Porch-Pirate – The Most Comprehensive Postman Recon / OSINT Client And Framework That Facilitates The Automated Discovery And Exploitation Of API Endpoints And Secrets Committed To Workspaces, Collections, Requests, Users And Teams
Porch Pirate started as a tool to quickly uncover Postman secrets, and has slowly begun to evolve into a multi-purpose reconaissance / OSINT framework for Postman. While existing tools are great proof of concepts, they only attempt to identify very specific keywords as “secrets”, and in very limited locations, with no consideration to recon beyond secrets. We realized we required capabilities that were “secret-agnostic”, and had enough flexibility to capture false-positives that still provided offensive value.
Porch Pirate enumerates and presents sensitive results (global secrets, unique headers, endpoints, query parameters, authorization, etc), from publicly accessible Postman entities, such as:
- Workspaces
- Collections
- Requests
- Users
- Teams
Installation
python3 -m pip install porch-pirateUsing the client
The Porch Pirate client can be used to nearly fully conduct reviews on public Postman entities in a quick and simple fashion. There are intended workflows and particular keywords to be used that can typically maximize results. These methodologies can be located on our blog: Plundering Postman with Porch Pirate.
Porch Pirate supports the following arguments to be performed on collections, workspaces, or users.
--globals--collections--requests--urls--dump--raw--curl
Simple Search
porch-pirate -s "coca-cola.com"Get Workspace Globals
By default, Porch Pirate will display globals from all active and inactive environments if they are defined in the workspace. Provide a -w argument with the workspace ID (found by performing a simple search, or automatic search dump) to extract the workspace’s globals, along with other information.
porch-pirate -w abd6bded-ac31-4dd5-87d6-aa4a399071b8Dump Workspace
When an interesting result has been found with a simple search, we can provide the workspace ID to the -w argument with the --dump command to begin extracting information from the workspace and its collections.
porch-pirate -w abd6bded-ac31-4dd5-87d6-aa4a399071b8 --dumpAutomatic Search and Globals Extraction
Porch Pirate can be supplied a simple search term, following the --globals argument. Porch Pirate will dump all relevant workspaces tied to the results discovered in the simple search, but only if there are globals defined. This is particularly useful for quickly identifying potentially interesting workspaces to dig into further.
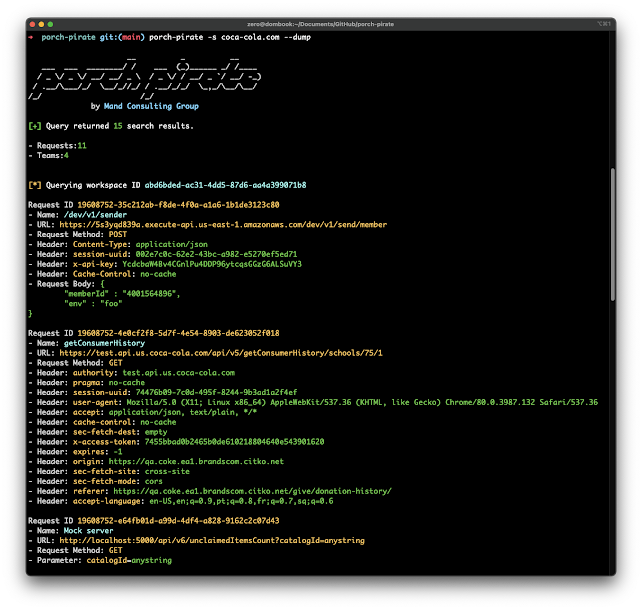
porch-pirate -s "shopify" --globalsAutomatic Search Dump
Porch Pirate can be supplied a simple search term, following the --dump argument. Porch Pirate will dump all relevant workspaces and collections tied to the results discovered in the simple search. This is particularly useful for quickly sifting through potentially interesting results.
porch-pirate -s "coca-cola.com" --dumpExtract URLs from Workspace
A particularly useful way to use Porch Pirate is to extract all URLs from a workspace and export them to another tool for fuzzing.
porch-pirate -w abd6bded-ac31-4dd5-87d6-aa4a399071b8 --urlsAutomatic URL Extraction
Porch Pirate will recursively extract all URLs from workspaces and their collections related to a simple search term.
porch-pirate -s "coca-cola.com" --urlsShow Collections in a Workspace
porch-pirate -w abd6bded-ac31-4dd5-87d6-aa4a399071b8 --collectionsShow Workspace Requests
porch-pirate -w abd6bded-ac31-4dd5-87d6-aa4a399071b8 --requestsShow raw JSON
porch-pirate -w abd6bded-ac31-4dd5-87d6-aa4a399071b8 --rawShow Entity Information
porch-pirate -w WORKSPACE_IDporch-pirate -c COLLECTION_IDporch-pirate -r REQUEST_IDporch-pirate -u USERNAME/TEAMNAMEConvert Request to Curl
Porch Pirate can build curl requests when provided with a request ID for easier testing.
porch-pirate -r 11055256-b1529390-18d2-4dce-812f-ee4d33bffd38 --curlUse a proxy
porch-pirate -s coca-cola.com --proxy 127.0.0.1:8080Using as a library
Searching
p = porchpirate()
print(p.search('coca-cola.com'))Get Workspace Collections
p = porchpirate()
print(p.collections('4127fdda-08be-4f34-af0e-a8bdc06efaba'))Dumping a Workspace
p = porchpirate()
collections = json.loads(p.collections('4127fdda-08be-4f34-af0e-a8bdc06efaba'))
for collection in collections['data']:
requests = collection['requests']
for r in requests:
request_data = p.request(r['id'])
print(request_data)Grabbing a Workspace’s Globals
p = porchpirate()
print(p.workspace_globals('4127fdda-08be-4f34-af0e-a8bdc06efaba'))Other Examples
Other library usage examples can be located in the examples directory, which contains the following examples:
dump_workspace.pyformat_search_results.pyformat_workspace_collections.pyformat_workspace_globals.pyget_collection.pyget_collections.pyget_profile.pyget_request.pyget_statistics.pyget_team.pyget_user.pyget_workspace.pyrecursive_globals_from_search.pyrequest_to_curl.pysearch.pysearch_by_page.pyworkspace_collections.py
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.