New GoBruteforcer malware targets phpMyAdmin, MySQL, FTP, Postgres

A newly discovered Golang-based botnet malware scans for and infects web servers running phpMyAdmin, MySQL, FTP, and Postgres services.
According to researchers with Palo Alto Networks’ Unit 42, who first spotted it in the wild and dubbed it GoBruteforcer, the malware is compatible with x86, x64, and ARM architectures.
GoBruteforcer will brute force accounts with weak or default passwords to hack into vulnerable *nix devices.
“For successful execution, the samples require special conditions on the victim system like specific arguments being used and targeted services already being installed (with weak passwords),” the researchers said.
For each targeted IP address, the malware starts scanning for phpMyAdmin, MySQL, FTP, and Postgres services. After detecting an open port accepting connections, it will attempt to log in using hard-coded credentials.
Once in, it deploys an IRC bot on compromised phpMyAdmin systems or a PHP web shell on servers running other targeted services.
In the next phase of the attack, GoBruteforcer will reach out to its command-and-control server and wait for instructions that will be delivered via the previously installed IRC bot or web shell.
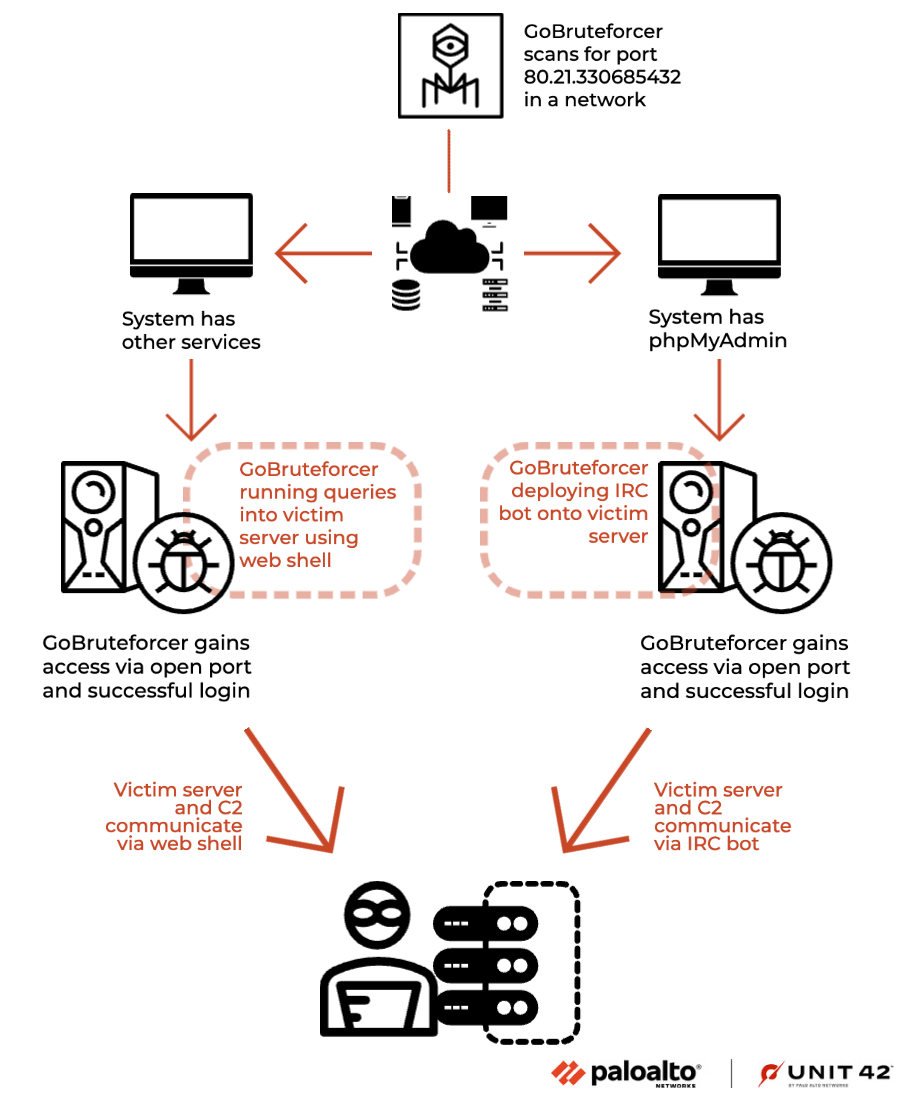
The botnet uses a multiscan module to find potential victims within a Classless Inter-Domain Routing (CIDR), granting it a broad selection of targets to infiltrate networks.
Before scanning for IP addresses to attack, GoBruteforcer chooses a CIDR block and will target all IP addresses within that range.
Rather than targeting a single IP, the malware uses CIDR block scanning for access to a diverse range of hosts on various IP addresses, increasing the reach of the attack.
GoBruteforcer is likely under active development, with its operators expected to adapt their tactics and the malware’s capabilities for targeting web servers and stay ahead of security defenses.
“We’ve seen this malware remotely deploy a variety of different types of malware as payloads, including coinminers,” Unit42 added.
“We believe that GoBruteforcer is in active development, and as such, things like initial infection vectors or payloads could change in the near future.”
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below


To keep up to date follow us on the below channels.






![[DRAGONFORCE] - Ransomware Victim: Pratt Homes 10 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)