New Zero-Day Flaw in Apache OFBiz ERP Allows Remote Code Execution
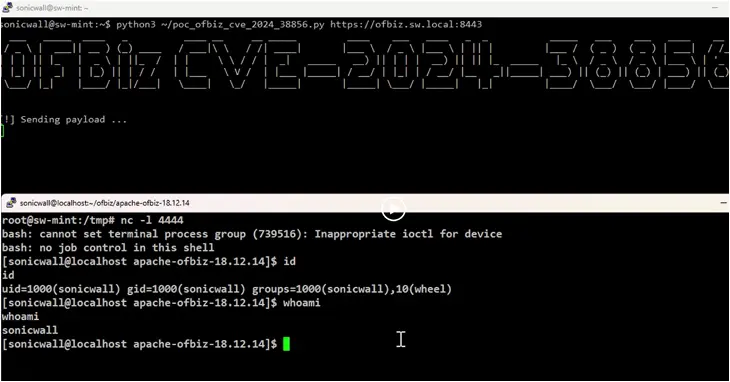
A new zero-day pre-authentication remote code execution vulnerability has been disclosed in the Apache OFBiz open-source enterprise resource planning (ERP) system that could allow threat actors to achieve remote code execution on affected instances.
Tracked as CVE-2024-38856, the flaw has a CVSS score of 9.8 out of a maximum of 10.0. It affects Apache OFBiz versions prior to 18.12.15.
“The root cause of the vulnerability lies in a flaw in the authentication mechanism,” SonicWall, which discovered and reported the shortcoming, said in a statement.
“This flaw allows an unauthenticated user to access functionalities that generally require the user to be logged in, paving the way for remote code execution.”
CVE-2024-38856 is also a patch bypass for CVE-2024-36104, a path traversal vulnerability that was addressed in early June with the release of 18.12.14.
SonicWall described the flaw as residing in the override view functionality that exposes critical endpoints to unauthenticated threat actors, who could leverage it to achieve remote code execution via specially crafted requests.
“Unauthenticated access was allowed to the ProgramExport endpoint by chaining it with any other endpoints that do not require authentication by abusing the override view functionality,” security researcher Hasib Vhora said.

The development comes as another critical path traversal vulnerability in OFBiz that could result in remote code execution (CVE-2024-32113) has since come under active exploitation to deploy the Mirai botnet. It was patched in May 2024.
In December 2023, SonicWall also disclosed a then-zero-day flaw in the same software (CVE-2023-51467) that made it possible to bypass authentication protections. It was subsequently subjected to a large number of exploitation attempts.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.



![[KAIROS] - Ransomware Victim: usarice[.]com 5 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)