New Mfa Bypassing Phishing Kit Targets Microsoft 365 Gmail Accounts
Cybercriminals have been increasingly using a new phishing-as-a-service (PhaaS) platform named ‘Tycoon 2FA’ to target Microsoft 365 and Gmail accounts and bypass two-factor authentication (2FA) protection.
Tycoon 2FA was discovered by Sekoia analysts in October 2023 during routine threat hunting, but it has been active since at least August 2023, when the Saad Tycoon group offered it through private Telegram channels.
The PhaaS kit shares similarities with other adversary-in-the-middle (AitM) platforms, such as Dadsec OTT, suggesting possible code reuse or a collaboration between developers.
In 2024, Tycoon 2FA released a new version that is stealthier, indicating a continuous effort to improve the kit. Currently, the service leverages 1,100 domains and has been observed in thousands of phishing attacks.
Tycoon 2FA attacks
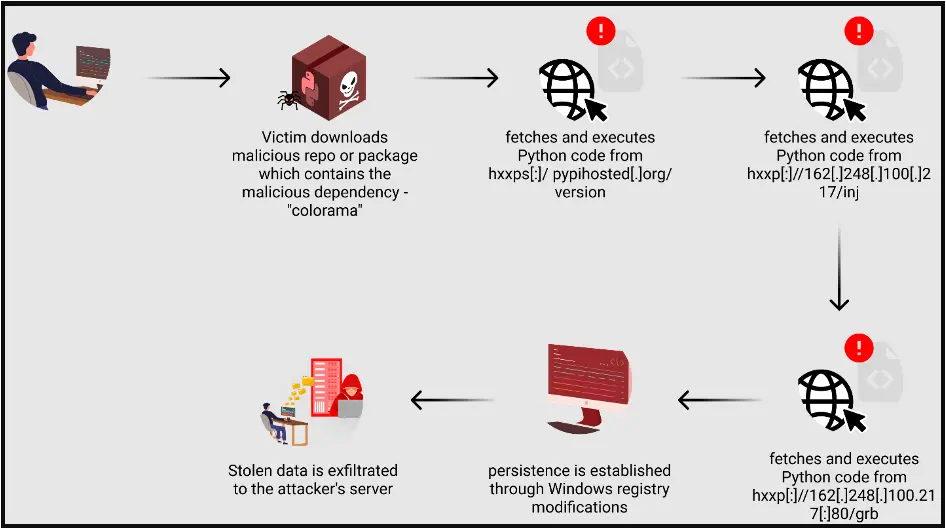
Tycoon 2FA attacks involve a multi-step process where the threat actor steals session cookies by using a reverse proxy server hosting the phishing web page, which intercepts the victim’s input and relays them to the legitimate service.
“Once the user completes the MFA challenge, and the authentication is successful, the server in the middle captures session cookies,” Skoia explains. This way, the attacker can replay a user’s session and bypass multi-factor authentication (MFA) mechanisms.
Sekoia’s report describes the attacks in seven distinct stages as described below:
- Stage 0 – Attackers distribute malicious links via emails with embedded URLs or QR codes, tricking victims into accessing phishing pages.
- Stage 1 – A security challenge (Cloudflare Turnstile) filters out bots, allowing only human interactions to proceed to the deceptive phishing site.
- Stage 2 – Background scripts extract the victim’s email from the URL to customize the phishing attack.
- Stage 3 – Users are quietly redirected to another part of the phishing site, moving them closer to the fake login page.
- Stage 4 – This stage presents a fake Microsoft login page to steal credentials, using WebSockets for data exfiltration.
- Stage 5 – The kit mimics a 2FA challenge, intercepting the 2FA token or response to bypass security measures.
- Stage 6 – Finally, victims are directed to a legitimate-looking page, obscuring the phishing attack’s success.
An overview of the attack is described with the diagram below, which includes all the steps of the process.
Evolution and scale
Sekoia reports that the latest version of the Tycoon 2FA phishing kit, released this year, has introduced significant modifications that improve the phishing and evasion capabilities.
Key changes include updates to the JavaScript and HTML code, alterations in the order of resource retrieval, and more extensive filtering to block traffic from bots and analytical tools.
For example, the kit now delays loading malicious resources until after the Cloudflare Turnstile challenge is resolved, using pseudorandom names for URLs to obscure its activities.
Also, Tor network traffic or IP addresses linked to data centers are now better identified, while traffic is rejected based on specific user-agent strings.
Regarding the scale of operations, Sekoia reports that it’s substantial, as there’s evidence of a broad user base of cybercriminals currently utilizing Tycoon 2FA for phishing operations.
The Bitcoin wallet linked to the operators has recorded over 1,800 transactions since October 2019, with a notable increment starting August 2023, when the kit was launched.
Over 530 transactions were over $120, which is the entry price for a 10-day phishing link. By mid-March 2024, the threat actors’ wallet had received a total of $394,015 worth of cryptocurrency.
Tycoon 2FA is just a recent addition to a PhaaS space that already offers cybercriminals plenty of options. Other notable platforms that can bypass 2FA protections include LabHost, Greatness, and Robin Banks.
For a list of the indicators of compromise (IoCs) linked to the Tycoon 2FA operation, Sekoia makes available a repository with over 50 entries.
