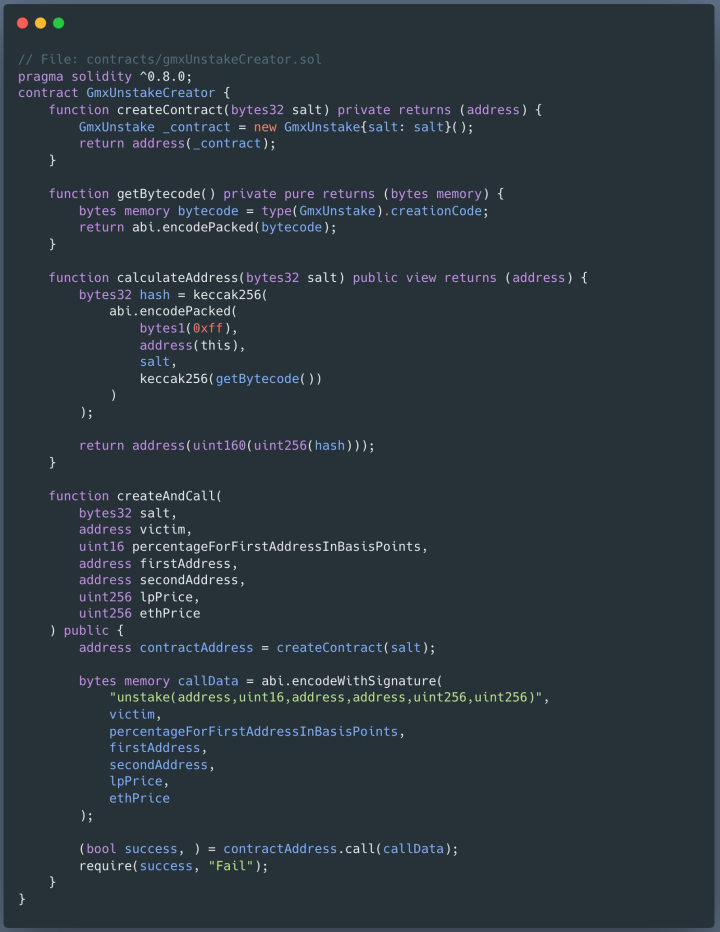
In a recent case analysts observed, a victim lost $927,000 worth of GMX after they were tricked into signing a transfer contract that sent the assets to a pre-computed address.
The second type of Create2 abuse is generating addresses similar to legitimate ones owned by the recipient, thus tricking users into sending assets to the threat actors, thinking they’re sending it to a known address.
The scheme, which is named ‘address poisoning,’ involves generating a large number of addresses and then picking those that match their specific phishing needs each time to trick their targets.
Since August 2023, Scam Sniffer has recorded 11 victims losing nearly $3 million, with one of them transferring $1.6 million to an address resembling one they had sent money to recently.
Most of these attacks went under the radar, silently siphoning millions, but some have caught the attention of the community.
At the beginning of the year, MetaMask warned about scammers using freshly-generated addresses that match those used by the victim in recent transactions.
In the scam, the threat actor may also send the victim a small amount in crypto to register the address in the wallet’s history, thus increasing the chances of the victim making the payment.
In early August 2023, a Binance operator mistakenly sent $20 million to scammers who employed the ‘address poisoning’ trick but noticed the error quickly and froze the recipient’s address.
Notably, using lookalike cryptocurrency addresses is a trick seen in clipboard-hijacking malware tools, like the Laplas Clipper, highlighting the method’s effectiveness.
When performing cryptocurrency transactions, it is always recommended to check the recipient’s address thoroughly, and not just the first and last three-four characters, before approving it.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.

