Malicious npm Packages Mimicking ‘noblox.js’ Compromise Roblox Developers’ Systems
Roblox developers are the target of a persistent campaign that seeks to compromise systems through bogus npm packages, once again underscoring how threat actors continue to exploit the trust in the open-source ecosystem to deliver malware.
“By mimicking the popular ‘noblox.js’ library, attackers have published dozens of packages designed to steal sensitive data and compromise systems,” Checkmarx researcher Yehuda Gelb said in a technical report.
Details about the campaign were first documented by ReversingLabs in August 2023 as part of a campaign that delivered a stealer called Luna Token Grabber, which it said was a “replay of an attack uncovered two years ago” in October 2021.
Since the start of the year, two other packages called noblox.js-proxy-server and noblox-ts were identified as malicious and impersonating the popular Node.js library to deliver stealer malware and a remote access trojan named Quasar RAT.
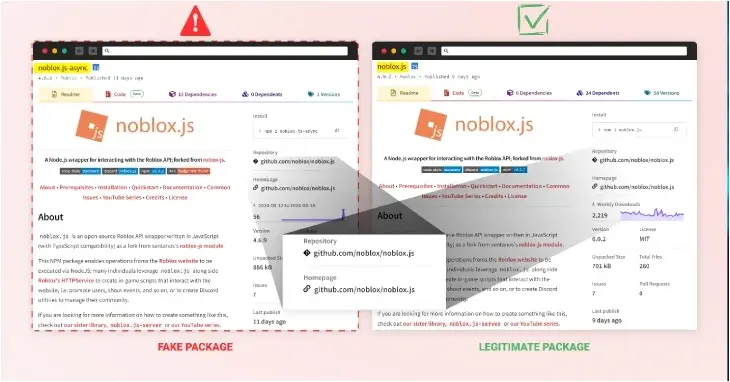
“The attackers of this campaign have employed techniques including brandjacking, combosquatting, and starjacking to create a convincing illusion of legitimacy for their malicious packages,” Gelb said,
To that end, the packages are given a veneer of legitimacy by naming them noblox.js-async, noblox.js-thread, noblox.js-threads, and noblox.js-api, giving the impression to unsuspecting developers that these libraries are related to the legitimate “noblox.js” package.
The package download stats are listed below –
- noblox.js-async (74 downloads)
- noblox.js-thread (117 downloads)
- noblox.js-threads (64 downloads)
- noblox.js-api (64 downloads)
Another technique employed is starjacking, in which the phony packages list the source repository as that of the actual noblox.js library to make it seem more reputable.
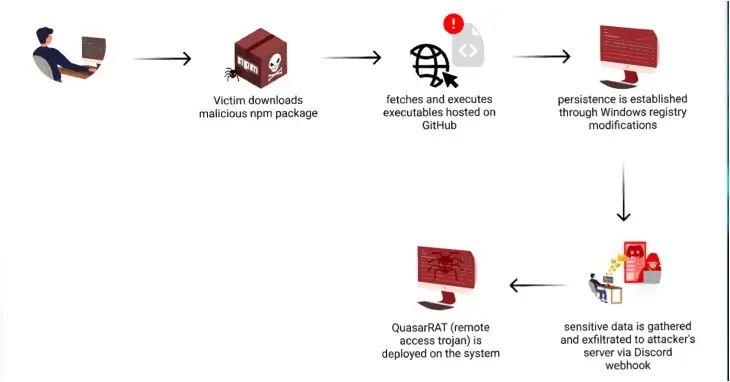
The malicious code embedded in the latest iteration acts as a gateway for serving additional payloads hosted on a GitHub repository, while simultaneously stealing Discord tokens, updating the Microsoft Defender Antivirus exclusion list to evade detection, and setting up persistence by means of a Windows Registry change.

“Central to the malware’s effectiveness is its approach to persistence, leveraging the Windows Settings app to ensure sustained access,” Gelb noted. “As a result, whenever a user attempts to open the Windows Settings app, the system inadvertently executes the malware instead.”
The end goal of the attack chain is the deployment of Quasar RAT granting the attacker remote control over the infected system. The harvested information is exfiltrated to the attacker’s command-and-control (C2) server using a Discord webhook.
The findings are an indication a steady stream of new packages continue to be published despite takedown efforts, making it essential that developers stay vigilant against the ongoing threat.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.


![[RANSOMHUB] - Ransomware Victim: www[.]black-star[.]fr 5 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)
