North Korea’s ScarCruft Deploys RokRAT Malware via LNK File Infection Chains
The North Korean threat actor known as ScarCruft began experimenting with oversized LNK files as a delivery route for RokRAT malware as early as July 2022, the same month Microsoft began blocking macros across Office documents by default.
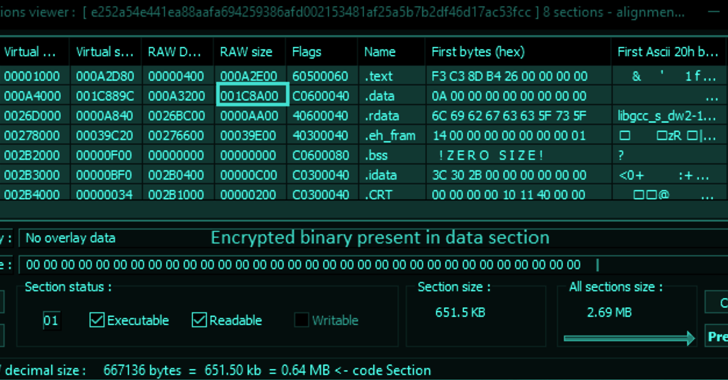
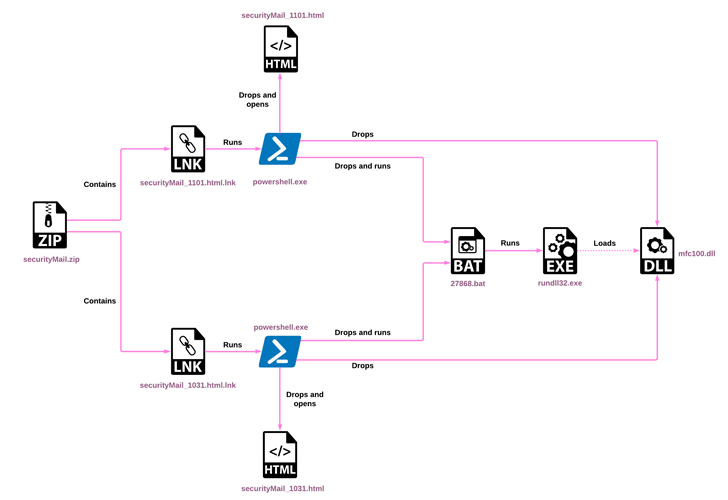
“RokRAT has not changed significantly over the years, but its deployment methods have evolved, now utilizing archives containing LNK files that initiate multi-stage infection chains,” Check Point said in a new technical report.
“This is another representation of a major trend in the threat landscape, where APTs and cybercriminals alike attempt to overcome the blocking of macros from untrusted sources.”
ScarCruft, also known by the names APT37, InkySquid, Nickel Foxcroft, Reaper, RedEyes, and Ricochet Chollima, is a threat group that almost exclusively targets South Korean individuals and entities as part of spear-phishing attacks designed to deliver an array of custom tools.
The adversarial collective, unlike the Lazarus Group or Kimsuky, is overseen by North Korea’s Ministry of State Security (MSS), which is tasked with domestic counterespionage and overseas counterintelligence activities, per Mandiant.
The group’s primary malware of choice is RokRAT (aka DOGCALL), which has since been adapted to other platforms such as macOS (CloudMensis) and Android (RambleOn), indicating that the backdoor is being actively developed and maintained.
RokRAT and its variants are equipped to carry out a wide range of activities like credential theft, data exfiltration, screenshot capture, system information gathering, command and shellcode execution, and file and directory management.
The collected information, some of which is stored in the form of MP3 files to cover its tracks, is sent back using cloud services like Dropbox, Microsoft OneDrive, pCloud and Yandex Cloud in a bid to disguise the command-and-control (C2) communications as legitimate.
Other bespoke malware used by the group include, but not limited to, Chinotto, BLUELIGHT, GOLDBACKDOOR, Dolphin, and, most recently, M2RAT. It’s also known to use commodity malware such as Amadey, a downloader that can receive commands from the attacker to download additional malware, in a bid to confuse attribution.
The use of LNK files as decoys to activate the infection sequences was also highlighted by the AhnLab Security Emergency Response Center (ASEC) last week, with the files containing PowerShell commands that deploy the RokRAT malware.
While the change in modus operandi signals ScarCruft’s endeavors to keep up with the shifting threat ecosystem, it has continued to leverage macro-based malicious Word documents as recently as April 2023 to drop the malware, mirroring a similar chain that was reported by Malwarebytes in January 2021.
Join our webinar and learn how to stop ransomware attacks in their tracks with real-time MFA and service account protection.
Save My Seat!Another attack wave observed at the beginning of November 2022, according to the Israeli cybersecurity company, employed ZIP archives incorporating LNK files to deploy the Amadey malware.
“[The LNK file] method can trigger an equally effective infection chain by a simple double click, one that is more reliable than n-day exploits or the Office macros which require additional clicks to launch,” Check Point said.
“APT37 continues to pose a considerable threat, launching multiple campaigns across the platforms and significantly improving its malware delivery methods.”
The findings come as Kaspersky disclosed a new Go-based malware developed by ScarCruft codenamed SidLevel that utilizes the cloud messaging service Ably as a C2 mechanism for the first time and comes with “extensive capabilities to steal sensitive information from victims.”
“The group continues to target individuals related to North Korea, including novelists, academic students, and also business people who appear to send funds back to North Korea,” the Russian cybersecurity firm noted in its APT Trends Report for Q1 2023.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below


To keep up to date follow us on the below channels.





![[INCRANSOM] - Ransomware Victim: State Bar of Texas (www[.]texasbar[.]com) 7 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)