Ransomware gangs abuse Process Explorer driver to kill security software

Threat actors use a new hacking tool dubbed AuKill to disable Endpoint Detection & Response (EDR) Software on targets’ systems before deploying backdoors and ransomware in Bring Your Own Vulnerable Driver (BYOVD) attacks.
In such attacks, malicious actors drop legitimate drivers signed with a valid certificate and capable of running with kernel privileges on the victims’ devices to disable security solutions and take over the system.
This technique is popular among various threat actors, from state-backed hacking groups to financially-motivated ransomware gangs.
The AuKill malware, first spotted by Sophos X-Ops security researchers, drops a vulnerable Windows driver (procexp.sys) next to the one used by Microsoft’s Process Explorer v16.32. This is a very popular and legitimate utility that helps collect information on active Windows processes.
To escalate privileges, it first checks if it’s already running with SYSTEM privileges, and if not, it impersonates the TrustedInstaller Windows Modules Installer service to escalate to SYSTEM.
To disable security software, AuKill starts several threads to continuously probe and disable security processes and services (and ensure they remain disabled by preventing them from restarting).
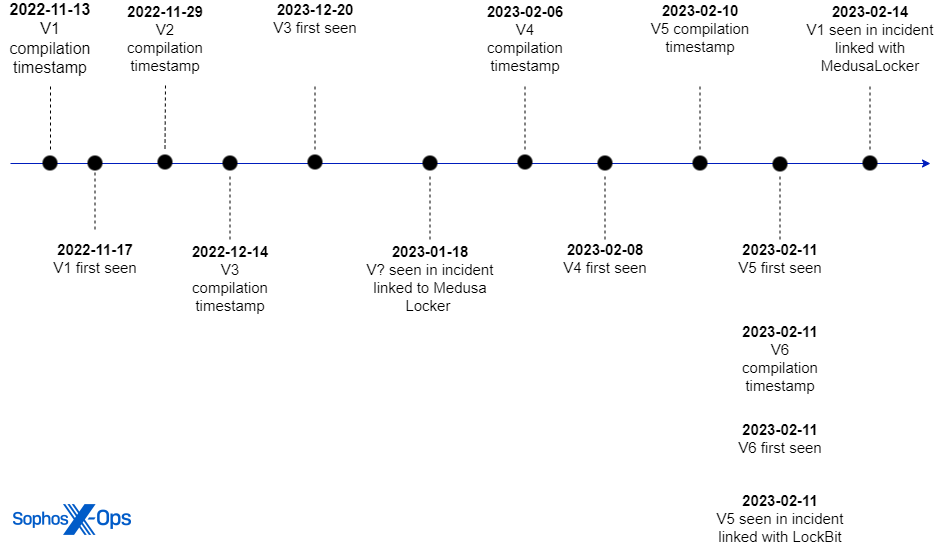
So far, multiple AuKill versions have been observed in the wild, some deployed in at least three separate incidents that have led to Medusa Locker and LockBit ransomware infections since the start of the year.
“The tool was used during at least three ransomware incidents since the beginning of 2023 to sabotage the target’s protection and deploy the ransomware,” Sophos X-Ops said.
“In January and February, attackers deployed Medusa Locker ransomware after using the tool; in February, an attacker used AuKill just prior to deploying Lockbit ransomware.”
AuKill is similar to an open-source tool called Backstab, which also uses a Process Explorer driver to disable security solutions running on compromised devices.
Backstab was previously deployed by the LockBit gang in at least one attack observed by Sophos X-Ops while analyzing the cybercrime group’s latest malware version, LockBit 3.0 or LockBit Black.
“We have found multiple similarities between the open-source tool Backstab and AuKill,” the researchers said.
“Some of these similarities include similar, characteristic debug strings, and nearly identical code flow logic to interact with the driver.”
The oldest AuKill sample has a November 2022 compilation timestamp, while the newest was compiled in mid-February when it was also used as part of an attack linked to the LockBit ransomware group.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below


To keep up to date follow us on the below channels.





