Malware Analysis – babuk – f1dd01a9e4b959e569250354d74e0423
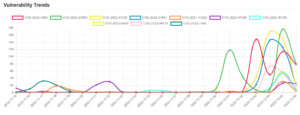
Score: 10 MALWARE FAMILY: babukTAGS:family:babuk, ransomwareMD5: f1dd01a9e4b959e569250354d74e0423SHA1: 7e2e524fd33261449571f1334868b17ef46e550dANALYSIS DATE: 2022-12-07T11:03:13ZTTPS: T1012, T1082, T1107, T1490, T1120 ScoreMeaningExample10Known badA malware family was...





![[TRYHACKME] - Void Execution Challenge 8 void_execution](https://www.redpacketsecurity.com/wp-content/uploads/2025/09/void_execution-150x150.png)














![LockBit 3.0 Ransomware Victim: myersontooth[.]com 40 image-11](https://www.redpacketsecurity.com/wp-content/uploads/2022/06/image-11-300x142.png)
![[QILIN] - Ransomware Victim: Sai Mai Hospital 42 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)
