Mirai DDoS malware variant expands targets with 13 router exploits
A Mirai-based DDoS (distributed denial of service) malware botnet tracked as IZ1H9 has added thirteen new payloads to target Linux-based routers and routers from D-Link, Zyxel, TP-Link, TOTOLINK, and others.
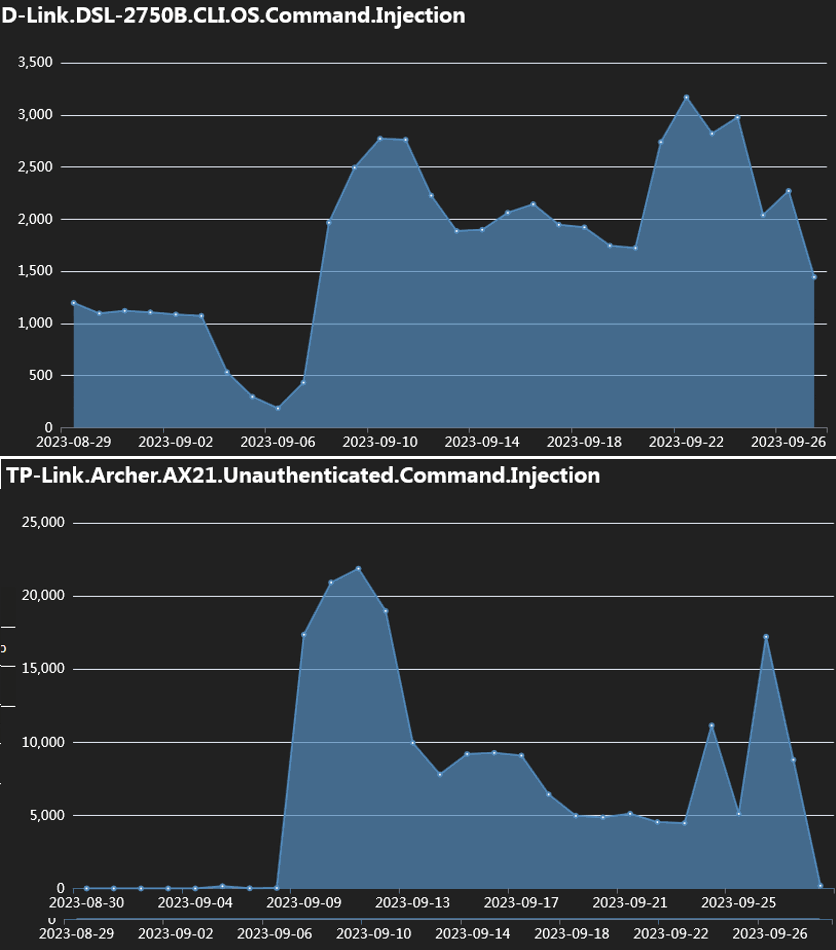
Fortinet researchers report observing a peak in the exploitation rates around the first week of September, reaching tens of thousands of exploitation attempts against vulnerable devices.
IZ1H9 compromises devices to enlist them to its DDoS swarm and then launches DDoS attacks on specified targets, presumably on the order of clients renting its firepower.
Extensive IoT targeting
The more devices and vulnerabilities targeted by a DDoS malware increased the potential to build a large and powerful botnet capable of delivering massive blows against websites.
In the case of IZ1H9, Fortinet reports it uses exploits for the following flaws, dating from 2015 to 2023:
- D-Link devices: CVE-2015-1187, CVE-2016-20017, CVE-2020-25506, CVE-2021-45382
- Netis WF2419: CVE-2019-19356
- Sunhillo SureLine (versions before 8.7.0.1.1): CVE-2021-36380
- Geutebruck products: CVE-2021-33544, CVE-2021-33548, CVE-2021-33549, CVE-2021-33550, CVE-2021-33551, CVE-2021-33552, CVE-2021-33553, CVE-2021-33554
- Yealink Device Management (DM) 3.6.0.20: CVE-2021-27561, CVE-2021-27562
- Zyxel EMG3525/VMG1312 (before V5.50): CVE not specified but targets the Zyxel device’s /bin/zhttpd/ component vulnerability
- TP-Link Archer AX21 (AX1800): CVE-2023-1389
- Korenix JetWave wireless AP: CVE-2023-23295
- TOTOLINK routers: CVE-2022-40475, CVE-2022-25080, CVE-2022-25079, CVE-2022-25081, CVE-2022-25082, CVE-2022-25078, CVE-2022-25084, CVE-2022-25077, CVE-2022-25076, CVE-2022-38511, CVE-2022-25075, CVE-2022-25083
The campaign also targets an unspecified CVE related to the “/cgi-bin/login.cgi” route, potentially affecting the Prolink PRC2402M router.
Attack chain
After exploiting one of the aforementioned CVEs, an IZ1H9 payload is injected into the device containing a command to fetch a shell script downloader named “l.sh” from a specified URL.
Upon execution, the script deletes logs to hide the malicious activity, and next, it fetches bot clients tailored for different system architectures.
Finally, the script modifies the device’s iptables rules to obstruct connection on specific ports and make it harder to remove the malware from the device.
Having done all the above, the bot establishes communication with the C2 (command and control) server and waits for commands to execute.
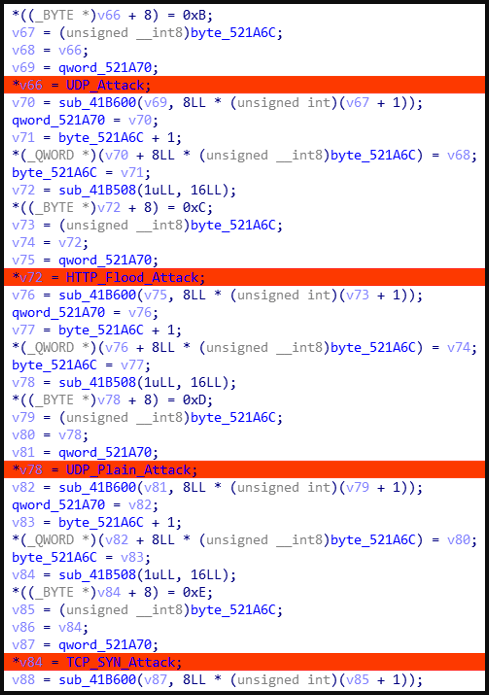
The supported commands concern the type of DDoS attack to launch, including UDP, UDP Plain, HTTP Flood, and TCP SYN.
Fortinet also reports that IZ1H9 features a data section with hardcoded credentials used for brute-force attacks.
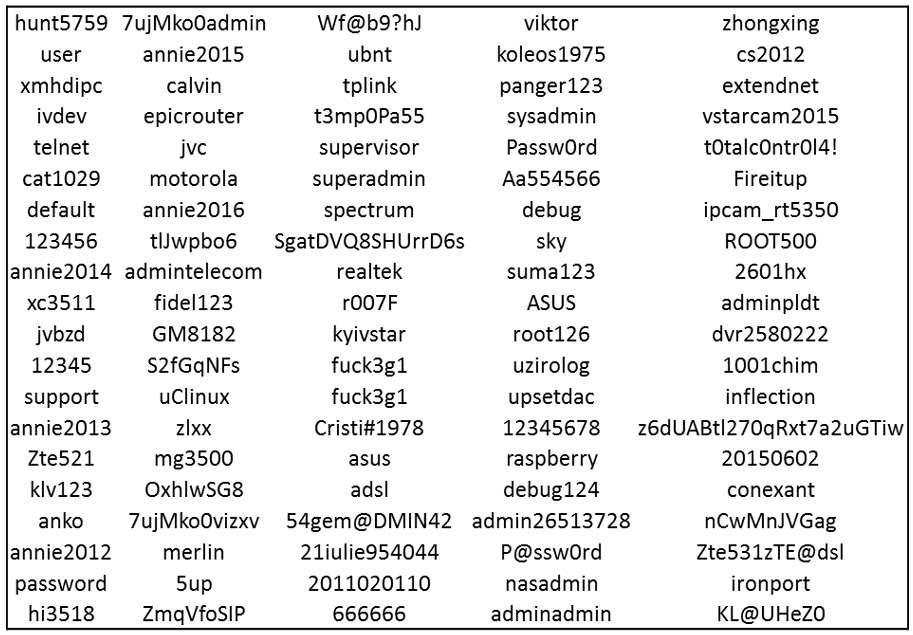
These attacks might be helpful for propagation to adjacent devices or authenticating to IoTs for which it does not have a working exploit.
Owners of IoT devices are recommended to use strong admin user credentials, update them to the latest available firmware version, and, if possible, reduce their exposure to the public internet.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.

