Monti ransomware targets VMware ESXi servers with new Linux locker

The Monti ransomware gang has returned, after a two-month break from publishing victims on their data leak site, using a new Linux locker to target VMware ESXi servers, legal, and government organizations.
Researchers at Trend Micro analyzing the new encryption tool from Monti found that it has “significant deviations from its other Linux-based predecessors.”
New Linux locker
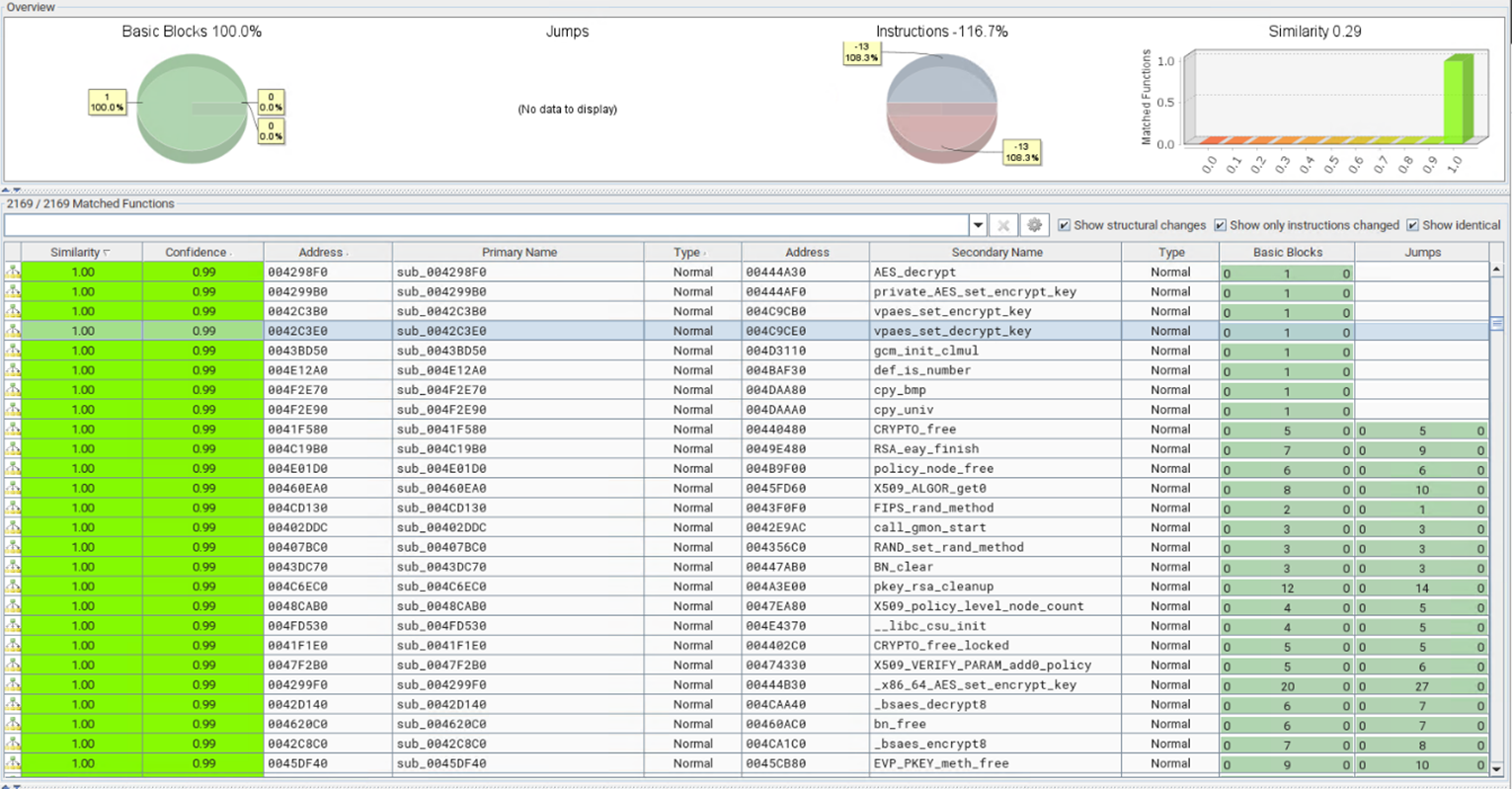
Previous versions of the Monti locker were heavily based (99%) on the leaked code from Conti ransomware but the similarities in the new locker are just 29%.
Among the significant modifications that Trend Micro observed are the following:
- Removal of the ‘–size,’ ‘–log,’ and ‘–vmlist’ parameters and addition of a new ‘-type=soft’ parameter to terminate ESXi virtual machines (VMs) in a subtler manner that is more likely to evade detection.
- Addition of a ‘–whitelist’ parameter to instruct the locker to skip specific ESXi virtual machines (VMs) on the host.
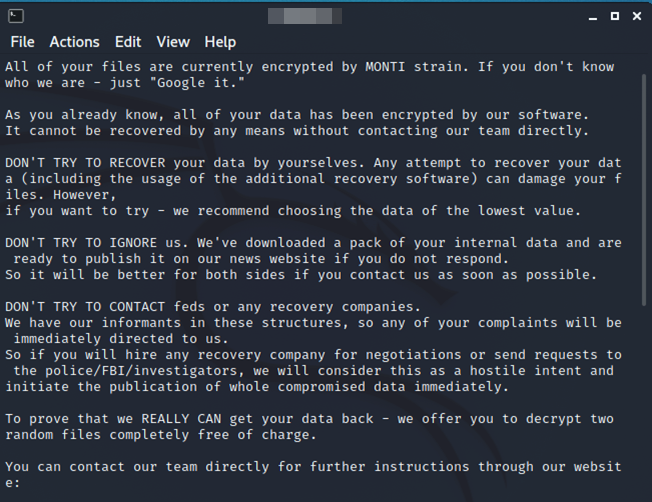
- Modification of ‘/etc/motd’ and ‘index.html’ files to display the ransom note content upon user login (Message of the Day).
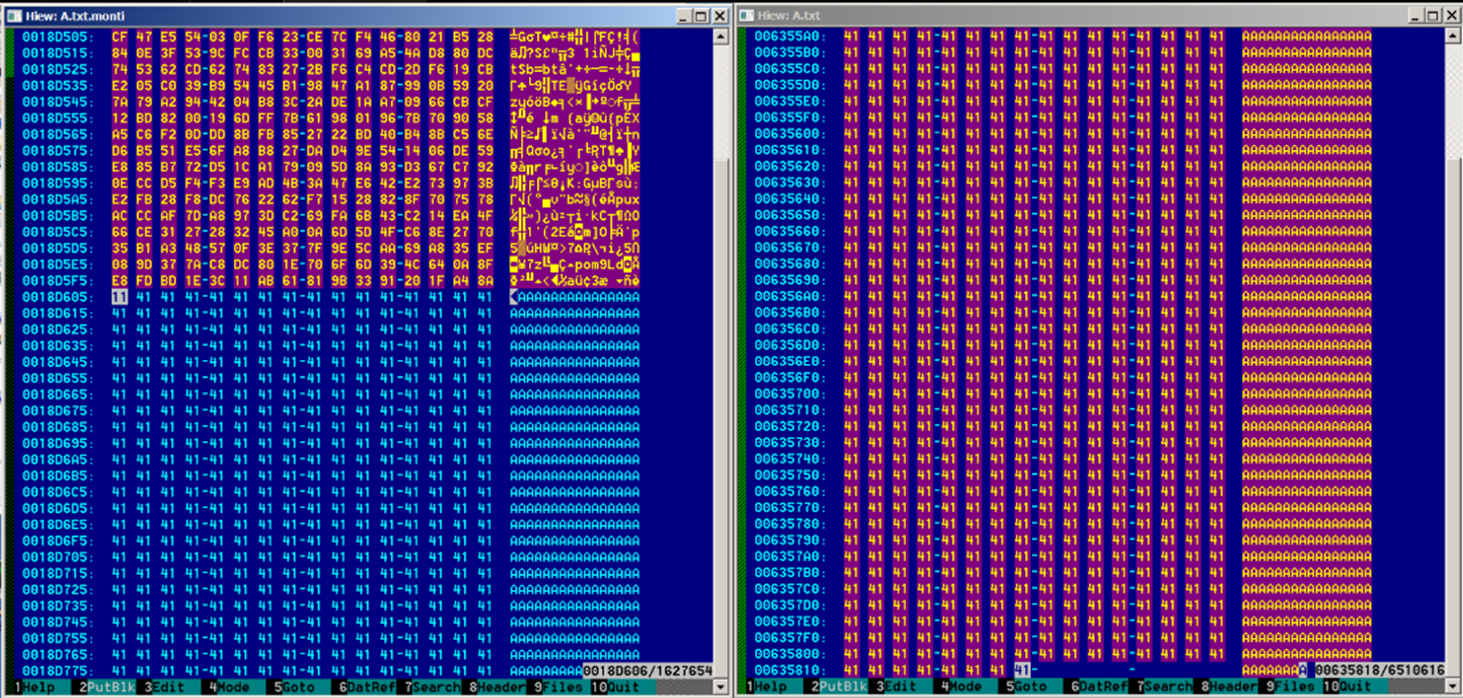
- Now appends the byte signature “MONTI” along with an additional 256 bytes related to the encryption key to the encrypted files.
- Checks if the file size is below or over 261 bytes, encrypts smaller files, and checks for the presence of the “MONTI” string on larger. If the string is missing, it encrypts the files.
- The new variant uses the AES-256-CTR encryption method from the OpenSSL library, unlike the previous variant, which used Salsa20.
- Files of sizes between 1.048MB and 4.19MB will have only the first 100,000 bytes encrypted, while files smaller than 1.048MB are wholly encrypted.
- Files exceeding the size of 4.19MB will have a portion of their content encrypted, calculated by a Shift Right operation.
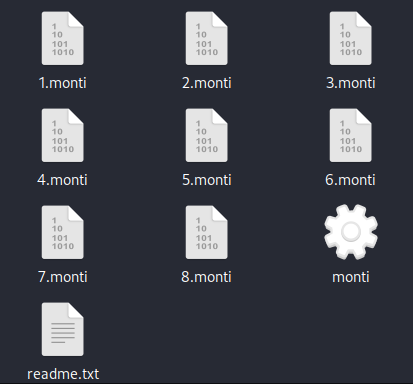
- The new variant adds the .MONTI extension to encrypted files and generates a ransom note (‘readme.txt’) on every directory it processes.
One of the highlights in the code, the researchers say, is its improved ability to evade detection, which makes it more difficult to identify and mitigate Monti ransomware attacks.
Monti ransomware background
First spotted by MalwareHunterTeam in June 2022 and documented publicly by BlackBerry a month later, Monti ransomware appeared as a clone of Conti, as it used most of its code following a leak from a Ukrainian researcher.
In September 2022, an Intel471 report highlighted the increased likelihood of Monti being a rebrand of Conti based on their identical initial network access methods.
However, due to the relatively low attack volume, the threat actor did not attract too much attention from researchers, with only one report by Fortinet in January 2023 that provides a cursory examination of their Linux locker.
Members of the gang do not consider themselves cybercriminals or their software malicious. They refer to the tools they use as utilities that reveal security problems in corporate networks, and call their attacks penetration testing, for which they want to get paid. If the victim company does not pay, they publish the name of their victims on their data leak site, under a section called “Wall of Shame.”
Despite the terms used to describe their activity, the Monti group behaves like any other ransomware gang, breaching company network, stealing data, and asking for a ransom.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.

![[AKIRA] - Ransomware Victim: Hometown Credit Union 6 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)


