iOS Mail bug allows remote zero-click attacks
On Monday, ZecOps released a report about a couple concerning vulnerabilities with the Mail app in iOS. These vulnerabilities would allow an attacker to execute arbitrary code in the Mail app or the maild process that assists the Mail app behind the scenes. Most concerning, though, is the fact that even the most current version of iOS, 13.4.1, is vulnerable.
The way the attack works is that the threat actor sends an email message designed to cause a buffer overflow in Mail (or maild). A buffer overflow is a bug in code that allows an attack to happen if the threat actor is able to fill a block of memory beyond its capacity. Essentially, the attacker writes garbage data that fills up the memory, then writes code that overwrites existing code in adjoining memory, which later gets executed by the vulnerable process.
The bad news
The vulnerabilities disclosed by ZecOps would allow an attacker to use such a buffer overflow to attack an iOS device remotely, on devices running iOS 6 through iOS 13.4.1. (ZecOps writes that it may work on even older versions of iOS, but they did not test that.)
On iOS 12, the attack requires nothing more than viewing a malicious email message in the Mail app. It would not require tapping a link or any other content within the message. On iOS 13, the situation is worse, as the attack can be carried out against the maild process in the background, without requiring any user interaction (ie, it is a “zero-click vulnerability”).
In the case of infection on iOS 13, there would be no significant sign of infection, other than temporary slowness of the Mail app. In some cases, evidence of a failed attack may be present in the form of messages that have no content and cannot be displayed.
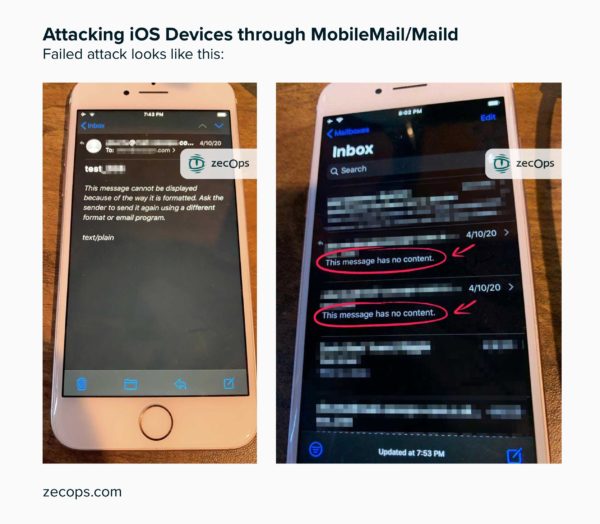
The messages—shown in the image above from the ZecOps blog—may be visible for a limited time. Once an attack is successful, the attacker would presumably use access to the Mail app to delete these messages, so the user may never see them.
The good news
I know how this sounds. This is an attack that can be carried out by any threat actor who has your email address, on the latest version of iOS, and the infection happens in the background without requiring action from the user. How is there good news here?!
Fortunately, there is. The vulnerabilities revealed by ZecOps only allow an attack of the Mail app itself. Using those vulnerabilities, an attacker would be able to capture your email messages, as well as modify and delete messages. Presumably the attacker would also be able to conduct other normal Mail operations, such as sending messages from your email address, although this was not mentioned. While this isn’t exactly comforting, it falls far short of compromising the entire device.
In order to achieve a full device compromise, the attacker would need to have another vulnerability. This means that if you have version 13.4.1, it would require a publicly unknown vulnerability, which would for the most part restrict such an attack to a nation-state-level adversary.
In other words, someone would have to be willing to risk burning a zero-day vulnerability, worth potentially a million dollars or more, to infect your phone. This means that you’re unlikely to be infected unless some hostile government or other powerful group is interested in spying on you.
If you are, for example, a human rights advocate working against a repressive regime, or a member of an oppressed minority in such a country, you may be a target. Similarly, if you are a journalist covering such news, you may be a target. You could also be at risk if you are an important business person, such as a CEO or CFO at a major corporation, or hold an important role in the government. The average person will not be at significant risk from this kind of attack.
Why disclose now?
It is common practice as part of “responsible disclosure” to avoid public mention of a major vulnerability until after it has been fixed, or until sufficient time has passed that it is believed the software or hardware vendor does not intend to fix the vulnerability in a timely fashion. Release of this kind of information before a fix is available can lead to increased danger to users, as hackers who learn that a vulnerability exists can find it for themselves.
Of course, this must be balanced against the risk of existing attacks that are going undetected. Disclosure can help people who are under active attack to discover the problem, and can help people who are not yet under attack learn how to prevent an attack.
With this in mind, ZecOps mentioned three reasons why they chose to disclose now:
- Since the disclosed vulnerabilities can’t be used to compromise the entire device without additional vulnerabilities, the risk of disclosure is lower.
- Apple has released a beta of iOS 13.4.5, which addresses the issue. Although a fix in beta is not exactly the same as a fix in a public release, the changes in the beta could be analyzed by an attacker, which would lead to discovery of the vulnerabilities. Essentially, the vulnerabilities have been disclosed to malicious hackers already, but the public was unaware.
- At least six organizations were under active attack using these vulnerabilities. (The organizations were not named.)
What you should do
First, don’t panic. As mentioned, this is not a widespread attack against everyone using an iPhone. There have been other zero-click vulnerabilities used to push malware onto iPhones in the past, yet none have ever been widespread. This is because the more widespread such an attack becomes, the more likely it is to be spotted, and subsequently fixed by Apple.
To protect their investment in million-dollar iOS zero-day vulnerabilities, powerful organizations use those vulnerabilities sparingly, only against targeted individuals or groups. Thus, unless you’re someone who might be targeted by a hostile nation or other powerful organization, you’re not likely to be in danger.
However, the risk does increase following disclosure, as malicious hackers can discover and use the vulnerability to attack Mail, at least. So you shouldn’t ignore the risk, either.
As much as I’d like to say, “Install Malwarebytes, run a scan, and remove the malware,” I can’t. Unlike macOS, installing antivirus software isn’t possible on iOS, due to Apple restrictions. So there is no software that can scan an iPhone or iPad for malware.
This, plus the lack of noticeable symptoms, means that it will be difficult to determine whether you’ve been affected. As always with iOS, if you have reason to believe you’ve been infected, your only option is to reset your device to factory state and set it up again from scratch as if it were a new device.
As for precautions to avoid infection, there are a couple things you can do. One would be to install the iOS 13.4.5 beta, which contains a fix for the bug. This is not something that’s easy to do, however, as you need an Apple developer account to download the beta. Plus, using a beta version of iOS, which may have bugs, isn’t recommended for all users.
The other possible security measure would be to disable Mail until the next version of iOS is released publicly. To do so, open the Settings app and scroll down to Password & Accounts. Tap that, then look at the list of accounts.
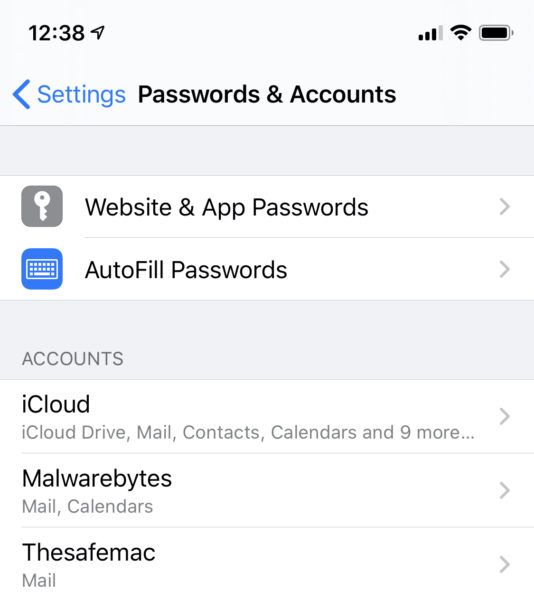
You may have multiple accounts, as shown above, or only one. For any accounts that say “Mail” underneath, that means that you’re using Mail to download mail for that account. Tap on each account, and on the next screen, look for the Mail toggle.

The image above shows that Mail is enabled. Toggle the switch to off. Do this for each of your accounts, and do not switch Mail back on again until you’ve updated to a version of iOS newer than 13.4.1.
Stay safe, everyone!
The post iOS Mail bug allows remote zero-click attacks appeared first on Malwarebytes Labs.


