Millions of GoDaddy customer data compromised in breach
Domain name registrar giant and hosting provider GoDaddy yesterday disclosed to the Securities and Exchange Commission (SEC) that it had suffered a security breach.
In the notice, it explained it had been compromised via an “unauthorized third-party access to our Managed WordPress hosting environment.” The unknown culprit behind the attack stole up to 1.2 million active and inactive customer data, including email addresses, original WordPress admin passwords, Secure File Transfer Protocol (sFTP) and database credentials, and SSL private keys.
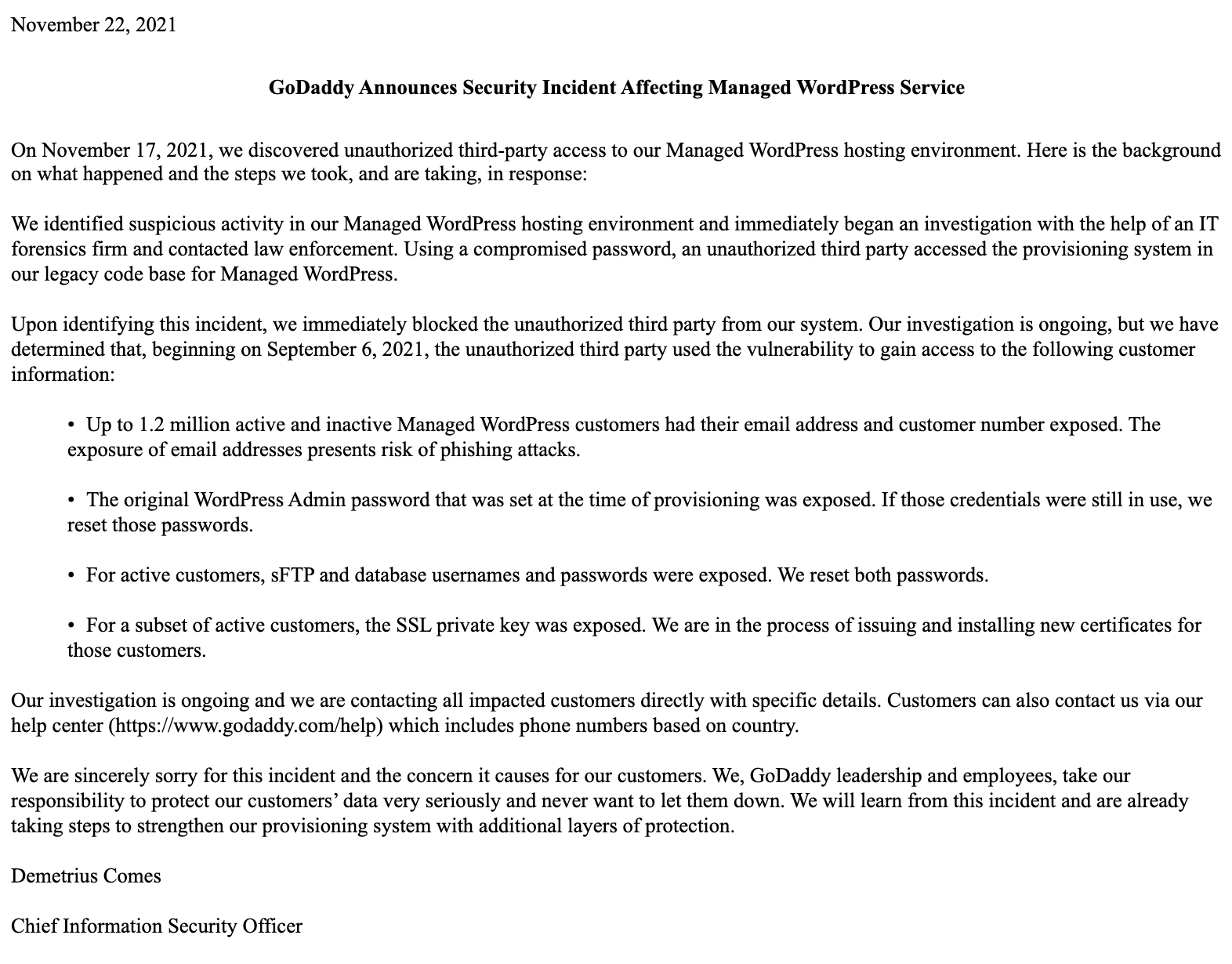
The company said it has taken measures to secure accounts and the environment, such as resetting passwords and blocking the unauthorised third-party from accessing its system, and said it will be issuing new certificates for specific customers.
GoDaddy first detected suspicious activity in its Managed WordPress hosting environment on Wednesday last week. According to initial investigations, the intruder used a compromised password to access legacy code in GoDaddy’s environment to steal data. Investigations are ongoing.
“We are sincerely sorry for this incident and the concern it causes for our customers,” wrote Demetrius Comes, GoDaddy’s Chief Information Security Officer (CISO), “We, GoDaddy leadership and employees, take our responsibility to protect our customers’ data very seriously and never want to let them down. We will learn from this incident and are already taking steps to strengthen our provisioning system with additional layers of protection.”
According to researchers from Defiant Inc, developers of Wordfence—a plugin for securing WordPress sites—GoDaddy has been handling sFTP in a way that doesn’t follow standard practices: “It appears that GoDaddy was storing sFTP credentials either as plaintext, or in a format that could be reversed into plaintext. They did this rather than using a salted hash, or a public key, both of which are considered industry best practices for sFTP. This allowed an attacker direct access to password credentials without the need to crack them.”
GoDaddy customer? Here’s what to do
If you use GoDaddy’s hosting service and are unsure if your account might be one of those affected, do not leave this to chance. Act now before someone takes the opportunity to take over your account.
GoDaddy has provided a good list of steps to take to lock down an account that might be potentially compromised:
- Change your password and your PIN
- Enable two-factor authentication (2FA) if you haven’t already
- Change the payment methods you have stored in your account, and delete those you don’t use. It would also be good to keep an eye on your bank account transactions and be ready to flag those that are fraudulent.
- Remove delegate access for anyone you’ve allowed into your account
- Remove any unknown API keys by deleting them.
- Verify your domain contact information is correct to avoid someone taking it over
- Remotely log out of your GoDaddy account, which will sign you out of all devices and browsers.
Stay safe!
The post Millions of GoDaddy customer data compromised in breach appeared first on Malwarebytes Labs.
If you like the site, please consider joining the telegram channel or supporting us on Patreon using the button below.


