Researchers Shed Light on CatB Ransomware’s Evasion Techniques
The threat actors behind the CatB ransomware operation have been observed using a technique called DLL search order hijacking to evade detection and launch the payload.
CatB, also referred to as CatB99 and Baxtoy, emerged late last year and is said to be an “evolution or direct rebrand” of another ransomware strain known as Pandora based on code-level similarities.
It’s worth noting that the use of Pandora has been attributed to Bronze Starlight (aka DEV-0401 or Emperor Dragonfly), a China-based threat actor that’s known to employ short-lived ransomware families as a ruse to likely conceal its true objectives.
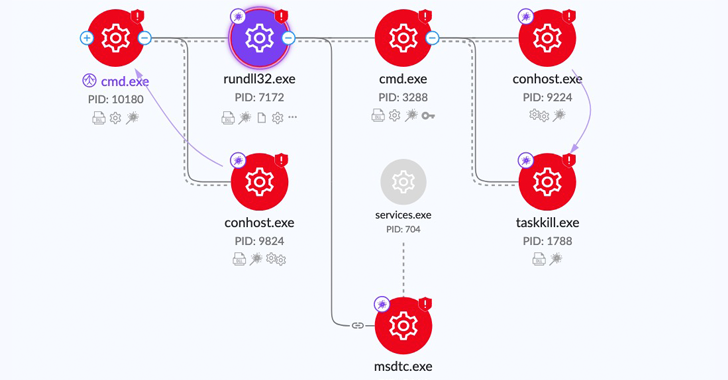
One of the key defining characteristics of CatB is its reliance on DLL hijacking via a legitimate service called Microsoft Distributed Transaction Coordinator (MSDTC) to extract and launch the ransomware payload.
“Upon execution, CatB payloads rely on DLL search order hijacking to drop and load the malicious payload,” SentinelOne researcher Jim Walter said in a report published last week. “The dropper (versions.dll) drops the payload (oci.dll) into the System32 directory.”
The dropper is also responsible for carrying out anti-analysis checks to determine if the malware is being executed within a virtual environment, and ultimately abusing the MSDTC service to inject the rogue oci.dll containing the ransomware into the msdtc.exe executable upon system restart.
“The [MSDTC] configurations changed are the name of the account under which the service should run, which is changed from Network Service to Local System, and the service start option, which is changed from Demand start to Auto start for persistency if a restart occurs,” Minerva Labs researcher Natalie Zargarov explained in a previous analysis.
One striking aspect of the ransomware is its absence of a ransom note. Instead, each encrypted file is updated with a message urging the victims to make a Bitcoin payment.
Are you aware of the risks associated with third-party app access to your company’s SaaS apps? Join our webinar to learn about the types of permissions being granted and how to minimize risk.
RESERVE YOUR SEATAnother trait is the malware’s ability to harvest sensitive data such as passwords, bookmarks, history from web browsers Google Chrome, Microsoft Edge (and Internet Explorer), and Mozilla Firefox.
“CatB joins a long line of ransomware families that embrace semi-novel techniques and atypical behaviors such as appending notes to the head of files,” Walter said. “These behaviors appear to be implemented in the interest of detection evasion and some level of anti-analysis trickery.”
This is not the first time the MSDTC service has been weaponized for malicious purposes. In May 2021, Trustwave disclosed a novel malware dubbed Pingback that leveraged the same technique to achieve persistence and bypass security solutions.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below


To keep up to date follow us on the below channels.