Fake 401k Year End Statements Used To Steal Corporate Credentials

Threat actors are using communication about personal pension accounts (the 401(k) plans in the U.S.), salary adjustments, and performance reports to steal company employees’ credentials.
Email security company Cofense warns that these attacks are becoming more frequent and even organizations with sound email security practices are having trouble against them.
Bogus 401k notices
401(k) is a popular retirement savings plan in the U.S. that offers a convenient way for employees to save for the future with tax benefits, often including additional contributions from their employer.
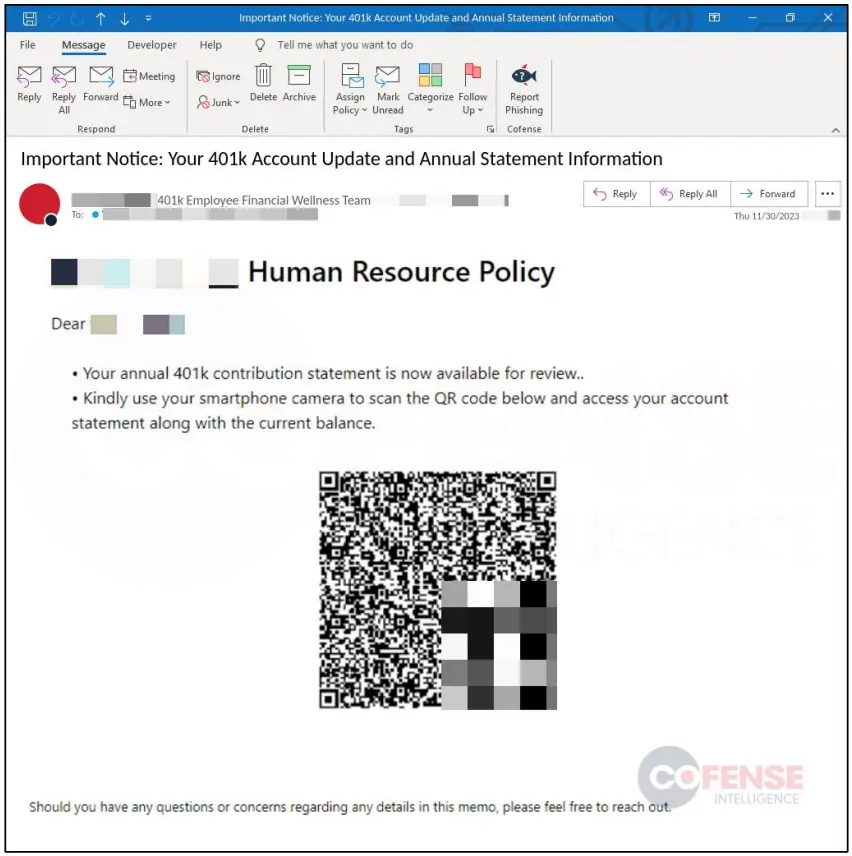
Cybercriminals take advantage of this topic and are sending targets 401(k) notifications posing as someone from their company’s Human Resources department alleging an important plan update or an increase in contributions.
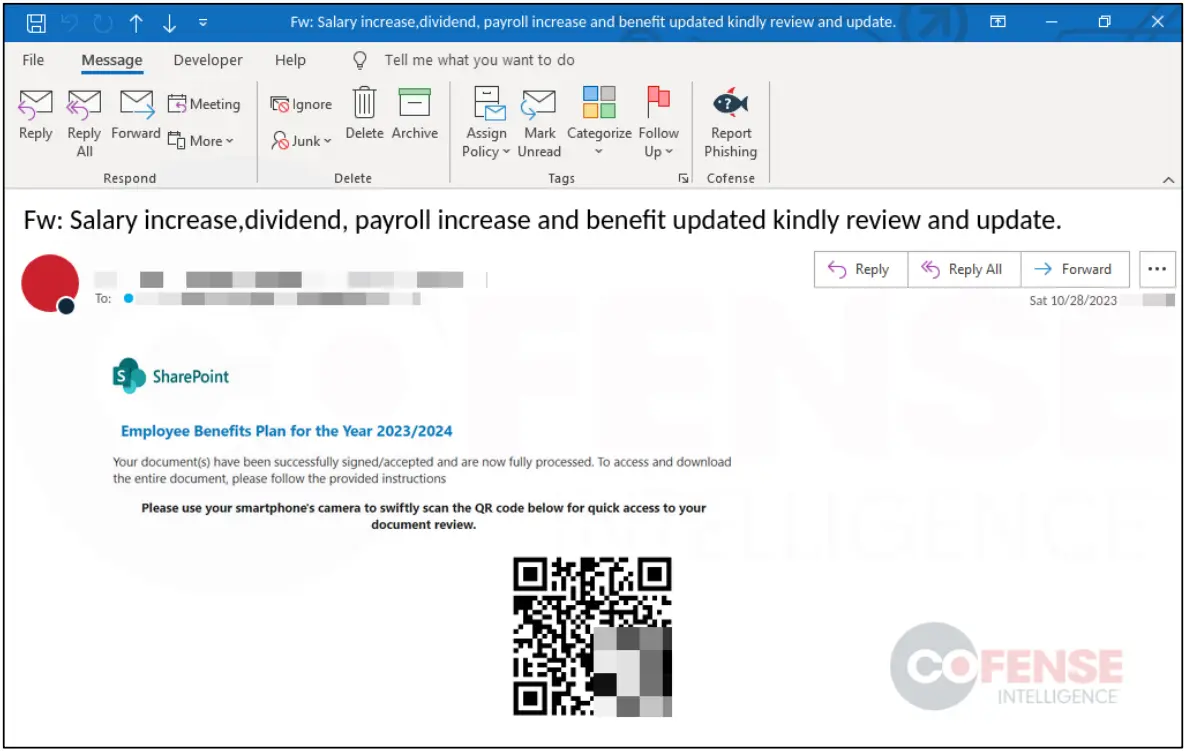
Cofense says that throughout last year it has seen a sharp rise in QR codes embedded in those phishing emails, taking recipients to a fake login page designed to steal credentials.
Other lure types seen more often towards the end of the year include open enrollment, surveys, and salary restructuring communications.
Open enrollment is a specific period, typically occurring towards the end of the calendar year, allowing employees to enroll in health insurance or retirement plans. Recipients take these messages very seriously because failing to enroll before the deadline results in loss of eligibility for some benefits until the next enrollment round.
Cybercriminals also appear to use more often lures regarding compensation adjustments, especially about bonuses and increases, which are usually decided at the end of the year.
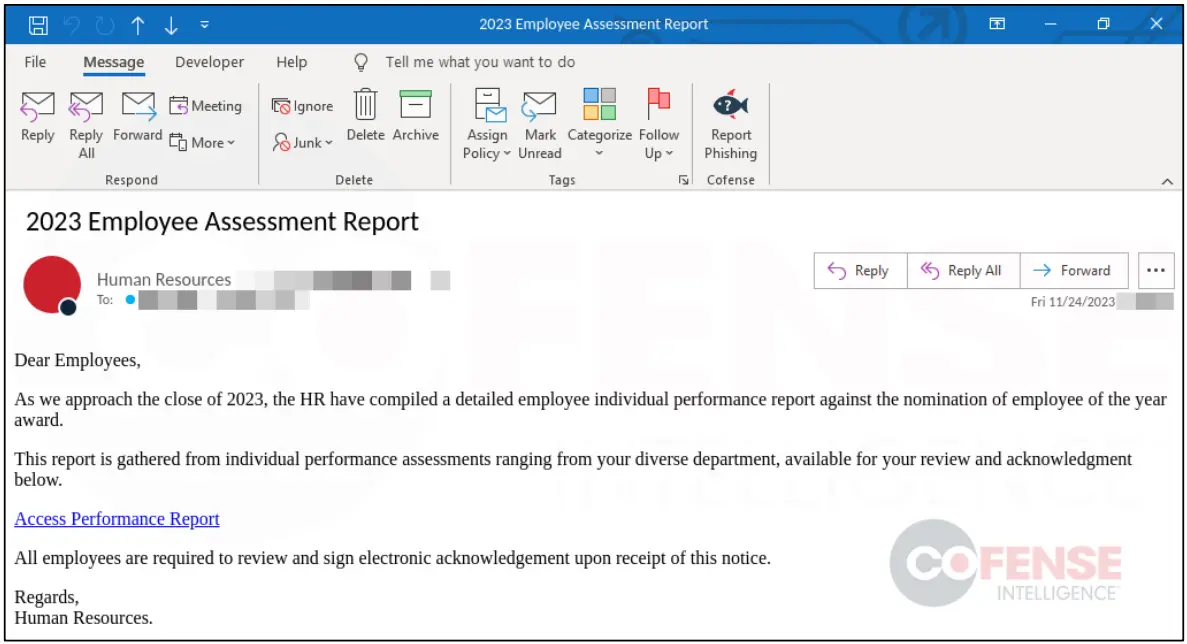
Finally, Cofense warns about fake employee satisfaction surveys and assessment reports sent to targets from spoofed human resource departments.
In one example, the phishing email uses an “employee of the year award” theme to trick recipients into opening their performance reports, allegedly to review and sign them.
Defense tips
Cofense says that all examples in its report are from employees of large enterprises that use effective email security solutions, yet many phishing messages still reach their employees’ inboxes.
The security company suggests that HR departments schedule these communications and inform the personnel accordingly to help filter out at least some of the malicious communications.
However, considering that many companies outsource these operations, educating and safeguarding employees from phishing attempts may be difficult.
Another measure would be to avoid QR codes in legitimate business communication, since many phishing campaigns rely on them.
