Microsoft Uncovers Critical Flaws in Rockwell Automation PanelView Plus
Microsoft has revealed two security flaws in Rockwell Automation PanelView Plus that could be weaponized by remote, unauthenticated attackers to execute arbitrary code and trigger a denial-of-service (DoS) condition.
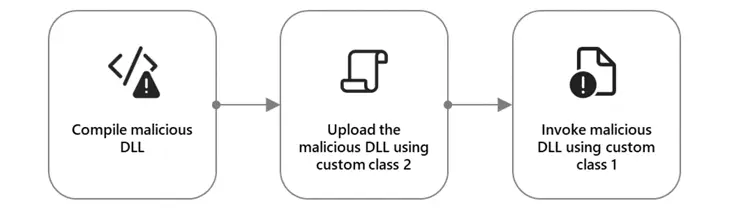
“The [remote code execution] vulnerability in PanelView Plus involves two custom classes that can be abused to upload and load a malicious DLL into the device,” security researcher Yuval Gordon said.
“The DoS vulnerability takes advantage of the same custom class to send a crafted buffer that the device is unable to handle properly, thus leading to a DoS.”
The list of shortcomings is as follows –
- CVE-2023-2071 (CVSS score: 9.8) – An improper input validation vulnerability that allows unauthenticated attackers to achieve remote code executed via crafted malicious packets.
- CVE-2023-29464 (CVSS score: 8.2) – An improper input validation vulnerability that allows an unauthenticated threat actor to read data from memory via crafted malicious packets and result in a DoS by sending a packet larger than the buffer size
Successful exploitation of the twin flaws permits an adversary to execute code remotely or lead to information disclosure or a DoS condition.
While CVE-2023-2071 impacts FactoryTalk View Machine Edition (versions 13.0, 12.0, and prior), CVE-2023-29464 affects FactoryTalk Linx (versions 6.30, 6.20, and prior).
It’s worth noting that advisories for the flaws were released by Rockwell Automation on September 12, 2023, and October 12, 2023, respectively. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) released its own alerts on September 21 and October 17.

The disclosure comes as unknown threat actors are believed to be exploiting a recently disclosed critical security flaw in HTTP File Server (CVE-2024-23692, CVSS score: 9.8) to deliver cryptocurrency miners and trojans such as Xeno RAT, Gh0st RAT, and PlugX.
The vulnerability, described as a case of template injection, allows a remote, unauthenticated attacker to execute arbitrary commands on the affected system by sending a specially crafted HTTP request.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.



![[INCRANSOM] - Ransomware Victim: statesideseattle[.]com 3 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)